HKTL_PDFPASS
Trojan-Clicker.Win32.Agent.syp (Kaspersky); Mal/Generic-L (Sophos); Trojan.Win32.Clicker!BT (Sunbelt); Trojan horse Generic9_c.BXAZ (AVG)
Windows 2000, Windows XP, Windows Server 2003,Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any propagation routine.
It does not have any backdoor routine.
It does not have any downloading capability.
TECHNICAL DETAILS
Arrival Details
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This hacking tool creates the following folders:
- %User Temp%\ns{random}.tmp -temporarily created during installation
- %User Temp%\NSISUtils
- {selected path of installation}
- %Start Menu%\Programs\{selected name of application}
- %Program Files%\ElcomSoft
- %Program Files%\ElcomSoft\Common Files
- %User Temp%\NirCMD
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.. %Start Menu% is the current user's Start Menu folder, which is usually C:\Windows\Start Menu or C:\Documents and Settings\{User name}\Start Menu on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming\Microsoft\Windows\Start Menu on Windows Vista and 7.. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).)
Other System Modifications
This hacking tool adds the following registry keys:
HKEY_CURRENT_USER\Software\ElcomSoft
HKEY_CURRENT_USER\Software\ElcomSoft\
Advanced PDF Password Recovery
HKEY_CURRENT_USER\Software\ElcomSoft\
Advanced PDF Password Recovery\Language
HKEY_CURRENT_USER\Software\ElcomSoft\
Common Files
HKEY_LOCAL_MACHINE\SOFTWARE\ElcomSoft
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\App Paths\
apdfpr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Uninstall\
APDFPRP
HKEY_LOCAL_MACHINE\SOFTWARE\ElcomSoft\
Common Files
It adds the following registry entries as part of its installation routine:
HKEY_CURRENT_USER\Software\ElcomSoft\
Advanced PDF Password Recovery
InstallDir = "{selected path of installation}"
HKEY_CURRENT_USER\Software\ElcomSoft\
Advanced PDF Password Recovery\Language
FileName = "chinese.lng"
HKEY_CURRENT_USER\Software\ElcomSoft\
Common Files
Location = "%Program Files%\ElcomSoft\Common Files"
HKEY_CURRENT_USER\Software\ElcomSoft\
Common Files
{files located at %Program Files%\ElcomSoft\Common Files path}.counter = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\ElcomSoft\
Common Files
Location = "%Program Files%\ElcomSoft\Common Files"
HKEY_LOCAL_MACHINE\SOFTWARE\ElcomSoft\
Common Files
{files located at '%Program Files%\ElcomSoft\Common Files' path}.counter = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\App Paths\
apdfpr.exe
(Default) = "{selected path of installation}\apdfpr.exe"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Uninstall\
APDFPRP
NSIS:StartMenuDir = "{selected name of application}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Uninstall\
APDFPRP
DisplayName = "APDFPRP 5.02"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Uninstall\
APDFPRP
UninstallString = "{selected path of installation}\uninst.exe"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Uninstall\
APDFPRP
{other entries which serves as information} = "{other data which serves as information}"
HKEY_USERS\.DEFAULT\Software\
Common Files
Location = "%Program Files%\ElcomSoft\Common Files"
HKEY_USERS\.DEFAULT\Software\
Common Files
{files located at '%Program Files%\ElcomSoft\Common Files' path}.counter = "1"
Propagation
This hacking tool does not have any propagation routine.
Backdoor Routine
This hacking tool does not have any backdoor routine.
