TROJ_FAKEAV.GAC
Windows 2000, XP, Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Trojan connects to a website to send and receive information.
It displays fake alerts that warn users of infection. It also displays fake scanning results of the affected system. It then asks for users to purchase it once scanning is completed. If users decide to purchase the rogue product, users are directed to a certain website asking for sensitive information, such as credit card numbers.
TECHNICAL DETAILS
Installation
This Trojan drops the following copies of itself into the affected system:
- %System Root%\Documents and Settings\All Users\Application Data\f0171\MS314.exe
(Note: %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.)
It creates the following folders:
- %Application Data%\My Security Shield
- %System Root%\Documents and Settings\All Users\Application Data\MSEHSFS
- %System Root%\Documents and Settings\All Users\Application Data\f0171
- %Desktop%\Quarantine Items
- %Desktop%\MSSSys
- %Desktop%\BackUp
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Windows\Profiles\{user name}\Application Data on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Application Data on Windows NT, and C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003.. %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.. %Desktop% is the current user's desktop, which is usually C:\Windows\Profiles\{user name}\Desktop on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Desktop on Windows NT, and C:\Documents and Settings\{User Name}\Desktop on Windows 2000, XP, and Server 2003.)
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
My Security Shield = "%System Root%\Documents and Settings\All Users\Application Data\f0171\MS314.exe" /s /d
It drops the following files:
- %Start Menu%\\My Security Shield.lnk - shortcut to its copy
- %Start Menu%\\Programs\\My Security Shield.lnk- shortcut to its copy
- %Desktop%\\57.mof - non-malicious component
- %Desktop%\\My Security Shield.lnk- shortcut to its copy
- %Application Data%\\Microsoft\\Internet Explorer\\Quick Launch\\My Security Shield.lnk - shortcut to its copy
- %User Profile%\\Recent\\DBOLE.sys - non-malicious component
- %User Profile%\\Recent\\pal.exe - non-malicious component
- %User Profile%\\Recent\\PE.exe - non-malicious component
- %User Profile%\\Recent\\DBOLE.drv - non-malicious component
- %User Profile%\\Recent\\fan.dll - non-malicious component
- %User Profile%\\Recent\\hymt.drv - non-malicious component
- %User Profile%\recent\SICKBOY.sys - non-malicious component
- %User Profile%\recent\ANTIGEN.sys - non-malicious component
- %User Profile%\recent\energy.drv - non-malicious component
- %User Profile%\recent\ANTIGEN.dll - non-malicious component
(Note: %Start Menu% is the current user's Start Menu folder, which is usually C:\Windows\Profiles\{user name}\Start Menu on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu on Windows NT and C:\Windows\Start Menu or C:\Documents and Settings\{User name}\Start Menu on Windows 2000, XP, and Server 2003.. %Desktop% is the current user's desktop, which is usually C:\Windows\Profiles\{user name}\Desktop on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Desktop on Windows NT, and C:\Documents and Settings\{User Name}\Desktop on Windows 2000, XP, and Server 2003.. %Application Data% is the current user's Application Data folder, which is usually C:\Windows\Profiles\{user name}\Application Data on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Application Data on Windows NT, and C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003.. %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.)
Other System Modifications
This Trojan adds the following registry keys:
HKEY_CLASSES_ROOT\a.DocHostUIHandler
HKEY_CLASSES_ROOT\CLSID\{3F2BBC05-40DF-11D2-9455-00104BC936FF}
HKEY_CURRENT_USER\Software\3
It adds the following registry entries:
HKEY_CLASSES_ROOT\Software\Microsoft\
Internet Explorer\SearchScopes
URL = http://{BLOCKED}ala.com/?&uid=2118&q={searchTerms}
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer
ltHI = 0
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer
IIL = 0
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer
ltTST = 1311
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer
ltHI = 0
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer
PRS = http://127.0.0.1:27777/?inj=%ORIGINAL%
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer\BrowserEmulation
MSCompatibilityMode = 0
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
DisallowRun = 1
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
0 = msseces.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
1 = MSASCui.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
2 = ekrn.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
3 = egui.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
5 = avcenter.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
6 = avscan.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
7 = avgfrw.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
8 = avgui.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
9 = avgtray.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
10 = avgscanx.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
11 = avgcfgex.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
12 = avgemc.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
13 = avgchsvx.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
14 = avgcmgr.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer\DisallowRun
15 = avgwdsvc.exe
HKEY_USERS\.DEFAULT\Software\
Microsoft\Internet Explorer\SearchScopes
URL = http://{BLOCKED}ala.com/?&uid=2118&q={searchTerms}
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options
Debugger = svchost.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
{application name}
Debugger = svchost.exe
It modifies the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer\Download
CheckExeSignatures = no
(Note: The default value data of the said registry entry is yes.)
It creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
{malware path and filename} = {malware path and filename}:*:Enabled:My Security Shield
Where {application name} may be any of the following:
- AAWTray.exe
- AVCare.exe
- AVENGINE.EXE
- AVWEBGRD.EXE
- About.exe
- Ad-Aware.exe
- AdwarePrj.exe
- AlphaAV.exe
- AluSchedulerSvc.exe
- AntiVirus_Pro.exe
- AntispywarXP2009.exe
- AntivirusPlus.exe
- AntivirusPro_2010.exe
- AntivirusXP.exe
- Arrakis3.exe
- BDInProcPatch.exe
- BDMsnScan.exe
- BDSurvey.exe
- Center.exe
- Cl.exe
- Heal.exe
- History.exe
- IEShow.exe
- Identity.exe
- JsRcGen.exe
- MPFSrv.exe
- MSASCui.exe
- MalwareRemoval.exe
- McSACore.exe
- MsMpEng.exe
- OAReg.exe
- OAcat.exe
- OAhlp.exe
- ODSW.exe
- OcHealthMon.exe
- PC_Antispyware2010.exe
- PSANCU.exe
- PSANHost.exe
- PSANToManager.exe
- PSUNMain.exe
- PavFnSvr.exe
- PerAvir.exe
- Pro.exe
- Professional.exe
- PsCtrls.exe
- PsImSvc.exe
- PskSvc.exe
- QuickHealCleaner.exe
- SafetyKeeper.exe
- Save.exe
- SaveArmor.exe
- SaveDefense.exe
- SaveKeep.exe
- SecurityFighter.exe
- SoftSafeness.exe
- TPSrv.exe
- TrustWarrior.exe
- Veteran.exe
- VisthAux.exe
- VisthLic.exe
- VisthUpd.exe
- W3asbas.exe
- WebProxy.exe
- WinSSUI.exe
- _avp32.exe
- _avpcc.exe
- _avpm.exe
- a.exe
- aAvgApi.exe
- ackwin32.exe
- adaware.exe
- advxdwin.exe
- agent.exe
- agentsvr.exe
- agentw.exe
- alertsvc.exe
- alevir.exe
- alogserv.exe
- amon9x.exe
- anti-trojan.exe
- antivirus.exe
- antivirusxppro2009.exe
- ants.exe
- apimonitor.exe
- aplica32.exe
- apvxdwin.exe
- arr.exe
- ashAvast.exe
- ashBug.exe
- ashChest.exe
- ashCnsnt.exe
- ashDisp.exe
- ashLogV.exe
- ashMaiSv.exe
- ashPopWz.exe
- ashQuick.exe
- ashServ.exe
- ashSimp2.exe
- ashSimpl.exe
- ashSkPcc.exe
- ashSkPck.exe
- ashUpd.exe
- ashWebSv.exe
- aswChLic.exe
- aswRegSvr.exe
- aswRunDll.exe
- aswUpdSv.exe
- atcon.exe
- atguard.exe
- atro55en.exe
- atupdater.exe
- atwatch.exe
- au.exe
- aupdate.exe
- auto-protect.nav80try.exe
- autodown.exe
- autotrace.exe
- autoupdate.exe
- av360.exe
- avadmin.exe
- avcenter.exe
- avciman.exe
- avconfig.exe
- avconsol.exe
- ave32.exe
- avgcc32.exe
- avgchk.exe
- avgcmgr.exe
- avgcsrvx.exe
- avgctrl.exe
- avgdumpx.exe
- avgemc.exe
- avgiproxy.exe
- avgnsx.exe
- avgnt.exe
- avgrsx.exe
- avgscanx.exe
- avgserv.exe
- avgserv9.exe
- avgsrmax.exe
- avgtray.exe
- avgui.exe
- avgupd.exe
- avgw.exe
- avgwdsvc.exe
- avkpop.exe
- avkserv.exe
- avkservice.exe
- avkwctl9.exe
- avltmain.exe
- avmailc.exe
- avmcdlg.exe
- avnotify.exe
- avnt.exe
- avp32.exe
- avpcc.exe
- avpdos32.exe
- avpm.exe
- avptc32.exe
- avpupd.exe
