WORM_DORKBOT.BZ
Trojan:Win32/Ircbrute (Microsoft), W32.IRCBot.NG (Symantec), W32/IRCbot.gen.a (McAfee), Trojan.Win32.Menti.gqsk (Kaspersky)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm arrives by connecting affected removable drives to a system. It may be downloaded by other malware/grayware/spyware from remote sites. It may be dropped by other malware. It may be unknowingly downloaded by a user while visiting malicious websites.
It is injected into all running processes to remain memory resident.
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
It also has rootkit capabilities, which enables it to hide its processes and files from the user.
It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This worm arrives by connecting affected removable drives to a system.
It may be downloaded by other malware/grayware/spyware from remote sites.
It may be dropped by other malware.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This worm drops the following copies of itself into the affected system:
- %User Profile%\Application Data\{random file name}.exe
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.)
It is injected into all running processes to remain memory resident.
Autostart Technique
This worm adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{random file name} = "%User Profile%\Application Data\{random file name}.exe"
Propagation
This worm creates the following folders in all removable drives:
- RECYCLER
It drops the following copy(ies) of itself in all removable drives:
- {removable drive letter}:\RECYCLER\{random hexadecimal number}.exe
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
[autorun]
;{garbage characters}
shellexecute=RECYCLER\{random file name}.exe
;{garbage characters}
icon=shell32.dll,7
;{garbage characters}
shell\open\command=RECYCLER\{random file name}.exe
;{garbage characters}
action=Open folder to view files
;{garbage characters}
shell\explore\command=RECYCLER\{random file name}.exe
;{garbage characters}
useautoplay=1
It sends messages that contain links to sites hosting remote copies of itself using the following instant-messaging (IM) applications:
- Windows Live Communicator
- MSN Messenger
- Pidgin
- Xchat
- mIRC
Rootkit Capabilities
This worm also has rootkit capabilities, which enables it to hide its processes and files from the user.
Other Details
This worm connects to the following URL(s) to get the affected system's IP address:
- http://api.wipmania.com/
It deletes the initially executed copy of itself
NOTES:
It hooks the following API functions to hide itself and to aid its routines:
- CopyFileA
- CopyFileW
- CreateFileA
- CreateFileW
- DeleteFileA
- DeleteFileW
- DnsQuery_A
- DnsQuery_W
- GetAddrInfoW
- HttpSendRequestA
- HttpSendRequestW
- InternetWriteFile
- LdrEnumerateLoadedModules
- LdrGetDllHandle
- LdrGetProcedureAddress
- LdrLoadDll
- MoveFileA
- MoveFileW
- NtEnumerateValueKey
- NtQueryDirectoryFile
- NtQueryInformationProcess
- NtQueryInformationThread
- NtQuerySystemInformation
- NtQueryVirtualMemory
- PR_Write
- RegCreateKeyExA
- RegCreateKeyExW
- RtlAnsiStringToUnicodeString
- URLDownloadToFileA
- URLDownloadToFileW
It drops the file {removable drive letter}:\RECYCLER\Desktop.ini to change the icon of the RECYCLER folder into the Recycle Bin icon.
It drops shortcut files pointing to the copy of itself in removable drives. These dropped .LNK files use the names of the folders located on the said drives for their file names. It then sets the attributes of the original folders to Hidden to trick the user into clicking the .LNK files.
It connects to a random IP address to send and receive information.
It has the following backdoor capabilities:
- Block DNS
- Create processes
- Download other files
- Insert iframe tags into HTML files
- Join an IRC channel
- Log in to FTP sites
- Perform Slowloris, UDP, and SYN flooding
- Run Reverse Socks4 proxy server
- Send MSN Messenger messages
- Steal login credentials
- Update Itself
- Visit a website
It steals the login credentials to websites by checking the following strings in the URL:
- *&password=*
- *&txtPassword=*
- *.moneybookers.*/*login.pl
- *1and1.com/xml/config*
- *4shared.com/login*
- *:2082/login*
- *:2083/login*
- *:2086/login*
- *:2222/CMD_LOGIN*
- *alertpay.com/login*
- *aol.*/*login.psp*
- *bcointernacional*login*
- *bigstring.*/*index.php*
- *clave=*
- *depositfiles.*/*/login*
- *dotster.com/*login*
- *dyndns*/account*
- *enom.com/login*
- *facebook.*/login.php*
- *fastmail.*/mail/*
- *fileserv.com/login*
- *filesonic.com/*login*
- *FLN-Password=*
- *freakshare.com/login*
- *gmx.*/*FormLogin*
- *godaddy.com/login*
- *google.*/*ServiceLoginAuth*
- *hackforums.*/member.php
- *hotfile.com/login*
- *letitbit.net*
- *login.live.*/*post.srf*
- *login.Pass=*
- *login.yahoo.*/*login*
- *login_pass=*
- *login_password=*
- *LoginPassword=*
- *loginUserPassword=*
- *mediafire.com/*login*
- *megaupload.*/*login*
