
Ransom.MSIL.TARGETCOMP.THHBBBB
UDS:Trojan-Downloader.MSIL.PsDownload.gen (KASPERSKY)
Windows
- マルウェアタイプ: 身代金要求型不正プログラム(ランサムウェア)
- 破壊活動の有無: なし
- 暗号化:
- 感染報告の有無: はい
概要
マルウェアは、他のマルウェアに作成されるか、悪意あるWebサイトからユーザが誤ってダウンロードすることによりコンピュータに侵入します。
詳細
侵入方法
マルウェアは、他のマルウェアに作成されるか、悪意あるWebサイトからユーザが誤ってダウンロードすることによりコンピュータに侵入します。
インストール
マルウェアは、感染したコンピュータ内に以下のように自身のコピーを作成します。
- %Application Data%\Syfwfpwux\Lcudsgjlb.exe
(註:%Application Data%フォルダは、現在ログオンしているユーザのアプリケーションデータフォルダです。Windows 2000(32-bit)、XP、Server 2003(32-bit)の場合、通常 "C:\Documents and Settings\<ユーザ名>\Local Settings\Application Data" です。また、Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit)、10(64-bit)の場合、通常 "C:\Users\<ユーザ名>\AppData\Roaming" です。)
マルウェアは、以下のファイルを作成し実行します。
- %User Temp%\Logrpaqfriixribkill$.bat
(註:%User Temp%フォルダは、現在ログオンしているユーザの一時フォルダです。Windows 2000(32-bit)、XP、Server 2003(32-bit)の場合、通常 "C:\Documents and Settings\<ユーザー名>\Local Settings\Temp"です。また、Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit)、10(64-bit)の場合、通常 "C:\Users\<ユーザ名>\AppData\Local\Temp" です。)
マルウェアは、以下のプロセスを追加します。
- start https://{BLOCKED}er.org/1NRk35
- takeown /f %SystemRoot%\system32\cmd.exe /a
- "%System32%\WindowsPowerShell\v1.0\powershell.exe" -Start -Sleep -Seconds 20
- cmd /c ""%Temp%\Logrpaqfriixribkill$.bat" "
- reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Command Processor" /v "AutoRun" /f
- "%Program Files%\Internet Explorer\iexplore.exe" -nohome
- "%Program Files%\Internet Explorer\iexplore.exe" SCODEF:3332 CREDAT:71937
- %Windows%\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe
- "%System32%\cmd.exe" /c bcdedit /set {current} bootstatuspolicy ignoreallfailures
- "%System32%\cmd.exe" /c bcdedit /set {current} recoveryenabled no
- \sysnative\vssadmin.exe delete shadows /all /quiet
- tasklist /fi "imagename eq {String}
- where String:
- MsMpEng.exe
- ntrtscan.exe
- avp.exe
- WRSA.exe
- egui.exe
- AvastUI.exe
- takeown /f %ProgramData%\ /a
- takeown /f %Public User%\ /a
- takeown /f %Windows%\SysWOW64\{String} /a
- takeown /f %System32%\{String} /a
- where {String}:
- cmd.exe
- net.exe
- net1.exe
- mshta.exe
- FTP.exe
- wscript.exe
- cscript.exe
- WindowsPowerShell\v1.0\powershell.exe
- cacls {String} /g Administrators:f
- cacls {String} /e /g Users:r
- cacls {String} /e /g Administrators:r
- cacls {String} /e /d SERVICE
- cacls {String} /e /d mssqlserver
- cacls {String} /e /d "network service"
- cacls {String} /e /d system
- cacls {String} /e /d mssql$sqlexpress
- where {String}:
- %ProgramData%\
- %Public User%\
- cacls %System32%\{String} /g Administrators:f
- cacls %System32%\{String} /e /g Users:r
- cacls %System32%\{String} /e /g Administrators:r
- cacls %System32%\{String} /e /d SERVICE
- cacls %System32%\{String} /e /d mssqlserver
- cacls %System32%\{String} /e /d "network service"
- cacls %System32%\{String} /e /g system:r
- cacls %System32%\{String} /e /d mssql$sqlexpress
- where {String}:
- cmd.exe
- net.exe
- net1.exe
- mshta.exe
- FTP.exe
- wscript.exe
- cscript.exe
- WindowsPowerShell\v1.0\powershell.exe
- cacls %Windows%\SysWOW64\{String} /g Administrators:f
- cacls %Windows%\SysWOW64\{String} /e /g Users:r
- cacls %Windows%\SysWOW64\{String} /e /g Administrators:r
- cacls %Windows%\SysWOW64\{String} /e /d SERVICE
- cacls %Windows%\SysWOW64\{String} /e /d mssqlserver
- cacls %Windows%\SysWOW64\{String} /e /d "network service"
- cacls %Windows%\SysWOW64\{String} /e /g system:r
- cacls %Windows%\SysWOW64\{String} /e /d mssql$sqlexpress
- where {String}:
- cmd.exe
- net.exe
- net1.exe
- mshta.exe
- FTP.exe
- wscript.exe
- cscript.exe
- WindowsPowerShell\v1.0\powershell.exe
- net stop {Stopped Services 1}
- %System32%\net1 stop {Stopped Services 2}
- sc delete {Services Deleted}
- taskkill /f /im {Stopped Process 1}
- taskkill /IM {Stopped Process 2} /F
- taskkill -f -im {Stopped Process 3}
- taskkill /IM {Stopped Process 4} /F
マルウェアは、以下のフォルダを作成します。
- %Application Data%\Syfwfpwux
(註:%Application Data%フォルダは、現在ログオンしているユーザのアプリケーションデータフォルダです。Windows 2000(32-bit)、XP、Server 2003(32-bit)の場合、通常 "C:\Documents and Settings\<ユーザ名>\Local Settings\Application Data" です。また、Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit)、10(64-bit)の場合、通常 "C:\Users\<ユーザ名>\AppData\Roaming" です。)
マルウェアは、以下のプロセスに組み込まれ、システムのプロセスに常駐します。
- %Windows%\Microsoft.NET\Framework\v4.0.30319
\MSBuild.exe
(註:%Windows%フォルダは、Windowsが利用するフォルダで、いずれのオペレーティングシステム(OS)でも通常、"C:\Windows" です。.)