- avsched32.exe
- avsynmgr.exe
- avupgsvc.exe
- avwin.exe
- avwin95.exe
- avwinnt.exe
- avwsc.exe
- avwupd.exe
- avwupd32.exe
- avwupsrv.exe
- avxmonitor9x.exe
- avxmonitornt.exe
- avxquar.exe
- b.exe
- backweb.exe
- bargains.exe
- bd_professional.exe
- bdagent.exe
- bdfvcl.exe
- bdfvwiz.exe
- bdmcon.exe
- bdreinit.exe
- bdsubwiz.exe
- bdtkexec.exe
- bdwizreg.exe
- beagle.exe
- belt.exe
- bidef.exe
- bidserver.exe
- bipcp.exe
- bipcpevalsetup.exe
- bisp.exe
- blackd.exe
- blackice.exe
- blink.exe
- blss.exe
- bootconf.exe
- bootwarn.exe
- borg2.exe
- bpc.exe
- brasil.exe
- brastk.exe
- brw.exe
- bs120.exe
- bspatch.exe
- bundle.exe
- bvt.exe
- c.exe
- cavscan.exe
- ccSvcHst.exe
- ccapp.exe
- ccevtmgr.exe
- ccpxysvc.exe
- cdp.exe
- cfd.exe
- cfgwiz.exe
- cfiadmin.exe
- cfiaudit.exe
- cfinet.exe
- cfinet32.exe
- cfp.exe
- cfpconfg.exe
- cfplogvw.exe
- cfpupdat.exe
- claw95.exe
- claw95cf.exe
- clean.exe
- cleanIELow.exe
- cleaner.exe
- cleaner3.exe
- cleanpc.exe
- click.exe
- cmd32.exe
- cmdagent.exe
- cmesys.exe
- cmgrdian.exe
- cmon016.exe
- connectionmonitor.exe
- cpd.exe
- cpf9x206.exe
- cpfnt206.exe
- crashrep.exe
- csc.exe
- cssconfg.exe
- cssupdat.exe
- cssurf.exe
- ctrl.exe
- cv.exe
- cwnb181.exe
- cwntdwmo.exe
- d.exe
- datemanager.exe
- dcomx.exe
- defalert.exe
- defscangui.exe
- defwatch.exe
- deloeminfs.exe
- deputy.exe
- divx.exe
- dllcache.exe
- dllreg.exe
- doors.exe
- dop.exe
- dpf.exe
- dpfsetup.exe
- dpps2.exe
- driverctrl.exe
- drwatson.exe
- drweb32.exe
- drwebupw.exe
- dssagent.exe
- dvp95.exe
- dvp95_0.exe
- ecengine.exe
- efpeadm.exe
- egui.exe
- ekrn.exe
- emsw.exe
- ent.exe
- esafe.exe
- escanhnt.exe
- escanv95.exe
- espwatch.exe
- ethereal.exe
- etrustcipe.exe
- evpn.exe
- exantivirus-cnet.exe
- exe.avxw.exe
- expert.exe
- explore.exe
- f-agnt95.exe
- f-prot.exe
- f-prot95.exe
- f-stopw.exe
- fact.exe
- fameh32.exe
- fast.exe
- fch32.exe
- fih32.exe
- findviru.exe
- firewall.exe
- fixcfg.exe
- fixfp.exe
- fnrb32.exe
- fp-win.exe
- fp-win_trial.exe
- fprot.exe
- frmwrk32.exe
- frw.exe
- fsaa.exe
- fsav.exe
- fsav32.exe
- fsav530stbyb.exe
- fsav530wtbyb.exe
- fsav95.exe
- fsgk32.exe
- fsm32.exe
- fsma32.exe
- fsmb32.exe
- gator.exe
- gav.exe
- gbmenu.exe
- gbn976rl.exe
- gbpoll.exe
- generics.exe
- gmt.exe
- guard.exe
- guarddog.exe
- guardgui.exe
- hacktracersetup.exe
- hbinst.exe
- hbsrv.exe
- homeav2010.exe
- hotactio.exe
- hotpatch.exe
- htlog.exe
- htpatch.exe
- hwpe.exe
- hxdl.exe
- hxiul.exe
- iamapp.exe
- iamserv.exe
- iamstats.exe
- ibmasn.exe
- ibmavsp.exe
- icload95.exe
- icloadnt.exe
- icmon.exe
