TROJ_RANSOM.EWQ
Windows 2000, XP, Server 2003


Threat Type: Trojan
Destructiveness: Yes
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan deletes itself after execution.
TECHNICAL DETAILS
Installation
This Trojan drops the following non-malicious file:
- %Desktop%\HOW TO DECRYPT FILES.txt
(Note: %Desktop% is the current user's desktop, which is usually C:\Windows\Profiles\{user name}\Desktop on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Desktop on Windows NT, and C:\Documents and Settings\{User Name}\Desktop on Windows 2000, XP, and Server 2003.)
Other Details
This Trojan does the following:
- Searches for the following files types in all drives:
- .jpg
- .jpeg
- .psd
- .cdr
- .dwg
- .max
- .mov
- .m2v
- .3gp
- .doc
- .docx
- .xls
- .xlsx
- .ppt
- .pptx
- .rar
- .zip
- .mdb
- .mp3
- .cer
- .p12
- .pfx
- .kwm
- .pwm
- .txt
- .avi
- .flv
- .lnk
- .bmp
- .1cd
- .md
- .mdf
- .dbf
- .mdb
- .odt
- .vob
- .ifo,
- .mpeg
- .mpg
- .doc
- .docx
- .xls
- .xlsx
- Encrypts files using RSA algorthm and is renames them using the following format: {original file name}.{extension}.ENCODED
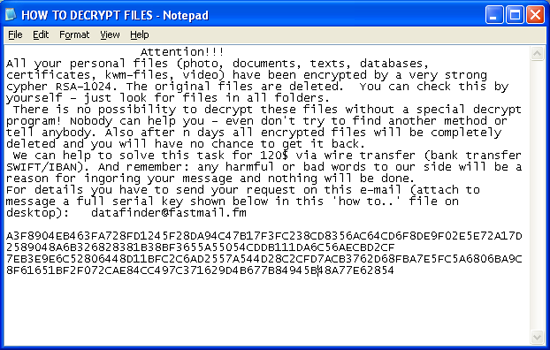
- Opens %Desktop%\HOW TO DECRYPT FILES.txt to allow the users to see the following message:
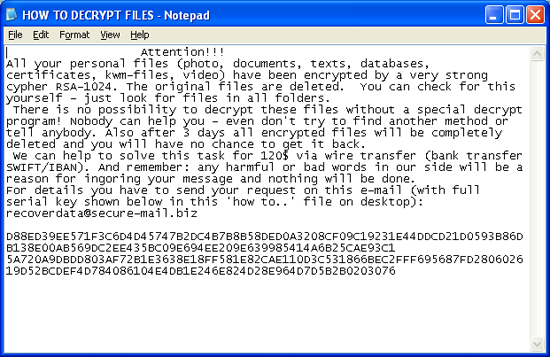
- Displays the following variant of the message:
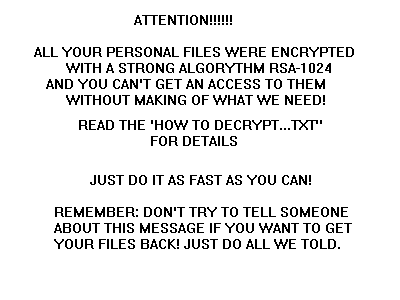
- Drops the picture file, {random characters}.bmp, in the user's Temp folder then sets the file as the wallpaper
It deletes itself after execution.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product to delete files detected as TROJ_RANSOM.EWQ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