自動実行方法
マルウェアは、自身のコピーがWindows起動時に自動実行されるよう以下のレジストリ値を追加します。
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Lcudsgjlb = %Application Data%\Syfwfpwux\Lcudsgjlb.exe
他のシステム変更
マルウェアは、以下のファイルを削除します。
- %User Temp%\Logrpaqfriixribkill$.bat
(註:%User Temp%フォルダは、現在ログオンしているユーザの一時フォルダです。Windows 2000(32-bit)、XP、Server 2003(32-bit)の場合、通常 "C:\Documents and Settings\<ユーザー名>\Local Settings\Temp"です。また、Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit)、10(64-bit)の場合、通常 "C:\Users\<ユーザ名>\AppData\Local\Temp" です。)
マルウェアは、以下のレジストリキーを削除します。
SOFTWARE\Raccine
SYSTEM\CurrentControlSet\Services\
EventLog\Application\Raccine
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\vssadmin.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\wmic.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\wbadmin.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\bcdedit.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\powershell.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\diskshadow.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\net.exe
SOFTWARE\Microsoft\Windows NT\
CurrentVersion\Image File Execution Options\taskkill.exe
プロセスの終了
マルウェアは、感染コンピュータ上で確認した以下のサービスを終了します。
- where {Stopped Services 1}:
- U8WorkerService1
- U8WorkerService2
- "memcached Server"
- Apache2.4
- UFIDAWebService
- MSComplianceAudit
- MSExchangeADTopology
- MSExchangeAntispamUpdate
- MSExchangeCompliance
- MSExchangeDagMgmt
- MSExchangeDelivery
- MSExchangeDiagnostics
- MSExchangeEdgeSync
- MSExchangeFastSearch
- MSExchangeFrontEndTransport
- MSExchangeHM
- MSSQL$SQL2008
- MSExchangeHMRecovery
- MSExchangeImap4
- MSExchangeIMAP4BE
- MSExchangeIS
- MSExchangeMailboxAssistants
- MSExchangeMailboxReplication
- MSExchangeNotificationsBroker
- MSExchangePop3
- MSExchangePOP3BE
- MSExchangeRepl
- MSExchangeRPC
- MSExchangeServiceHost
- MSExchangeSubmission
- MSExchangeThrottling
- MSExchangeTransport
- MSExchangeTransportLogSearch
- MSExchangeUM
- MSExchangeUMCR
- MySQL5_OA
- HaoZipSvc
- Realtek11nSU
- xenlite
- XenSvc
- Apache2.2
- "Synology Drive VSS Service x64"
- DellDRLogSvc
- FirebirdGuardianDeafaultInstance
- JWEM3DBAUTORun
- JWRinfoClientService
- JWService
- Service2
- RapidRecoveryAgent
- FirebirdServerDefaultInstance
- AdobeARMservice
- VeeamCatalogSvc
- VeeanBackupSvc
- VeeamTransportSvc
- TPlusStdAppService1300
- TPlusStdTaskService1300
- TPlusStdUpgradeService1300
- TPlusStdWebService1300
- VeeamNFSSvc
- VeeamDeploySvc
- VeeamCloudSvc
- VeeamMountSvc
- VeeamBrokerSvc
- VeeamDistributionSvc
- tmlisten
- ServiceMid
- 360EntPGSvc
- ClickToRunSvc
- RavTask
- AngelOfDeath
- d_safe
- NFLicenceServer
- "NetVault Process Manager"
- RavService
- DFServ
- IngressMgr
- EvtSys
- K3ClouManager
- NFVPrintServer
- RTCAVMCU
- CobianBackup10
- GNWebService
- Mysoft.SchedulingService
- AgentX
- SentinelKeysServer
- DGPNPSEV
- TurboCRM70
- NFSysService
- U8DispatchService
- NFOTPService
- U8EISService
- U8EncryptService
- U8GCService
- U8KeyManagePool
- U8MPool
- U8SCMPool
- U8SLReportService
- U8TaskService
- U8WebPool
- UFAllNet
- UFReportService
- UTUService"
- UIODetect
- VMwareHostd
- TeamViewer8
- VMUSBArbService
- VMAuthdService
- wanxiao-monitor
- WebAttendServer
- mysqltransport
- VMnetDHCP
- "VMware NAT Service"
- Tomcat8
- TeamViewer
- QPCore
- CASLicenceServer
- CASWebServer
- AutoUpdateService
- "Alibaba Security Aegis Detect Service"
- "Alibaba Security Aegis Update Service"
- "AliyunService"
- CASXMLService
- AGSService
- RapService
- DDNSService
- iNethinkSQLBackupSvc
- CASVirtualDiskService
- CASMsgSrv
- "OracleOraDb10g_homeliSQL*Plus"
- OracleDBConsoleilas
- MySQL
- TPlusStdAppService1220
- TPlusStdTaskService1220
- TPlusStdUpgradeService1220
- K3MobileServiceManage
- "FileZilla Server"
- DDVRulesProcessor
- ImtsEventSvr
- AutoUpdatePatchService
- OMAILREPORT
- "Dell Hardware Support"
- SupportAssistAgent
- K3MMainSuspendService
- KpService
- ceng_web_svc_d
- KugouService
- pcas
- U8SendMailAdmin
- "Bonjour Service"
- "Apple Mobile Device Service"
- "ABBYY.Licensing.FineReader.Professional.12.0""
- MSSQLServerADHelper100
- MSSQL$ISARS
- MSSQL$MSFW
- SQLAgent$ISARS
- SQLAgent$MSFW
- SQLBrowser
- ReportServer$ISARS
- SQLWriter
- WinDefend
- mr2kserv
- MSExchange
- ShadowProtectSvc
- SPAdminV4
- SPTimerV4
- SPTraceV4
- SPUserCodeV4
- SPWriterV4
- SPSearch4
- MSSQLServerADHelper100
- IISADMIN
- firebirdguardiandefaultinstance
- ibmiasrw
- QBCFMonitorService
- QBVSS
- QBPOSDBServiceV12
- "IBM Domino Server (CProgramFilesIBMDominodata)"
- "IBM Domino Diagnostics (CProgramFilesIBMDomino)"
- IISADMIN