- icsupp95.exe
- icsuppnt.exe
- idle.exe
- iedll.exe
- iedriver.exe
- iface.exe
- ifw2000.exe
- inetlnfo.exe
- infus.exe
- infwin.exe
- init.exe
- init32.exe
- install.exe
- install[1].exe
- install[2].exe
- install[3].exe
- install[4].exe
- install[5].exe
- intdel.exe
- intren.exe
- iomon98.exe
- istsvc.exe
- jammer.exe
- jdbgmrg.exe
- jedi.exe
- kavlite40eng.exe
- kavpers40eng.exe
- kavpf.exe
- kazza.exe
- keenvalue.exe
- kerio-pf-213-en-win.exe
- kerio-wrl-421-en-win.exe
- kerio-wrp-421-en-win.exe
- killprocesssetup161.exe
- launcher.exe
- ldnetmon.exe
- ldpro.exe
- ldpromenu.exe
- ldscan.exe
- licmgr.exe
- livesrv.exe
- lnetinfo.exe
- loader.exe
- localnet.exe
- lockdown.exe
- lockdown2000.exe
- lookout.exe
- lordpe.exe
- lsetup.exe
- luall.exe
- luau.exe
- lucomserver.exe
- luinit.exe
- luspt.exe
- mapisvc32.exe
- mcagent.exe
- mcmnhdlr.exe
- mcmscsvc.exe
- mcnasvc.exe
- mcproxy.exe
- mcshell.exe
- mcshield.exe
- mcsysmon.exe
- mctool.exe
- mcupdate.exe
- mcvsrte.exe
- mcvsshld.exe
- md.exe
- mfin32.exe
- mfw2en.exe
- mfweng3.02d30.exe
- mgavrtcl.exe
- mgavrte.exe
- mghtml.exe
- mgui.exe
- minilog.exe
- mmod.exe
- monitor.exe
- moolive.exe
- mostat.exe
- mpfagent.exe
- mpfservice.exe
- mpftray.exe
- mrflux.exe
- mrt.exe
- msa.exe
- msapp.exe
- msbb.exe
- msblast.exe
- mscache.exe
- msccn32.exe
- mscman.exe
- msdm.exe
- msdos.exe
- msfwsvc.exe
- msiexec16.exe
- mslaugh.exe
- msmgt.exe
- msmsgri32.exe
- msseces.exe
- mssmmc32.exe
- mssys.exe
- msvxd.exe
- mu0311ad.exe
- mwatch.exe
- n32scanw.exe
- nav.exe
- navap.navapsvc.exe
- navapsvc.exe
- navapw32.exe
- navdx.exe
- navlu32.exe
- navnt.exe
- navstub.exe
- navw32.exe
- navwnt.exe
- nc2000.exe
- ncinst4.exe
- ndd32.exe
- neomonitor.exe
- neowatchlog.exe
- netarmor.exe
- netd32.exe
- netinfo.exe
- netmon.exe
- netscanpro.exe
- netspyhunter-1.2.exe
- netutils.exe
- nisserv.exe
- nisum.exe
- nmain.exe
- nod32.exe
- normist.exe
- norton_internet_secu_3.0_407.exe
- notstart.exe
- npf40_tw_98_nt_me_2k.exe
- npfmessenger.exe
- nprotect.exe
- npscheck.exe
- npssvc.exe
- nsched32.exe
- nssys32.exe
- nstask32.exe
- nsupdate.exe
- nt.exe
- ntrtscan.exe
- ntvdm.exe
- ntxconfig.exe
- nui.exe
- nupgrade.exe
- nvarch16.exe
- nvc95.exe
- nvsvc32.exe
- nwinst4.exe
- nwservice.exe
- nwtool16.exe
- oasrv.exe
- oaui.exe
- oaview.exe
- ollydbg.exe
- onsrvr.exe
- optimize.exe
- ostronet.exe
- otfix.exe
- outpost.exe
- outpostinstall.exe
- outpostproinstall.exe
- ozn695m5.exe
- padmin.exe
- panixk.exe
- patch.exe
- pav.exe
- pavcl.exe
- pavproxy.exe
- pavprsrv.exe
- pavsched.exe
- pavsrv51.exe
