Ransom.Linux.TRIGONA.THCBBBC
UDS:Trojan-Ransom.Linux.Agent.a (KASPERSKY)
Linux


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Information Theft
This Ransomware gathers the following data:
- Computer ID
- Computer Name
- Host Name
- Boot time
- Machine ID
- Processor Architecture
- OS version
- Local Disk Information
- Keyboard Lists
- Main Language
- System User
- Workgroup
Other Details
This Ransomware does the following:
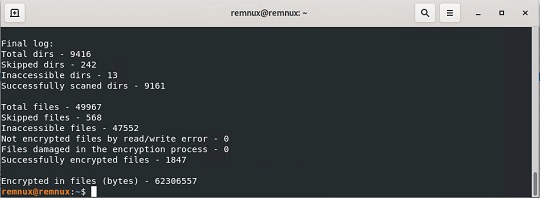
- It displays the following on the terminal after encrypting files:
It accepts the following parameters:
- /full ← Encrypts full content of files
- /test_cid ← Specifies the Computer ID to use
- /test_vid ← Specifies the Victim ID to use
- /p or /path ← Specifies the path to recursively encrypt
- /erase ← Overwrite files with NULL bytes, appends "._erased" extension and deletes it.
- /is_testing ← Sets the testing flag (Must be used with /test_cid and /test_vid)
- /shdwn ← Shuts down the system
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file path:
- /proc/
- /sys/
- /run/
- /dev/
- /lib/
- /lib64/
- /bin/
- /sbin/
- /boot/
- /etc/
- /share/
- systemd
- kernel
It renames encrypted files using the following names:
- {Random Characters}._locked
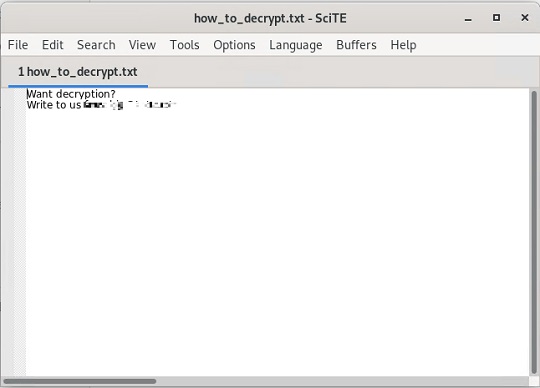
It drops the following file(s) as ransom note:
- \tmp\how_to_decrypt.txt
- {Encrypted Directory}\how_to_decrypt.txt
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- Troj.ELF.TRX.XXELFC1DFF029
Step 2
Scan your computer with your Trend Micro product to delete files detected as Ransom.Linux.TRIGONA.THCBBBC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