- "Simply Accounting Database Connection Manager"
- QuickBooksDB1
- QuickBooksDB2
- QuickBooksDB3
- QuickBooksDB4
- QuickBooksDB5
- where {Stopped Services 2}:
- U8WorkerService1
- U8WorkerService2
- UIODetect
- HaoZipSvc
- "memcached Server"
- VMwareHostd
- Apache2.4
- UFIDAWebService
- "igfxCUIService2.0.0.0"
- MSComplianceAudit
- MSExchangeADTopology
- MSExchangeAntispamUpdate
- TeamViewer8
- Realtek11nSU
- VMUSBArbService
- MSExchangeCompliance
- xenlite
- VMAuthdService
- XenSvc
- wanxiao-monitor
- WebAttendServer
- MSExchangeDagMgmt
- Apache2.2
- mysqltransport
- MSExchangeDelivery
- VMnetDHCP
- MSExchangeDiagnostics
- "Synology Drive VSS Service x64"
- "VMware NAT Service"
- MSExchangeEdgeSynca
- DellDRLogSvc
- FirebirdGuardianDeafaultInstance
- Tomcat8
- MSExchangeFastSearch
- JWEM3DBAUTORun
- JWRinfoClientService
- MSExchangeFrontEndTransport
- TeamViewer
- MSExchangeHM
- QPCore
- JWService
- CASLicenceServer
- MSSQL$SQL2008
- Service2
- CASWebServer
- MSExchangeHMRecovery
- RapidRecoveryAgent
- AutoUpdateService
- MSExchangeImap4
- FirebirdServerDefaultInstance
- MSExchangeIMAP4BE
- "Alibaba Security Aegis Detect Service"
- AdobeARMservice
- MSExchangeIS
- VeeamCatalogSvc
- "Alibaba Security Aegis Update Service"
- MSExchangeMailboxAssistants
- VeeanBackupSvc
- "AliyunService"
- VeeamTransportSvc
- CASXMLService
- MSExchangeMailboxReplication
- MSExchangeNotificationsBroker
- AGSService
- TPlusStdAppService1300
- RapService
- DDNSService
- MSExchangePop3
- iNethinkSQLBackupSvc
- TPlusStdTaskService1300
- MSExchangePOP3BE
- CASVirtualDiskService
- TPlusStdUpgradeService1300
- MSExchangeRepl
- MSExchangeRPC
- CASMsgSrv
- TPlusStdWebService1300
- "OracleOraDb10g_homeliSQL*Plus"
- VeeamNFSSvc
- MSExchangeServiceHost
- OracleDBConsoleilas
- VeeamDeploySvc
- MSExchangeSubmission
- VeeamCloudSvc
- MySQL
- MSExchangeThrottling
- TPlusStdAppService1220
- VeeamMountSvc
- MSExchangeTransport
- MSExchangeTransportLogSearch
- VeeamBrokerSvc
- TPlusStdTaskService1220
- MSExchangeUM
- VeeamDistributionSvc
- TPlusStdUpgradeService1220
- MSExchangeUMCR
- tmlisten
- MySQL5_OA
- K3MobileServiceManage
- ServiceMid
- "FileZilla Server"
- 360EntPGSvc
- DDVRulesProcessor
- ClickToRunSvc
- ImtsEventSvr
- AutoUpdatePatchService
- RavTask
- OMAILREPORT
- AngelOfDeath
- "Dell Hardware Support"
- d_safe
- SupportAssistAgent
- K3MMainSuspendService
- NFLicenceServer
- "NetVault Process Manager"
- KpService
- RavService
- ceng_web_svc_d
- KugouService
- DFServ
- IngressMgr
- pcas
- U8SendMailAdmin
- EvtSys
- "Bonjour Service"
- K3ClouManager
- "Apple Mobile Device Service"
- NFVPrintServer
- "ABBYY.Licensing.FineReader.Professional.12.0"
- RTCAVMCU
- CobianBackup10
- GNWebService
- Mysoft.SchedulingService
- AgentX
- SentinelKeysServer
- DGPNPSEV
- TurboCRM70
- NFSysService
- U8DispatchService
- NFOTPService
- U8EISService
- U8EncryptService
- U8GCService
- U8KeyManagePool
- U8MPool
- U8SCMPool
- U8SLReportService
- U8TaskService
- U8WebPool
- UFAllNet
- UFReportService
- UTUService
マルウェアは、感染コンピュータ上で以下のプロセスが常駐されていることを確認した場合、そのプロセスを終了します。
- where {Stopped Process 1}:
- db*
- apache*
- mysql*
- Notifier*
- IBM*
- copy*
- store*
- sql*
- vee*
- wrsa*
- postg*
- sage*
- msdt*
- ora*
- microsoft*
- backup*
- http*
- office*
- cube*
- team*
- b1*
- sbo*
- reporting*
- sav*
- fd*
- where {Stopped Process 2}:
- sqlservr.exe
- httpd.exe
- java.exe
- fdhost.exe
- fdlauncher.exe
- reportingservicesservice.exe
- softmgrlite.exe
- sqlbrowser.exe
- ssms.exe
- vmtoolsd.exe
- baidunetdisk.exe
- yundetectservice.exe
- ssclient.exe
- GNAupdaemon.exe
- RAVCp164.exe
- igfxEM.exe
- igfxHK.exe
- igfxTray.exe
- 360bdoctor.exe
- GNCEFExternal.exe
- PrivacyIconClient.exe
- UIODetect.exe
- AutoDealService.exe
- IDDAService.exe
- EnergyDataService.exe
- MPService.exe
- TransMain.exe
- DAService.exe
- GoogleCrashHandler.exe
- GoogleCrashHandler64.exe
- GoogleUpdate.exe
- cohernece.exe
- vmware-tray.exe
- MsDtsSrvr.exe
- msmdsrv.exe
- "FileZilla server.exe"
- UpdateData.exe
- WebApi.Host.exe
- VGAuthService.exe
- omtsreco.exe
- TNSLSNR.exe
- oracle.exe
- msdtc.exe
- mmc.exe
- emagent.exe
- Admin.exe
- EnterprisePortal.exe
- tomcat7.exe
- Kingdee.K3.CRM.MMC.MMCService.exe
- Kingdee.k3.Weixin.ClientService.exe
- Kingdee.K3.PUBLIC.BkgSvcHost.exe
- Kingdee.K3.HR.Server.exe
- Kingdee.K3.PUBLIC.KDSvrMgrHost.exe
- tomcat5.exe
- Kingdee.DeskTool.exe
- UserClient.exe
- mysqld.exe
- ImtsEventSvr.exe
- mysqld-nt.exe
- 360EnterpriseDiskUI.exe
- tomcat8.exe
- QQprotect.exe
- isqlplussvc.exe
- nmesrvc.exe
- jusched.exe
- MtxHotPlugService.exe
