PDF_MALPHISH.AUSJEQYE
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users. It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It steals email account information.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Information Theft
This Trojan steals email account information.
Stolen Information
This Trojan sends the gathered information via HTTP POST to the following URL:
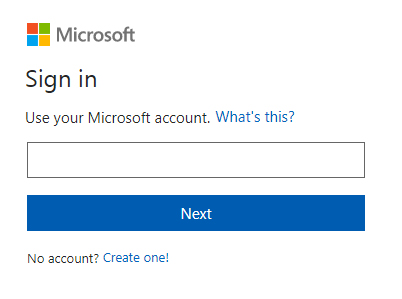
- Office365:
Username - http://{BLOCKED}editltd.com/lusada/onedrv/365/step2.php
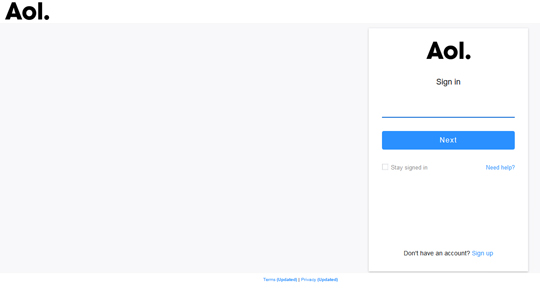
Password - http://{BLOCKED}editltd.com/lusada/onedrv/365/next.php - AOL:
Username - http://{BLOCKED}editltd.com/lusada/onedrv/aoluser/index1.php
Password - http://{BLOCKED}editltd.com/lusada/onedrv/aoluser/aollogs.php - Google:
Username - http://{BLOCKED}editltd.com/lusada/onedrv/gmail/wmed.php
Password - http://{BLOCKED}editltd.com/lusada/onedrv/gmail/wmz.php - Other:
Username and Password - http://{BLOCKED}editltd.com/lusada/onedrv/other/next3.php
Other Details
This Trojan does the following:
- This Trojan presents the user a fake message tricking them to click on the following link:
http://{BLOCKED}editltd.com/lusada/onedrv/index.htm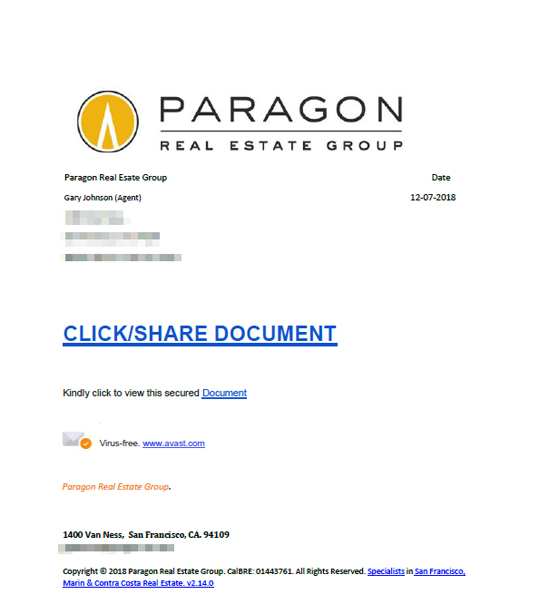
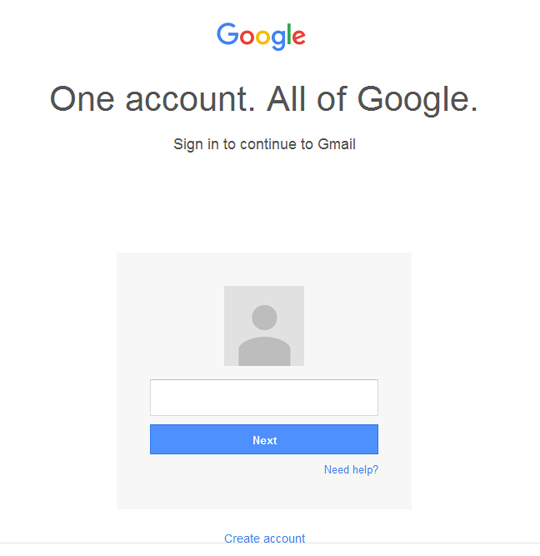
- Clicking on the URL displays this webpage:
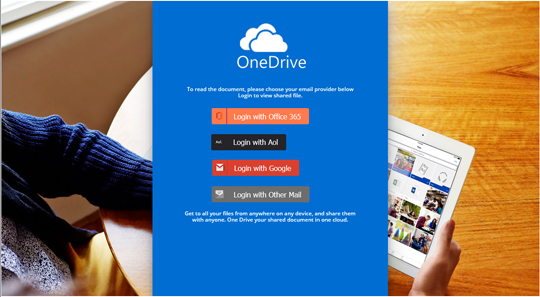
- Choosing an email provider from the webpage will redirect you to the following URL(s):
- http://{BLOCKED}editltd.com/lusada/onedrv/365/index.php
- http://{BLOCKED}editltd.com/lusada/onedrv/aoluser/index.htm
- http://{BLOCKED}editltd.com/lusada/onedrv/gmail/index.htm
- http://{BLOCKED}editltd.com/lusada/onedrv/other/index.htm
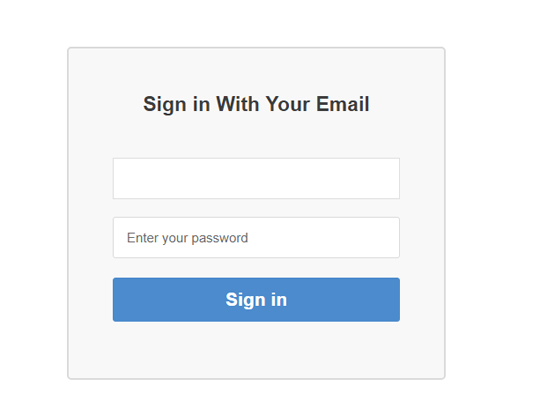
- Spoofed login pages are shown for each email providers:
- Office365:
- AOL:
- Google:
- Other:
- Office365:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as PDF_MALPHISH.AUSJEQYE. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