- pavw.exe
- pc.exe
- pccwin98.exe
- pcfwallicon.exe
- pcip10117_0.exe
- pcscan.exe
- pctsAuxs.exe
- pctsGui.exe
- pctsSvc.exe
- pctsTray.exe
- pdfndr.exe
- pdsetup.exe
- periscope.exe
- persfw.exe
- personalguard.exe
- perswf.exe
- pf2.exe
- pfwadmin.exe
- pgmonitr.exe
- pingscan.exe
- platin.exe
- pop3trap.exe
- poproxy.exe
- popscan.exe
- portdetective.exe
- portmonitor.exe
- powerscan.exe
- ppinupdt.exe
- pptbc.exe
- ppvstop.exe
- prizesurfer.exe
- prmt.exe
- prmvr.exe
- procdump.exe
- processmonitor.exe
- procexplorerv1.0.exe
- programauditor.exe
- proport.exe
- protector.exe
- protectx.exe
- pspf.exe
- purge.exe
- qconsole.exe
- qh.exe
- qserver.exe
- rapapp.exe
- rav7.exe
- rav7win.exe
- rav8win32eng.exe
- ray.exe
- rb32.exe
- rcsync.exe
- realmon.exe
- reged.exe
- regedt32.exe
- rescue.exe
- rescue32.exe
- rrguard.exe
- rscdwld.exe
- rshell.exe
- rtvscan.exe
- rtvscn95.exe
- rulaunch.exe
- rwg.exe
- safeweb.exe
- sahagent.exe
- savenow.exe
- sbserv.exe
- sc.exe
- scam32.exe
- scan32.exe
- scan95.exe
- scanpm.exe
- scrscan.exe
- seccenter.exe
- secureveteran.exe
- securitysoldier.exe
- serv95.exe
- setloadorder.exe
- setup_flowprotector_us.exe
- setupvameeval.exe
- sgssfw32.exe
- sh.exe
- shellspyinstall.exe
- shield.exe
- shn.exe
- showbehind.exe
- signcheck.exe
- smart.exe
- smartprotector.exe
- smc.exe
- smrtdefp.exe
- sms.exe
- smss32.exe
- snetcfg.exe
- soap.exe
- sofi.exe
- sperm.exe
- spf.exe
- sphinx.exe
- spoler.exe
- spoolcv.exe
- spoolsv32.exe
- spywarexpguard.exe
- spyxx.exe
- srexe.exe
- srng.exe
- ss3edit.exe
- ssg_4104.exe
- ssgrate.exe
- st2.exe
- start.exe
- stcloader.exe
- supftrl.exe
- support.exe
- supporter5.exe
- svc.exe
- svchostc.exe
- svchosts.exe
- svshost.exe
- sweep95.exe
- sweepnet.sweepsrv.sys.swnetsup.exe
- symlcsvc.exe
- symproxysvc.exe
- symtray.exe
- system.exe
- system32.exe
- sysupd.exe
- tapinstall.exe
- taskmgr.exe
- taumon.exe
- tbscan.exe
- tc.exe
- tca.exe
- tcm.exe
- tds-3.exe
- tds2-98.exe
- tds2-nt.exe
- teekids.exe
- tfak.exe
- tfak5.exe
- tgbob.exe
- titanin.exe
- titaninxp.exe
- trickler.exe
- trjscan.exe
- trjsetup.exe
- trojantrap3.exe
- tsadbot.exe
- tsc.exe
- tvmd.exe
- tvtmd.exe
- uiscan.exe
- undoboot.exe
- updat.exe
- upgrad.exe
- upgrepl.exe
- utpost.exe
- vbcmserv.exe
- vbcons.exe
- vbust.exe
- vbwin9x.exe
- vbwinntw.exe
- vcsetup.exe
- vet32.exe
- vet95.exe
- vettray.exe
- vfsetup.exe
- vir-help.exe
- virusmdpersonalfirewall.exe
- vnlan300.exe
- vnpc3000.exe
- vpc32.exe
- vpc42.exe
- vpfw30s.exe
- vptray.exe
- vscan40.exe
- vscenu6.02d30.exe
- vsched.exe