- jucheck.exe
- wordpad.exe
- SecureCRT.exe
- chrome.exe
- Thunder.exe"
- ThunderPlatform.exe
- iexplore.exe
- vm-agent.exe
- vm-agent-daemon.exe
- eSightService.exe
- cygrunsrv.exe
- wrapper.exe
- nginx.exe
- node.exe
- sshd.exe
- vm-tray.exe
- iempwatchdog.exe
- sqlwriter.exe
- php.exe
- "notepad++.exe"
- "phpStudy.exe"
- OPCClient.exe
- navicat.exe
- SupportAssistAgent.exe
- SunloginClient.exe
- SOUNDMAN.exe
- WeChat.exe
- TXPlatform.exe
- Tencentdll.exe
- jenkins.exe
- QQ.exe
- HaoZip.exe
- HaoZipScan.exe
- TSVNCache.exe
- RAVCpl64.exe
- secbizsrv.exe
- aliwssv.exe
- Helper_Haozip.exe
- acrotray.exe
- "FileZilla Server Interface.exe"
- YoudaoNote.exe
- YNoteCefRender.exe
- idea.exe
- fsnotifier.exe
- picpick.exe
- lantern.exe
- sysproxy-
- service.exe
- pcas.exe
- PresentationFontCache.exe
- RtWlan.exe
- monitor.exe
- Correspond.exe
- ChatServer.exe
- InetMgr.exe
- LogonServer.exe
- GameServer.exe
- ServUAdmin.exe
- ServUDaemon.exe
- update0.exe
- server.exe
- w3wp.exe
- notepad.exe
- PalmInputService.exe
- PalmInputGuard.exe
- UpdateServer.exe
- UpdateGate.exe
- DBServer.exe
- LoginGate.exe
- SelGate.exe
- RunGate.exe
- M2Server.exe
- LogDataServer.exe
- LoginSrv.exe
- sqlceip.exe
- mqsvc.exe
- RefundOrder.exe
- ClamTray.exe
- AdobeARM.exe
- veeam.backup.shell.exe
- VpxClient.exe
- vmware-vmrc.exe
- DSCPatchService.exe
- scktsrvr.exe
- ServerManager.exe
- Dispatcher.exe
- EFDispatcher.exe
- ClamWin.exe
- srvany.exe
- JT_AG-8332.exe
- XXTClient.exe
- clean.exe
- "Net.Service.exe"
- plsqldev.exe
- splwow64.exe
- Oobe.exe
- QQYService.exe
- SGTool.exe
- postgres.exe
- AppVShNotify.exe
- OfficeClickToRun.exe
- EntDT.exe
- EntPublish.exe"
- pg_ctl.exe
- rcrelay.exe
- SogouImeBroker.exe
- CCenter.exe
- ScanFrm.exe
- d_manage.exe
- RsTray.exe
- wampmanager.exe
- RavTray.exe
- mssearch.exe
- sqlmangr.exe
- msftesql.exe
- SyncBaseSvr.exe
- oracle.exe
- TNSLSNR.exe
- SyncBaseConsole.exe
- aspnet_state.exe
- AutoBackUpEx.exe
- redis-server.exe
- MySQLNotifier.exe
- oravssw.exe
- fppdis5.exe
- His6Service.exe
- dinotify.exe
- JhTask.exe
- Executer.exe
- AllPassCBHost.exe
- ap_nginx.exe
- AndroidServer.exe
- XT.exe
- XTService.exe
- AllPassMCService.exe
- IMEDICTUPDATE.exe
- FlashHelperService.exe
- ap_redis-server.exe
- UtilDev.WebServer.Monitor.exe
- UWS.AppHost.Clr2.x86.exe
- FoxitProtect.exe
- ftnlses.exe
- ftusbrdwks.exe
- ftusbrdsrv.exe
- ftnlsv.exe
- Syslogd_Service.exe
- UWS.HighPrivilegeUtilities.exe
- ftusbsrv.exe
- UWS.LowPrivilegeUtilities.exe
- UWS.AppHost.Clr2.AnyCpu.exe
- winguard_x64.exe
- vmconnect.exe
- UWS.AppHost.Clr2.x86.exe
- firefox.exe
- usbrdsrv.exe
- usbserver.exe
- Foxmail.exe
- qemu-ga.exe
- wwbizsrv.exe
- ZTEFileTranS.exe
- ZTEUsbIpc.exe
- ZTEUsbIpcGuard.exe
- AlibabaProtect.exe
- kbasesrv.exe
- ZTEVdservice.exe
- MMRHookService.exe
- extjob.exe
- IpOverUsbSvc.exe
- VMwareTray.exe
- devenv.exe
- PerfWatson2.exe
- ServiceHub.Host.Node.x86.exe
- ServiceHub.IdentityHost.exe
- ServiceHub.VSDetouredHost.exe
- ServiceHub.SettingsHost.exe
- ServiceHub.Host.CLR.x86.exe
- ServiceHub.RoslynCodeAnalysisService32.exe
- ServiceHub.DataWarehouseHost.exe
- Microsoft.VisualStudio.Web.Host.exe
- SQLEXPRWT.exe
- setup.exe
- remote.exe
- setup100.exe
- landingpage.exe
- WINWORD.exe
- KuaiYun.exe
- HwsHostPanel.exe
- NovelSpider.exe
- Service_KMS.exe
- WebServer.exe
- ChsIME.exe
- btPanel.exe
- Protect_2345Explorer.exe
- Pic_2345Svc.exe
- vmware-converter-a.exe
- vmware-converter.exe
- vmware.exe
- vmware-unity-helper.exe
- vmware-vmx.exe
- vmware-vmx.exe
- usysdiag.exe
- PopBlock.exe
- gsinterface.exe
- Gemstar.Group.CRS.Client.exe
- TenpayServer.exe
- RemoteExecService.exe
- VS_TrueCorsManager.exe
- ntpsvr-2019-01-22-wgs84.exe
- rtkjob-ion.exe
- ntpsvr-2019-01-22-no-usrcheck.exe
- NtripCaster-2019-01-08.exe
- BACSTray.exe
- protect.exe
- hfs.exe
- jzmis.exe
- NewFileTime_x64.exe
- 2345MiniPage.exe
- JMJ_server.exe
- cacls.exe
- gpsdaemon.exe
- gpsusersvr.exe
- gpsdownsvr.exe
- gpsstoragesvr.exe
- gpsdataprocsvr.exe
- gpsftpd.exe
- gpsmysqld.exe
- gpstomcat6.exe
- gpsloginsvr.exe
- gpsmediasvr.exe
- gpsgatewaysvr.exe
- gpssvrctrl.exe
- zabbix_agentd.exe"
- BackupExec.exe
- Att.exe
- mdm.exe
- BackupExecManagementService.exe
- bengine.exe
- benetns.exe
- beserver.exe
- pvlsvr.exe
- bedbg.exe
- beremote.exe
- beremote.exe
- beremote.exe
- beremote.exe
- RemoteAssistProcess.exe
- BarMoniService.exe
- GoodGameSrv.exe
- BarCMService.exe
- TsService.exe
- GoodGame.exe
- BarServerView.exe
- IcafeServicesTray.exe
- BsAgent_0.exe
- ControlServer.exe
- DisklessServer.exe
- DumpServer.exe
