Ransom.Win32.BURAN.B
a variant of Win32/Filecoder.Buran.H trojan(Nod32)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %User Temp%{Generated Hash}.zeppelin
- %Application Data%{Random Name of Running Process} - copy of itself
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- notepad.exe - executed with injected code to delete original malware file
- %Application Data%{Random Name of Running Process} - agent {No. of drives}
- net stop "Acronis VSS Provider" /y;
- net stop "Enterprise Client Service" /y;
- net stop "SQL Backups" /y;
- net stop "SQLsafe Backup Service" /y;
- net stop "SQLsafe Filter Service" /y;
- net stop "Sophos Agent" /y;
- net stop "Sophos AutoUpdate Service" /y;
- net stop "Sophos Clean Service" /y;
- net stop "Sophos Device Control Service" /y;
- net stop "Sophos File Scanner Service" /y;
- net stop "Sophos Health Service" /y;
- net stop "Sophos MCS Agent" /y;
- net stop "Sophos MCS Client" /y;
- net stop "Sophos Message Router" /y;
- net stop "Sophos Safestore Service" /y;
- net stop "Sophos System Protection Service" /y;
- net stop "Sophos Web Control Service" /y;
- net stop "Symantec System Recovery" /y;
- net stop "Veeam Backup Catalog Data Service" /y;
- net stop "Zoolz 2 Service" /y;
- net stop ARSM /y;
- net stop AVP /y;
- net stop AcrSch2Svc /y;
- net stop AcronisAgent /y;
- net stop Antivirus /y;
- net stop BackupExecAgentAccelerator /y;
- net stop BackupExecAgentBrowser /y;
- net stop BackupExecDeviceMediaService /y;
- net stop BackupExecJobEngine /y;
- net stop BackupExecManagementService /y;
- net stop BackupExecRPCService /y;
- net stop BackupExecVSSProvider /y;
- net stop DCAgent /y;
- net stop EPSecurityService /y;
- net stop EPUpdateService /y;
- net stop ESHASRV /y;
- net stop EhttpSrv /y;
- net stop EraserSvc11710 /y;
- net stop EsgShKernel /y;
- net stop FA_Scheduler /y;
- net stop IISAdmin /y;
- net stop IMAP4Svc /y;
- net stop KAVFS /y;
- net stop KAVFSGT /y;
- net stop MBAMService /y;
- net stop MBEndpointAgent /y;
- net stop MMS /y;
- net stop MSExchangeES /y;
- net stop MSExchangeIS /y;
- net stop MSExchangeMGMT /y;
- net stop MSExchangeMTA /y;
- net stop MSExchangeSA /y;
- net stop MSExchangeSRS /y;
- net stop MSOLAP$SQL_2008 /y;
- net stop MSOLAP$SYSTEM_BGC /y;
- net stop MSOLAP$TPS /y;
- net stop MSOLAP$TPSAMA /y;
- net stop MSSQL$BKUPEXEC /y;
- net stop MSSQL$ECWDB2 /y;
- net stop MSSQL$PRACTICEMGT /y;
- net stop MSSQL$PRACTTICEBGC /y;
- net stop MSSQL$PROD /y;
- net stop MSSQL$PROFXENGAGEMENT /y;
- net stop MSSQL$SBSMONITORING /y;
- net stop MSSQL$SHAREPOINT /y;
- net stop MSSQL$SOPHOS /y;
- net stop MSSQL$SQLEXPRESS /y;
- net stop MSSQL$SQL_2008 /y;
- net stop MSSQL$SYSTEM_BGC /y;
- net stop MSSQL$TPS /y;
- net stop MSSQL$TPSAMA /y;
- net stop MSSQL$VEEAMSQL2008R2 /y;
- net stop MSSQL$VEEAMSQL2008R2 /y;
- net stop MSSQL$VEEAMSQL2012 /y;
- net stop MSSQLFDLauncher /y;
- net stop MSSQLFDLauncher$PROFXENGAGEMENT /y;
- net stop MSSQLFDLauncher$SBSMONITORING /y;
- net stop MSSQLFDLauncher$SHAREPOINT /y;
- net stop MSSQLFDLauncher$SQL_2008 /y;