Dropping Routine
This hacking tool drops the following files:
- %User Temp%\ns{random}.tmp\installoptions.dll -temporarily created during installation
- %User Temp%\ns{random}.tmp\ioSpecial.ini -temporarily created during installation
- %User Temp%\ns{random}.tmp\left.bmp - temporarily created during installation
- %User Temp%\ns{random}.tmp\modern-header.bmp -will be deleted after installation
- %User Temp%\ns{random}.tmp\nsWeb.dll -temporarily created during installation
- %User Temp%\ns{random}.tmp\sobar.bmp -temporarily created during installation
- %User Temp%\ns{random}.tmp\system.dll -temporarily created during installation
- %User Temp%\ns{random}.tmp\baiduio.ini -temporarily created during installation
- %User Temp%\ns{random}.tmp\cnnic_small.bmp -temporarily created during installation
- %User Temp%\ns{random}.tmp\brandingurl.dll -temporarily created during installation
- %User Temp%\NSISUtils\nsisutils.dll
- %User Temp%\NSISUtils\DuringIn.GiF
- %System%\bassmod.dll
- {selected path of installation}\apdfpr.chm
- {selected path of installation}\apdfpr.exe - It is the main hacktool executable
- {selected path of installation}\chinese.lng
- {selected path of installation}\digits.chr
- {selected path of installation}\english.chr
- {selected path of installation}\english.dic
- {selected path of installation}\english.lng
- {selected path of installation}\file_id.diz
- {selected path of installation}\german.chr
- {selected path of installation}\german.dic
- {selected path of installation}\german.lng
- {selected path of installation}\GPUManager.exe
- {selected path of installation}\license.txt
- {selected path of installation}\order.txt
- {selected path of installation}\partner.xml
- {selected path of installation}\readme.txt
- {selected path of installation}\russian.chr
- {selected path of installation}\russian.dic
- {selected path of installation}\russian.lng
- {selected path of installation}\special.chr
- {selected path of installation}\uninst.exe
- {selected path of installation}\soft2cn{letters and chinese characters).exe
- {selected path of installation}\{chinese characters}
- {selected path of installation}\{chinese characters}
- {selected path of installation}\{chinese characters}.txt
- %Program Files%\ElcomSoft\Common Files\elcom_lang.xml
- %Program Files%\ElcomSoft\Common Files\elcom_partners.exml
- %Program Files%\ElcomSoft\Common Files\elcom_reg.dll
- %Program Files%\ElcomSoft\Common Files\elcom_xml.dll
- %Start Menu%\Programs\{selected name of application}\APDFPRP.LNK
- %Start Menu%\Programs\{selected name of application}\{chinese characters}.lnk
- %Start Menu%\Programs\{selected name of application}\{chinese characters}.lnk
- %Start Menu%\Programs\{selected name of application}\{chinese characters}.lnk
- %Desktop%\APDFPRP.LNK
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.. %System% is the Windows system folder, which is usually C:\Windows\System32.. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).. %Start Menu% is the current user's Start Menu folder, which is usually C:\Windows\Start Menu or C:\Documents and Settings\{User name}\Start Menu on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming\Microsoft\Windows\Start Menu on Windows Vista and 7.. %Desktop% is the current user's desktop, which is usually C:\Documents and Settings\{User Name}\Desktop on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\Desktop on Windows Vista and 7.)
Download Routine