- NetDiskServer.exe
- PersonUDisk.exe
- service_agent.exe
- SoftMemory.exe
- BarServer.exe
- RtkNGUI64.exe
- Serv-U-Tray.exe
- QQPCSoftTrayTips.exe
- SohuNews.exe
- Serv-U.exe
- QQPCRTP.exe
- EasyFZS.exe
- HaoYiShi.exe
- HysMySQL.exe
- wtautoreg.exe
- ispiritPro.exe
- CAService.exe
- XAssistant.exe
- TrustCA.exe
- GEUU20003.exe
- CertMgr.exe
- eSafe_monitor.exe
- MainExecute.exe
- FastInvoice.exe
- sesvc.exe
- ScanFileServer.exe
- Nuoadehgcgcd.exe
- OpenFastAssist.exe
- FastInvoiceAssist.exe
- Nuoadfaggcje.exe
- OfficeUpdate.exe
- atkexComSvc.exe
- FileTransferAgent.exe
- MasterReplicatorAgent.exe
- CrmAsyncService.exe
- CrmAsyncService.exe
- CrmUnzipService.exe
- NscAuthService.exe
- ReplicaReplicatorAgent.exe
- ASMCUSvc.exe
- OcsAppServerHost.exe
- RtcCdr.exe
- IMMCUSvc.exe
- DataMCUSvc.exe
- MeetingMCUSvc.exe
- QmsSvc.exe
- RTCSrv.exe
- pnopagw.exe
- NscAuth.exe
- Microsoft.ActiveDirectory.WebServices.exe
- DistributedCacheService.exe
- c2wtshost.exe
- Microsoft.Office.Project.Server.Calculation.exe
- schedengine.exe
- Microsoft.Office.Project.Server.Eventing.exe
- Microsoft.Office.Project.Server.Queuing.exe
- WSSADMIN.EXE
- hostcontrollerservice.exe
- noderunner.exe
- OWSTIMER.EXE
- wsstracing.exe
- mssearch.exe
- MySQLInstallerConsole.exe
- EXCEL.EXE
- consent.exe
- RtkAudioService64.exe
- RAVBg64.exe
- FNPLicensingService64.exe
- VisualSVNServer.exe
- MotionBoard57.exe
- MotionBoardRCService57.exe
- LPManService.exe
- RaRegistry.exe
- RaAutoInstSrv.exe
- RtHDVCpl.exe
- DefenderDaemon.exe
- BestSyncApp.exe
- ApUI.exe
- AutoUpdate.exe
- LPManNotifier.exe
- FieldAnalyst.exe
- TimingGenerate.exe
- Detector.exe
- Estimator.exe
- FA_Logwriter.exe
- TrackingSrv.exe
- cbInterface.exe
- ccbService.exe
- dbsrv16.exe
- KICManager.exe
- KICMain.exe
- ServerManagerLauncher.exe
- TbossGate.exe
- iusb3mon.exe
- MgrEnvSvc.exe
- Mysoft.Config.WindowsService.exe
- Mysoft.UpgradeService.UpdateService.exe
- hasplms.exe
- Mysoft.Setup.InstallService.exe
- Mysoft.UpgradeService.Dispatcher.exe
- Mysoft.DataCenterService.WindowsHost.exe
- Mysoft.DataCenterService.DataCleaning.exe
- Mysoft.DataCenterService.DataTracking.exe
- Mysoft.SchedulingService.WindowsHost.exe
- ServiceMonitor.exe
- Mysoft.SchedulingService.ExecuteEngine.exe
- AgentX.exe
- host.exe
- AutoUpdate.exe
- vsjitdebugger.exe"
- VBoxSDS.exe
- TeamViewer_Service.exe
- TeamViewer.exe
- CasLicenceServer.exe
- tv_w32.exe
- tv_x64.exe
- rdm.exe
- SecureCRTPortable.exe
- VirtualBox.exe
- VBoxSVC.exe
- VirtualBoxVM.exe
- abs_deployer.exe
- edr_monitor.exe
- sfupdatemgr.exe
- ipc_proxy.exe
- edr_agent.exe
- edr_sec_plan.exe
- sfavsvc.exe
- DataShareBox.ShareBoxMonitorService.exe
- DataShareBox.ShareBoxService.exe
- Jointsky.CloudExchangeService.exe
- Jointsky.CloudExchange.NodeService.ein
- perl.exe
- TsServer.exe
- AppMain.exe
- easservice.exe
- Kingdee6.1.exe
- QyKernel.exe
- QyFragment.exe
- ComputerZTray.exe
- ComputerZService.exe
- ClearCache.exe
- ProLiantMonitor.exe
- ChsIME.exe
- bugreport.exe
- GNWebServer.exe
- UI0Detect.exe
- GNCore.exe
- gnwayDDNS.exe
- GNWebHelper.exe
- php-cgi.exe
- ESLUSBService.exe
- CQA.exe
- Kekcoek.pif
- Tinuknx.exe
- servers.exe
- ping.exe
- TianHeng.exe
- K3MobileService.exe
- VSSVC.exe
- Xshell.exe
- XshellCore.exe
- FNPLicensingService.exe
- XYNTService.exe
- U8DispatchService.exe
- EISService.exe
- UFSoft.U8.Framework.EncryptManager.exe
- yonyou.u8.gc.taskmanager.servicebus.exe
- U8KeyManagePool.exe
- U8MPool.exe
- U8SCMPool.exe
- UFIDA.U8.Report.SLReportService.exe
- U8TaskService.exe
- U8TaskWorker.exe
- U8WebPool.exe
- U8AllAuthServer.exe
- UFIDA.U8.UAP.ReportService.exe
- UFIDA.U8.ECE.UTU.Services.exe
- U8WorkerService.exe
- UFIDA.U8.ECE.UTU.exe
- ShellStub.exe
- U8UpLoadTask.exe
- UfSysHostingService.exe
- UFIDA.UBF.SystemManage.ApplicationService.exe
- UFIDA.U9.CS.Collaboration.MailService.exe
- NotificationService.exe
- UBFdevenv.exe
- UFIDA.U9.SystemManage.SystemManagerClient.exe
- mongod.exe
- SpusCss.exe
- UUDesktop.exe
- KDHRServices.exe
- Kingdee.K3.Mobile.Servics.exe
- KDSvrMgrService.exe
- pdfServer.exe
- pdfspeedup.exe
- SufAppServer.exe
- Kingdee.K3.Mobile.LightPushService.exe
- iMTSSvcMgr.exe
- kdmain.exe
- KDActMGr.exe
- K3ServiceUpdater.exe
- Aua.exe
- iNethinkSQLBackup.exe
- auaJW.exe
- Scheduler.exe
- bschJW.exe
- SystemTray64.exe
- OfficeDaemon.exe
- OfficeIndex.exe
- OfficeIm.exe
- iNethinkSQLBackupConsole.exe
- OfficeMail.exe
- OfficeTask.exe
- OfficePOP3.exe
- apache.exe
- GnHostService.exe → Terminates the specified process and any child processes which were started by it.