- vsecomr.exe
- vshwin32.exe
- vsisetup.exe
- vsmain.exe
- vsmon.exe
- vsserv.exe
- vsstat.exe
- vswin9xe.exe
- vswinntse.exe
- vswinperse.exe
- w32dsm89.exe
- w9x.exe
- watchdog.exe
- webdav.exe
- webscanx.exe
- webtrap.exe
- wfindv32.exe
- whoswatchingme.exe
- wimmun32.exe
- win-bugsfix.exe
- win32.exe
- win32us.exe
- winactive.exe
- winav.exe
- windll32.exe
- window.exe
- windows.exe
- wininetd.exe
- wininitx.exe
- winlogin.exe
- winmain.exe
- winppr32.exe
- winrecon.exe
- winservn.exe
- winss.exe
- winssk32.exe
- winssnotify.exe
- winstart.exe
- winstart001.exe
- wintsk32.exe
- winupdate.exe
- wkufind.exe
- wnad.exe
- wnt.exe
- wradmin.exe
- wrctrl.exe
- wsbgate.exe
- wscfxas.exe
- wscfxav.exe
- wscfxfw.exe
- wsctool.exe
- wupdater.exe
- wupdt.exe
- wyvernworksfirewall.exe
- xp_antispyware.exe
- xpdeluxe.exe
- xpf202en.exe
- zapro.exe
- zapsetup3001.exe
- zatutor.exe
- zonalm2601.exe
- zonealarm.exe
- ~1.exe
- ~2.exe
Backdoor Routine
This Trojan connects to the following websites to send and receive information:
- {BLOCKED}dwlentor-disgan669.net
HOSTS File Modification
This Trojan adds the following strings to the Windows HOSTS file:
- {BLOCKED}.{BLOCKED}.45.100 4-open-davinci.com
- {BLOCKED}.{BLOCKED}.45.100 securitysoftwarepayments.com
- {BLOCKED}.{BLOCKED}.45.100 privatesecuredpayments.com
- {BLOCKED}.{BLOCKED}.45.100 secure.privatesecuredpayments.com
- {BLOCKED}.{BLOCKED}.45.100 getantivirusplusnow.com
- {BLOCKED}.{BLOCKED}.45.100 secure-plus-payments.com
- {BLOCKED}.{BLOCKED}.45.100 www.getantivirusplusnow.com
- {BLOCKED}.{BLOCKED}.45.100 www.secure-plus-payments.com
- {BLOCKED}.{BLOCKED}.45.100 www.getavplusnow.com
- {BLOCKED}.{BLOCKED}.45.100 safebrowsing-cache.google.com
- {BLOCKED}.{BLOCKED}.45.100 urs.microsoft.com
- {BLOCKED}.{BLOCKED}.45.100 www.securesoftwarebill.com
- {BLOCKED}.{BLOCKED}.45.100 secure.paysecuresystem.com
- {BLOCKED}.{BLOCKED}.45.100 paysoftbillsolution.com
- {BLOCKED}.{BLOCKED}.45.100 protected.maxisoftwaremart.com
- {BLOCKED}.{BLOCKED}.243.64 www.google.com
- {BLOCKED}.{BLOCKED}.243.64 google.com
- {BLOCKED}.{BLOCKED}.243.64 google.com.au
- {BLOCKED}.{BLOCKED}.243.64 www.google.com.au
- {BLOCKED}.{BLOCKED}.243.64 google.be
- {BLOCKED}.{BLOCKED}.243.64 www.google.be
- {BLOCKED}.{BLOCKED}.243.64 google.com.br
- {BLOCKED}.{BLOCKED}.243.64 www.google.com.br
- {BLOCKED}.{BLOCKED}.243.64 google.ca
- {BLOCKED}.{BLOCKED}.243.64 www.google.ca
- {BLOCKED}.{BLOCKED}.243.64 google.ch
- {BLOCKED}.{BLOCKED}.243.64 www.google.ch
- {BLOCKED}.{BLOCKED}.243.64 google.de
- {BLOCKED}.{BLOCKED}.243.64 www.google.de