- net stop MSSQLFDLauncher$SYSTEM_BGC /y;
- net stop MSSQLFDLauncher$TPS /y;
- net stop MSSQLFDLauncher$TPSAMA /y;
- net stop MSSQLSERVER /y;
- net stop MSSQLServerADHelper /y;
- net stop MSSQLServerADHelper100 /y;
- net stop MSSQLServerOLAPService /y;
- net stop McAfeeEngineService /y;
- net stop McAfeeFramework /y;
- net stop McAfeeFrameworkMcAfeeFramework /y;
- net stop McShield /y;
- net stop McTaskManager /y;
- net stop MsDtsServer /y;
- net stop MsDtsServer100 /y;
- net stop MsDtsServer110 /y;
- net stop MySQL57 /y;
- net stop MySQL80 /y;
- net stop NetMsmqActivator /y;
- net stop OracleClientCache80 /y;
- net stop PDVFSService /y;
- net stop POP3Svc /y;
- net stop RESvc /y;
- net stop ReportServer /y;
- net stop ReportServer$SQL_2008 /y;
- net stop ReportServer$SYSTEM_BGC /y;
- net stop ReportServer$TPS /y;
- net stop ReportServer$TPSAMA /y;
- net stop SAVAdminService /y;
- net stop SAVService /y;
- net stop SDRSVC /y;
- net stop SMTPSvc /y;
- net stop SNAC /y;
- net stop SQLAgent$BKUPEXEC /y;
- net stop SQLAgent$CITRIX_METAFRAME /y;
- net stop SQLAgent$CXDB /y;
- net stop SQLAgent$ECWDB2 /y;
- net stop SQLAgent$PRACTTICEBGC /y;
- net stop SQLAgent$PRACTTICEMGT /y;
- net stop SQLAgent$PROD /y;
- net stop SQLAgent$PROFXENGAGEMENT /y;
- net stop SQLAgent$SBSMONITORING /y;
- net stop SQLAgent$SHAREPOINT /y;
- net stop SQLAgent$SOPHOS /y;
- net stop SQLAgent$SQLEXPRESS /y;
- net stop SQLAgent$SQL_2008 /y;
- net stop SQLAgent$SYSTEM_BGC /y;
- net stop SQLAgent$TPS /y;
- net stop SQLAgent$TPSAMA /y;
- net stop SQLAgent$VEEAMSQL2008R2 /y;
- net stop SQLAgent$VEEAMSQL2008R2 /y;
- net stop SQLAgent$VEEAMSQL2012 /y;
- net stop SQLBrowser /y;
- net stop SQLSERVERAGENT /y;
- net stop SQLSafeOLRService /y;
- net stop SQLTELEMETRY /y;
- net stop SQLTELEMETRY$ECWDB2 /y;
- net stop SQLWriter /y;
- net stop SamSs /y;
- net stop SepMasterService /y;
- net stop ShMonitor /y;
- net stop SmcService /y;
- net stop Smcinst /y;
- net stop SntpService /y;
- net stop SstpSvc /y;
- net stop TmCCSF /y;
- net stop TrueKey /y;
- net stop TrueKeyScheduler /y;
- net stop TrueKeyServiceHelper /y;
- net stop UI0Detect /y;
- net stop VeeamBackupSvc /y;
- net stop VeeamBrokerSvc /y;
- net stop VeeamCatalogSvc /y;
- net stop VeeamCloudSvc /y;
- net stop VeeamDeploySvc /y;
- net stop VeeamDeploymentService /y;
- net stop VeeamEnterpriseManagerSvc /y;
- net stop VeeamHvIntegrationSvc /y;
- net stop VeeamMountSvc /y;
- net stop VeeamNFSSvc /y;
- net stop VeeamRESTSvc /y;
- net stop VeeamTransportSvc /y;
- net stop W3Svc /y;
- net stop WRSVC /y;
- net stop bedbg /y;
- net stop ekrn /y;
- net stop kavfsslp /y;
- net stop klnagent /y;
- net stop macmnsvc /y;
- net stop masvc /y;
- net stop mfefire /y;
- net stop mfemms /y;
- net stop mfevtp /y;
- net stop mozyprobackup /y;
- net stop msftesql$PROD /y;
- net stop ntrtscan /y;
- net stop sacsvr /y;
- net stop sophossps /y;
- net stop svcGenericHost /y;
- net stop swi_filter /y;
- net stop swi_service /y;
- net stop swi_update /y;
- net stop swi_update_64 /y;
- net stop tmlisten /y;