- HwUVPUpgrade.exe → Terminates the specified process and any child processes which were started by it.
- "Kingdee.KIS.UESystemSer.exe" → Terminates the specified process and any child processes which were started by it.
- uvpmonitor.exe → Terminates the specified process and any child processes which were started by it.
- UVPUpgradeService.exe → Terminates the specified process and any child processes which were started by it.
- KDdataUpdate.exe → Terminates the specified process and any child processes which were started by it.
- Portal.exe → Terminates the specified process and any child processes which were started by it.
- U8SMSSrv.exe → Terminates the specified process and any child processes which were started by it.
- "Ufida.T.SM.PublishService.exe" → Terminates the specified process and any child processes which were started by it.
- lta8.exe → Terminates the specified process and any child processes which were started by it.
- UfSvrMgr.exe → Terminates the specified process and any child processes which were started by it.
- AutoUpdateService.exe → Terminates the specified process and any child processes which were started by it.
- MOM.exe → Terminates the specified process and any child processes which were started by it."
- where {Stopped Process 3}:
- PccNTMon.exe
- NTRtScan.exe
- TmListen.exe
- TmCCSF.exe
- TmProxy.exe
- TMBMSRV.exe
- TmPfw.exe
- CNTAoSMgr.exe
- sqlbrowser.exe
- sqlwriter.exe
- sqlservr.exe
- msmdsrv.exe
- MsDtsSrvr.exe
- sqlceip.exe
- fdlauncher.exe
- Ssms.exe
- SQLAGENT.EXE
- fdhost.exe
- fdlauncher.exe
- ReportingServicesService.exe
- msftesql.exe
- pg_ctl.exe
- postgres.exe
- UniFi.exe
- where {Stopped Process 4}:
- ThunderPlatform.exe
- pg_ctl.exe
- sqlservr.exe
- BackupExec.exe
- VBoxSDS.exe
- iexplore.exe
- Att.exe
- rcrelay.exe
- httpd.exe
- mdm.exe
- vm-agent.exe
- vm-agent-daemon.exe
- SogouImeBroker.exe
- mysqld.exe
- BackupExecManagementService.exe
- eSightService.exe
- TeamViewer_Service.exe
- java.exe
- CCenter.exe
- bengine.exe
- fdhost.exe
- cygrunsrv.exe
- TeamViewer.exe
- ScanFrm.exe
- benetns.exe
- wrapper.exe
- d_manage.exe
- fdlauncher.exe
- CasLicenceServer.exe
- nginx.exe
- beserver.exe
- reportingservicesservice.exe
- tv_w32.exe
- RsTray.exe
- pvlsvr.exe
- wampmanager.exe
- softmgrlite.exe
- node.exe
- tv_x64.exe
- bedbg.exe
- rdm.exe
- RavTray.exe
- sqlbrowser.exe
- beremote.exe
- SecureCRT.exe
その他
マルウェアは、以下を実行します。
- It encrypts files from local drives, removable drives, and network shares
- It connects to the following website to download and execute malicious module in memory to perform its malicious routine:
- http://{BLOCKED}.{BLOCKED}.{BLOCKED}.25/arx-Slkmrtswx_Vttmygcq.bmp
- It deletes the following services:
- Where {Services Deleted}:
- MsDtsServer
- MSSQL$SOPHOS
- MSSQLFDLauncher
- MSSQLSERVER
- MSSQLServerADHelper100
- MSSQLServerOLAPService
- ReportServer
- SQLAgent$SOPHOS
- "SQLANYs_sem5"
- SQLBrowser
- SQLSERVERAGENT
- SQLWriter
- B1LicenseService
- b1s50000
- b1s50001
- b1s50002
- B1ServerTools
- B1ServerTools64
- B1Workflow
- COMSysApp
- Gatekeeper64
- isapnp
- "SAP Business One RSP Agent Service"
- SBOClientAgent
- "SBODI_Server"
- SBOMail
- SBOWFDataAccess
- "vmickvpexchange"
- "vmicguestinterface"
- "vmicshutdown"
- "vmicheartbeat"
- "vmicrdv"
- "storflt"
- "vmictimesync"
- "vmicvss"
- "hvdsvc"
- "nvspwmi"
- "wmms"
- "AvgAdminServer"
- "AVG Antivirus"
- "avgAdminClient"
- "SAVService"
- "SAVAdminService"
- "Sophos AutoUpdate Service"
- "Sophos Clean Service"
- "Sophos Device Control Service"
- "Sophos Endpoint Defense Service"
- "Sophos File Scanner Service"
- "Sophos Health Service"
- "Sophos MCS Agent"
- "Sophos MCS Client"
- "SntpService"
- "swc_service"
- "swi_service"
- "Sophos UI"
- "swi_update"
- "Sophos Web Control Service"
