HackTool.Win32.Radmin.HA
RemoteAdmin.Win32.RDPWrap.b (KASPERSKY)
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Hacking Tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any propagation routine.
It does not have any backdoor routine.
TECHNICAL DETAILS
Arrival Details
This Hacking Tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Propagation
This Hacking Tool does not have any propagation routine.
Backdoor Routine
This Hacking Tool does not have any backdoor routine.
Rootkit Capabilities
This Hacking Tool does not have rootkit capabilities.
Other Details
This Hacking Tool does the following:
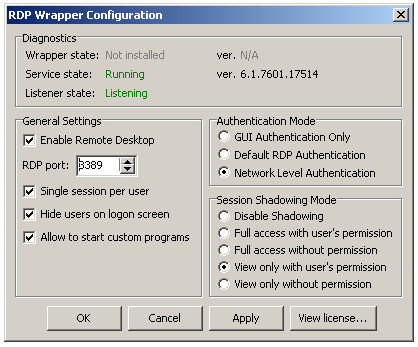
- It displays the following upon execution:
- It displays the following upon clicking View license button:
- It displays the following application information:
- Diagnostic:
- Wrapper state
- Service state
- Listener state
- App version
- It has the following functions:
- It executes the following command to add a new rule named "Remote Destop" and changes the local port from default value (TCP port 3389) to user specified port.
- netsh advfirewall firewall set rule name="Remote Desktop" new localport={User Specified Port}
- General Settings:
- Enable Remote Destop
- RDP port selection
- Single session per user
- Hide users on logon screen
- Allow to start custom programs
- Authentication Mode:
- GUI Authentication Only
- Default RDP Authentication
- Network Level Authentication
- Session Shadowing Mode:
- Disable Shadowing
- Full access with user's permission
- Full access without permission
- View only with user's permission
- View only without permission
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Scan your computer with your Trend Micro product to delete files detected as HackTool.Win32.Radmin.HA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