This hacking tool does not have any downloading capability.
NOTES:
The default language of the hacktool is Chinese.
This primarily installs the following Hack Tool:
- Advanced PDF Password Recovery Pro 5.02
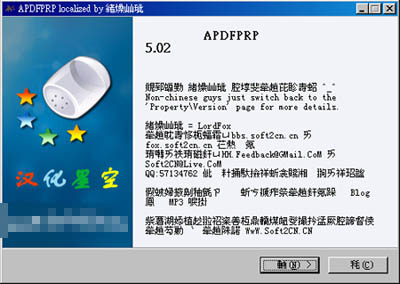
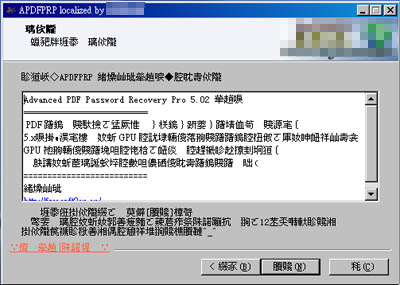
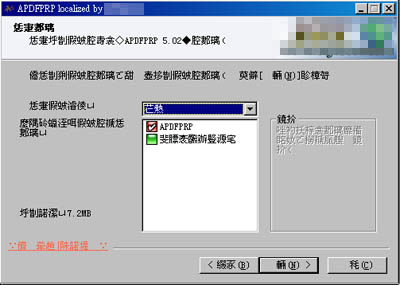
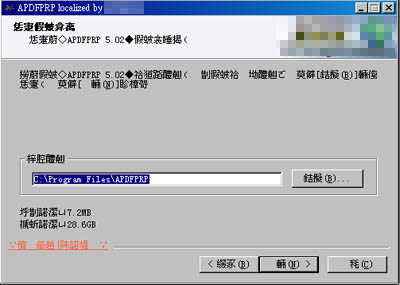
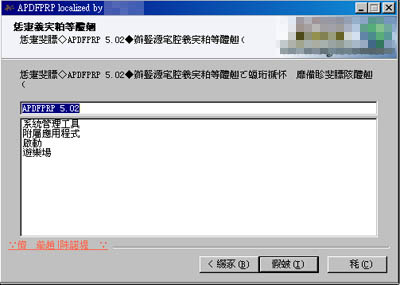
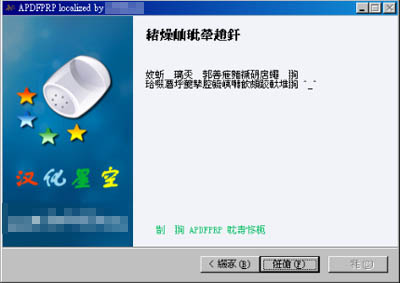
As part of installation, the following windows can be seen:
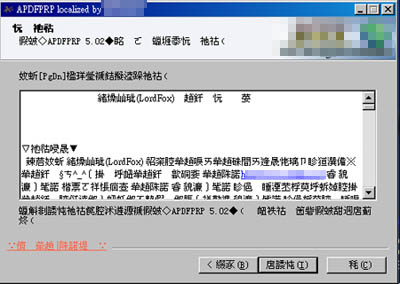
The variable {selected path of installation} where it will be installed is manually filled up in the following:
The variable {selected name of application} is filled up in the following:
The user may or may not accept to install additional offer by this hacktool on the tickmark(accept(by default)- checked/not accept- unchecked):

The add-on is a Baidu Bar.
The add-on creates the following directory:
- %Program Files%\Baidu
- %Program Files%\Baidu\bar
- %Program Files%\Baidu\bar\BDBar_tmp
- %Program Files%\Baidu\bar\img
- %Program Files%\Baidu\iexp
- {All Users' start menu}\Programs\{Chinese characters related to add-on: baidu super search bar}
The add-on drops the following files:
- %Program Files%\Baidu\bar\baidubar.dat
- %Program Files%\Baidu\bar\BaiduBar.dll
- %Program Files%\Baidu\bar\BDBar_tmp\BaiduBar.dll
- %Program Files%\Baidu\bar\img\imglist.bmp
- %Program Files%\Baidu\bar\img\logo.bmp
- %Program Files%\Baidu\iexp\bdsrhook.dll
- {All Users' start menu}\Programs\{Chinese characters related to add-on: baidu super search bar}\{Chinese character files}.url
It will add registry keys and entries as part of the installation to the add-on(if accepted by the user).
It will show the following at the last of installation:
The main hacktool executable has the following window:
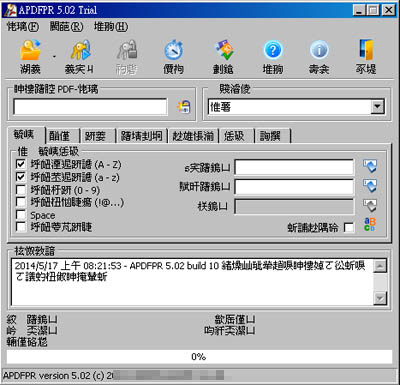
The hacktool can unlock restriction which protects the PDF documents through the following:
- Brute-Force
- Mask
- Dictionary
- Key search
It does not have rootkit capabilities.
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Remove HKTL_PDFPASS by using its own Uninstall option
Step 3
Restart in Safe Mode
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software
- ElcomSoft
- ElcomSoft
- In HKEY_LOCAL_MACHINE\SOFTWARE
- ElcomSoft
- ElcomSoft
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths
- apdfpr.exe
- apdfpr.exe
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
- APDFPRP
- APDFPRP
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_USERS\.DEFAULT\Software\Common Files
- Location = "%Program Files%\ElcomSoft\Common Files"
- Location = "%Program Files%\ElcomSoft\Common Files"
- In HKEY_USERS\.DEFAULT\Software\Common Files
- {files located at '%Program Files%\ElcomSoft\Common Files' path}.counter = "1"
- {files located at '%Program Files%\ElcomSoft\Common Files' path}.counter = "1"
Step 6
Search and delete these folders
- %User Temp%\ns{random}.tmp
- %User Temp%\NSISUtils
- {selected path of installation}
- %Start Menu%\Programs\{selected name of application}
- %Program Files%\ElcomSoft
- %User Temp%\NirCMD
- %Program Files%\Baidu
- {All Users' start menu}\Programs\{chinese characters related to add-on: baidu super search bar}
Step 7
Search and delete these files
- %Desktop%\APDFPRP.LNK
- %System%\bassmod.dll
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as HKTL_PDFPASS. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