- "Sophos System Protection Service"
- "Sophos Safestore Service"
- "hmpalertsvc"
- "RpcEptMapper"
- "Sophos Endpoint Defense Service"
- "SophosFIM"
- "swi_filter"
- "FirebirdGuardianDefaultInstance"
- "FirebirdServerDefaultInstance"
- "MSSQLFDLauncher"
- "MSSQLSERVER"
- "SQLSERVERAGENT"
- "SQLBrowser"
- "SQLTELEMETRY"
- "MsDtsServer130"
- "SSISTELEMETRY130"
- "SQLWriter"
- "MSSQL$VEEAMSQL2012"
- "SQLAgent$VEEAMSQL2012"
- "MSSQL"
- "SQLAgent"
- "MSSQLServerADHelper100"
- "MSSQLServerOLAPService"
- "MsDtsServer100"
- "ReportServer"
- "SQLTELEMETRY$HL"
- "TMBMServer"
- "MSSQL$PROGID"
- "MSSQL$WOLTERSKLUWER"
- "SQLAgent$PROGID"
- "SQLAgent$WOLTERSKLUWER"
- "MSSQLFDLauncher$OPTIMA"
- "MSSQL$OPTIMA"
- "SQLAgent$OPTIMA"
- "ReportServer$OPTIMA"
- "msftesql$SQLEXPRESS"
- "postgresql-x64-9.4"
- "WRSVC"
- "ekrn"
- "ekrnEpsw"
- "klim6"
- "AVP18.0.0"
- "KLIF"
- "klpd"
- "klflt"
- "klbackupdisk"
- "klbackupflt"
- "klkbdflt"
- "klmouflt"
- "klhk"
- "KSDE1.0.0"
- "kltap"
- "ScSecSvc"
- "Core Mail Protection"
- "Core Scanning Server"
- "Core Scanning ServerEx"
- "Online Protection System"
- "RepairService"
- "Core Browsing Protection"
- "Quick Update Service"
- "McAfeeFramework"
- "macmnsvc"
- "masvc"
- "mfemms"
- "mfevtp"
- "TmFilter"
- "TMLWCSService"
- "tmusa"
- "TmPreFilter"
- "TMSmartRelayService"
- "TMiCRCScanService"
- "VSApiNt"
- "TmCCSF"
- "tmlisten"
- "TmProxy"
- "ntrtscan"
- "ofcservice"
- "TmPfw"
- "PccNTUpd"
- "PandaAetherAgent"
- "PSUAService"
- "NanoServiceMain"
- "EPIntegrationService"
- "EPProtectedService"
- "EPRedline"
- "EPSecurityService"
- "EPUpdateService"
- "UniFi"
- "XT800Service_Personal"
- "DAService_TCP"
- "eCard-TTransServer"
- eCardMPService
- EnergyDataService
- UI0Detect
- OracleOraDb11g_home1ClrAgent
- K3MobileService
- QcSoftService
- OracleOraDb11g_home1TNSListener
- "UWS LoPriv Services"
- TCPIDDAService
- ftnlsv3
- VMTools
- ftnlses3
- MSCRMAsyncService
- WebAttendServer
- OracleVssWriterORCL
- VGAuthService
- OracleServiceORCL
- REPLICA
- FxService
- MSDTC
- UIODetect
- RTCATS
- aspnet_state @Redis
- "wanxiao-monitor"
- TeamViewer
- RTCAVMCU
- "UtilDev Web Server Pro"
- JhTask
- RabbitMQ
- ftusbrdwks
- RtcQms
- VMAuthdService
- "AHS SERVICE"
- ftusbrdsrv
- ImeDictUpdateService
- RTCMEETINGMCU
- "Sense Shield Service"
- "ZTE USBIP Client Guard"
- VMUSBArbService
- "ZTE USBIP Client"
- SSMonitorService
- MCService
- "ZTE FileTranS"
- VMwareHostd
- RTCIMMCU
- SSSyncService
- "vm-agent"
- TPlusStdAppService1300
- VmAgentDaemon
- OpenSSHd
- MSSQL$SQL2008
- wwbizsrv
- RTCDATAMCU
- eSightService
- qemu-ga
- allpass_redisservice_port21160
- apachezt
- SQLAgent$SQL2008
- RTCCDR
- "Flash Helper Service"
- AlibabaProtect
- Jenkins
- TPlusStdTaskService1300
- ZTEVdservice
- TPlusStdUpgradeService1300
- ProjectEventService16
- kbasesrv
- "Kiwi Syslog Server"
- ProjectQueueService16
- secbizsrv
- "UWS HiPriv Services"
- VirboxWebServer
- MMRHookService
- SPAdminV4
- SQLTELEMETRY
- OracleJobSchedulerORCL
- MSMQ
- jhi_service
- SPSearchHostController
- IpOverUsbSvc
- smtpsvrJT
- LMS
- SPTimerV4
- zyb_sync
- MsDtsServer100
- "FontCache3.0.0.0"
- SPTraceV4
- KuaiYunTools
- 360EntHttpServer
- KMSELDI
- 360EntSvc
- "OSP Service"
- OSearch16
- 360EntClientSvc
- btPanel
- NFWebServer
- Protect_2345Explorer
- ProjectCalcService16
- wampapache
- c2wts
- 2345PicSvc
- MSSEARCH
- vmware-converter-agent
- AppFabricCachingService
- msftesql
- ADWS
- vmware-converter-server
- "SyncBASE Service"
- vmware-converter-worker
- MotionBoard57
- OracleDBConcoleorcl
- MotionBoardRCService57
- QQCertificateService
- OracleRemExecService
- GPSDaemon
- vsvnjobsvc
- GPSUserSvr
- OracleMTSRecoveryService
- VisualSVNServer
- GPSDownSvr
- "FlexNet Licensing Service 64"
- BestSyncSvc
- GPSStorageSvr
- LPManager
- GPSDataProcSvr