- *members*.iknowthatgirl*/members*
- *members.brazzers.com*
- *moniker.com/*Login*
- *namecheap.com/*login*
- *netflix.com/*ogin*
- *netload.in/index*
- *no-ip*/login*
- *officebanking.cl/*login.asp*
- *oron.com/login*
- *pas=*
- *pass=*
- *Passwd=*
- *password=*
- *password]=*
- *paypal.*/webscr?cmd=_login-submit*
- *pw=*
- *runescape*/*weblogin*
- *screenname.aol.*/login.psp*
- *secure.logmein.*/*logincheck*
- *sendspace.com/login*
- *service=youtube*
- *signin.ebay*SignIn
- *sms4file.com/*/signin-do*
- *speedyshare.com/login*
- *steampowered*/login*
- *TextfieldPassword=*
- *thepiratebay.org/login*
- *torrentleech.org/*login*
- *twitter.com/sessions
- *txtpass=*
- *uploaded.to/*login*
- *uploading.com/*login*
- *vip-file.com/*/signin-do*
- *webnames.ru/*user_login*
- *what.cd/login*
- *whcms*dologin*
- *youporn.*/login*
- 1and1
- 4shared
- Alertpay
- Bcointernacional
- BigString
- Brazzers
- clave
- Depositfiles
- Dotster
- DynDNS
- EmailName
- Fastmail
- Fileserve
- Filesonic
- FLN-Password
- FLN-UserName
- Freakshare
- Gmail
- Godaddy
- Hackforums
- Hotfile
- IKnowThatGirl
- Letitbit
- login
- login.Pass
- login.User
- login_email
- login_pass
- login_password
- loginId
- loginname
- LoginPassword
- loginUserName
- loginUserPassword
- LogMeIn
- Mediafire
- Megaupload
- Moneybookers
- Moniker
- Namecheap
- Netflix
- Netload
- numeroTarjeta
- OfficeBanking
- Passwd
- password
- quick_password
- quick_username
- Runescape
- screenname
- Sendspace
- session[password]
- session[username_or_email]
- Sms4file
- Speedyshare
- Steam
- TextfieldEmail
- TextfieldPassword
- Thepiratebay
- token
- Torrentleech
- txtEmail
- txtpass
- txtPassword
- txtuser
- Uploaded
- Uploading
- userid
- username
- Vip-file
- Webnames
- Whatcd
- Yahoo
- YouPorn
- YouTube
It attempts to steal user credentials used in the following websites:
- AlertPay
- AOL
- BigString
- Brazzers
- Depositfiles
- Dotster
- DynDNS
- E-bay
- Fastmail
- FileServe
- FileSonic
- FreakShare
- Gmail
- GMX
- Go Daddy
- Hackforums
- Hotfile
- Letitbit
- LogMeIn
- MediaFire
- Megaupload
- Moneybookers
- Moniker
- Namecheap
- Netflix
- Netload Serious Filehosting
- No-IP
- OfficeBanking
- Oron
- PayPal
- Runescape
- SendSpace
- sms4file
- Speedy Share
- Steam
- TorrentLeech
- The Piraye Bay
- uploaded
- Uploading
- ViP-file
- Webnames (Russia)
- What.CD
- Windows Live
- Yahoo
- YouPorn
- YouTube
- 4shared
It blocks connections to sites if the URL contains the following anti-virus related strings:
- avast.
- avira.
- bitdefender.
- bullguard.
- clamav.
- comodo.
- emsisoft.
- eset.
- f-secure.
- fortinet.
- garyshood.
- gdatasoftware.
- heck.tc
- iseclab.
- jotti.
- kaspersky.
- lavasoft.
- malwarebytes.
- mcafee.
- norman.
- norton.
- novirusthanks.
- onecare.live.
- onlinemalwarescanner.
- pandasecurity.
- precisesecurity.
- sophos.
- sunbeltsoftware.
- symantec
- threatexpert.
- trendmicro.
- virscan.
- virus.
- virusbuster.nprotect.
- viruschief.
- virustotal.
- webroot.
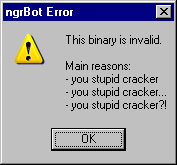
It displays the following message box, then corrupts the hard disk of an infected system if the important parts of the malware are modified:
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Restart in Safe Mode
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {random file name}="%User Profile%\Application Data\{random file name}.exe"
- {random file name}="%User Profile%\Application Data\{random file name}.exe"
Step 4
Search and delete this folder
Step 5
Search and delete this file
Step 6
Search and delete AUTORUN.INF files created by WORM_DORKBOT.BZ that contain these strings
Step 7
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_DORKBOT.BZ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
Changing File attributes using ATTRIB command
- Open a command prompt.
For Windows 2000, Windows XP, and Windows Server 2003 users, click Start > Run. In the Open input box, type [b]CMD[/b] then press Enter.
For Windows Vista and Windows 7 users, click Start, type [b]CMD[/b] in the Search input field then press Enter. - In the Command Prompt (CMD) window, type the following:
ATTRIB [+R | -R] [+A | -A ] [+S | -S] [+H | -H] [+I | -I] [drive:][path][filename] [/S [/D] [/L]]
Where:
+ Sets an attribute.
- Clears an attribute.
R Read-only file attribute.
A Archive file attribute.
S System file attribute.
H Hidden file attribute.
I Not content indexed file attribute.
[drive:][path][filename] Specifies a file or files for attrib to process.
/S Processes matching files in the current folder and all subfolders.
/D Processes folders as well.
/L Work on the attributes of the Symbolic Link versus the target of the Symbolic Link
Example:To remove the Hidden attribute for all files and folders, including subfolders, in drive D, type the following command:
ATTRIB –H D:\* /S /D - Repeat Step 2 for folders and files in other drives or folders.
Did this description help? Tell us how we did.