- net stop wbengine /y;
- net stop wbengine /y;
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Other System Modifications
This Ransomware adds the following registry keys:
HKEY_CURRENT_USER\Software\Zeppelin
Process = {random string}
HKEY_CURRENT_USER\Software\Zeppelin
Knock = 666
HKEY_CURRENT_USER\Software\Zeppelin\
Keys
Public Key = {public key}
HKEY_CURRENT_USER\Software\Zeppelin\
Keys
Encrypted Private Key = {encrypted private key}
HKEY_CURRENT_USER\Software\Zeppelin\
Paths
Creates one for every drive. Value is equal to 0-{No. of drives} = {random string}
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
%Application Data%{Random Name of Running Process} = "{Random Name of Running Process}" -start;
Other Details
This Ransomware connects to the following URL(s) to get the affected system's IP address:
- geoiptool.com
- gedatatool.com
- iplogger.com
It does the following:
- It terminates itself if found to be running in a machine from the following countries:
- Ukraine
- Belorussia
- Kazakhstan
- Russian Federation
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- boot.ini
- bootfont.bin
- bootsect.bak
- desktop.ini
- ctfmon.exe
- iconcache.db
- master.exe
- master.dat
- ntdetect.com
- ntldr
- ntuser.dat
- ntuser.dat.log
- ntuser.ini
- thumbs.db
- !!! ALL YOUR FILES ARE ENCRYPTED !!!.TXT
- .cmd
- .com
- .cpl
- .dll
- .msc
- .msp
- .pif
- .scr
- .sys
- .log
- .lnk
- .bat
It avoids encrypting files found in the following folders:
- $RECYCLE.BIN\
- :\$Windows.~bt\
- :\RECYCLER
- :\System Volume Information\
- :\Windows.old\
- :\Windows\
- :\intel\
- :\nvidia\
- :\inetpub\logs\
- \All Users\
- \AppData\
- \Apple Computer\Safari\
- \Application Data\
- \Boot\
- \Google\
- \Google\Chrome\
- \Mozilla Firefox\
- \Mozilla\
- \Opera Software\
- \Opera\
- \Tor Browser\
- \Common Files\
- \Internet Explorer\
- \Windows Defender\
- \Windows Mail\
- \Windows Media Player\
- \Windows Multimedia Platform\
- \Windows NT\
- \Windows Photo Viewer\
- \Windows Portable Devices\
- \WindowsPowerShell\
- \Windows Photo Viewer\
- \Windows Security\
- \Embedded Lockdown Manager\
- \Windows Journal\
- \MSBuild\
- \Reference Assemblies\
- \Windows Sidebar\
- \Windows Defender Advanced Threat Protection\
- \Microsoft\
- \Package Cache\
- \Microsoft Help\
It appends the following extension to the file name of the encrypted files:
- {original name}.{Unique ID}
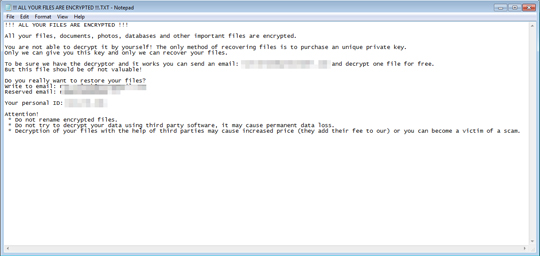
It leaves text files that serve as ransom notes containing the following text:
- !!! ALL YOUR FILES ARE ENCRYPTED !!!.txt
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
-
Troj.Win32.TRX.XXPE50FFF033
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- HKEY_CURRENT_USER\Software\Zeppelin
Step 5
Search and delete this file
- %Application Data%{Random Name of Running Process}
Step 6
Scan your computer with your Trend Micro product to delete files detected as Ransom.Win32.BURAN.B. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 7
Restore encrypted files from backup.
Did this description help? Tell us how we did.