- MediatekRegistryWriter
- GPSGatewaySvr
- GPSMediaSvr
- RaAutoInstSrv_RT2870
- GPSLoginSvr
- CobianBackup10
- SQLANYs_sem5
- GPSTomcat6
- CASLicenceServer
- GPSMysqld
- SQLService
- GPSFtpd
- semwebsrv
- "Zabbix Agent"
- TbossSystem
- BackupExecAgentAccelerator
- ErpEnvSvc
- Mysoft.Autoupgrade.DispatchService
- bedbg
- Mysoft.Autoupgrade.UpdateService
- BackupExecDeviceMediaService
- BackupExecRPCService
- BackupExecAgentBrowser
- Mysoft.Config.WindowsService
- Mysoft.DataCenterService
- BackupExecJobEngine
- Mysoft.SchedulingService
- BackupExecManagementService
- Mysoft.Setup.InstallService
- MDM
- MysoftUpdate
- TxQBService
- edr_monitor
- Gailun_Downloader
- abs_deployer
- RemoteAssistService
- savsvc
- ShareBoxMonitorService
- YunService
- ShareBoxService
- Serv-U
- CloudExchangeService
- "EasyFZS Server"
- "Rpc Monitor"
- "U8WorkerService2"
- OpenFastAssist
- CIS
- EASService
- "Nuo Update Monitor"
- "Daemon Service"
- KICkSvr
- asComSvc
- OfficeUpdateService
- RtcSrv
- U8SmsSrv
- OfficeClearCache
- RTCASMCU
- FTA
- TurboCRM70
- MASTER
- U8DispatchService
- NscAuthService
- U8EISService
- MSCRMUnzipService
- U8EncryptService
- U8GCService
- MSCRMAsyncService$maintenance
- U8KeyManagePool
- "U8MPool"
- U8SCMPool
- U8SLReportService
- U8TaskService
- "U8WebPool"
- UFAllNet
- UFReportService
- UTUService
- "U8WorkerService1"
ランサムウェアの不正活動
マルウェアは、ファイル名に以下の文字列を含むファイルの暗号化はしません。
- desktop.ini
- ntuser.dat
- thumbs.db
- iconcache.db
- ntuser.ini
- ntldr
- bootfont.bin
- ntuser.dat.log
- bootsect.bak
- boot.ini
- autorun.inf
- debugLog.txt
- MSBuild.exe
- RECOVERY FILES.txt
マルウェアは、ファイルパスに以下の文字列を含むファイルの暗号化はしません。
- msocache
- $windows.~ws
- system volume information
- intel
- appdata
- perflogs
- programdata
- application data
- tor browser
- boot
- $windows.~bt
- mozilla
- boot
- windows.old
- Windows Microsoft.NET
- WindowsPowerShell
- Windows NT
- Windows
- Common Files
- Microsoft Security Client
- Internet Explorer
- Reference
- Assemblies
- Windows Defender
- Microsoft ASP.NET
- Core Runtime
- Package
- Store
- Microsoft Help Viewer
- Microsoft MPI
- Windows Kits
- Microsoft.NET
- Windows Mail
- Microsoft Security Client
- Package Store
- Microsoft Analysis Services
- Windows Portable Devices
- Windows Photo Viewer
- Windows Sidebar
マルウェアは、暗号化されたファイルのファイル名に以下の拡張子を追加します。
- .FARGO3
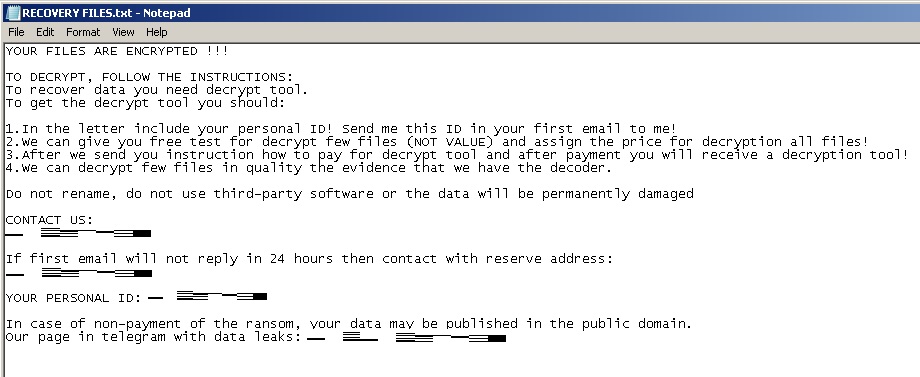
マルウェアは、以下の内容を含む脅迫状のテキストファイルを残します。
- {Drive Letter:}\RECOVERY FILES.txt
- {Encrypted Directory:}\RECOVERY FILES.txt
対応方法
手順 1
Windows 7、Windows 8、Windows 8.1、および Windows 10 のユーザは、コンピュータからマルウェアもしくはアドウェア等を完全に削除するために、ウイルス検索の実行前には必ず「システムの復元」を無効にしてください。
手順 2
このマルウェアもしくはアドウェア等の実行により、手順中に記載されたすべてのファイル、フォルダおよびレジストリキーや値がコンピュータにインストールされるとは限りません。インストールが不完全である場合の他、オペレーティングシステム(OS)の条件によりインストールがされない場合が考えられます。手順中に記載されたファイル/フォルダ/レジストリ情報が確認されない場合、該当の手順の操作は不要ですので、次の手順に進んでください。
手順 3
Windowsをセーフモードで再起動します。
手順 4
このレジストリ値を削除します。
警告:レジストリはWindowsの構成情報が格納されているデータベースであり、レジストリの編集内容に問題があると、システムが正常に動作しなくなる場合があります。
レジストリの編集はお客様の責任で行っていただくようお願いいたします。弊社ではレジストリの編集による如何なる問題に対しても補償いたしかねます。
レジストリの編集前にこちらをご参照ください。
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Lcudsgjlb = %Application Data%\Syfwfpwux\Lcudsgjlb.exe
- Lcudsgjlb = %Application Data%\Syfwfpwux\Lcudsgjlb.exe
手順 5
以下のファイルを検索し削除します。
- %User Temp%\Logrpaqfriixribkill$.bat
- {Drive Letter:}\RECOVERY FILES.txt
- {Encrypted Directory:}\RECOVERY FILES.txt
手順 6
以下のフォルダを検索し削除します。
- %Application Data%\Syfwfpwux
手順 7
コンピュータを通常モードで再起動し、最新のバージョン(エンジン、パターンファイル)を導入したウイルス対策製品を用い、「Ransom.MSIL.TARGETCOMP.THHBBBB」と検出したファイルの検索を実行してください。 検出されたファイルが、弊社ウイルス対策製品により既に駆除、隔離またはファイル削除の処理が実行された場合、ウイルスの処理は完了しており、他の削除手順は特にありません。
手順 8
以下のファイルをバックアップを用いて修復します。なお、マイクロソフト製品に関連したファイルのみ修復されます。このマルウェア/グレイウェア/スパイウェアが同社製品以外のプログラムをも削除した場合には、該当プログラムを再度インストールする必要があります。
ご利用はいかがでしたか? アンケートにご協力ください