- {BLOCKED}.{BLOCKED}.243.64 google.dk
- {BLOCKED}.{BLOCKED}.243.64 www.google.dk
- {BLOCKED}.{BLOCKED}.243.64 google.fr
- {BLOCKED}.{BLOCKED}.243.64 www.google.fr
- {BLOCKED}.{BLOCKED}.243.64 google.ie
- {BLOCKED}.{BLOCKED}.243.64 www.google.ie
- {BLOCKED}.{BLOCKED}.243.64 google.it
- {BLOCKED}.{BLOCKED}.243.64 www.google.it
- {BLOCKED}.{BLOCKED}.243.64 google.co.jp
- {BLOCKED}.{BLOCKED}.243.64 www.google.co.jp
- {BLOCKED}.{BLOCKED}.243.64 google.nl
- {BLOCKED}.{BLOCKED}.243.64 www.google.nl
- {BLOCKED}.{BLOCKED}.243.64 google.no
- {BLOCKED}.{BLOCKED}.243.64 www.google.no
- {BLOCKED}.{BLOCKED}.243.64 google.co.nz
- {BLOCKED}.{BLOCKED}.243.64 www.google.co.nz
- {BLOCKED}.{BLOCKED}.243.64 google.pl
- {BLOCKED}.{BLOCKED}.243.64 www.google.pl
- {BLOCKED}.{BLOCKED}.243.64 google.se
- {BLOCKED}.{BLOCKED}.243.64 www.google.se
- {BLOCKED}.{BLOCKED}.243.64 google.co.uk
- {BLOCKED}.{BLOCKED}.243.64 www.google.co.uk
- {BLOCKED}.{BLOCKED}.243.64 google.co.za
- {BLOCKED}.{BLOCKED}.243.64 www.google.co.za
- {BLOCKED}.{BLOCKED}.243.64 www.google-analytics.com
- {BLOCKED}.{BLOCKED}.243.64 www.bing.com
- {BLOCKED}.{BLOCKED}.243.64 search.yahoo.com
- {BLOCKED}.{BLOCKED}.243.64 www.search.yahoo.com
- {BLOCKED}.{BLOCKED}.243.64 uk.search.yahoo.com
- {BLOCKED}.{BLOCKED}.243.64 ca.search.yahoo.com
- {BLOCKED}.{BLOCKED}.243.64 de.search.yahoo.com
- {BLOCKED}.{BLOCKED}.243.64 fr.search.yahoo.com
- {BLOCKED}.{BLOCKED}.243.64 au.search.yahoo.com
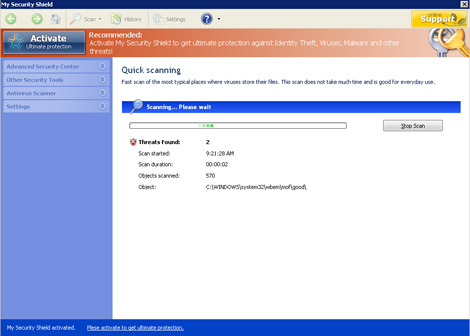
Rogue Antivirus Routine
This Trojan displays the following fake alerts:
It displays fake alerts that warn users of infection. It also displays fake scanning results of the affected system. It then asks for users to purchase it once scanning is completed. If users decide to purchase the rogue product, users are directed to a certain website asking for sensitive information, such as credit card numbers.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Identify and terminate files detected as TROJ_FAKEAV.GAC
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 3
Search and delete these folders
Step 4
Search and delete this file
Step 5
Remove these strings added by the malware/grayware/spyware in the HOSTS file
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CLASSES_ROOT\a.DocHostUIHandler
Step 7
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Step 8
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download
Step 9
Scan your computer with your Trend Micro product to delete files detected as TROJ_FAKEAV.GAC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.