HKTL_REINLOG.GB
a variant of Win32/PSW.QQPass.DU trojan(ESET-NOD32)
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be manually installed by a user.
It uses a user interface (UI).
TECHNICAL DETAILS
Arrival Details
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be manually installed by a user.
Other Details
This hacking tool uses the following user interfaces (UIs):
It does the following:
- Send reports to certain smtp servers when the first button is clicked:
- smtp.{user input}.com
- Generate an executable and .ini file when the second button is clicked:
A dialog box will be displayed to give the user the option to choose the location and name the generated file.- {user chosen path}\{user-defined file name}.exe - detected as TSPY_KEYLOG.NTS
- config.ini - storage of user data, deleted after use
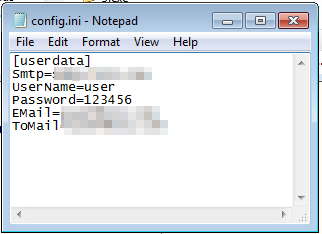
- Stores the entered email and password
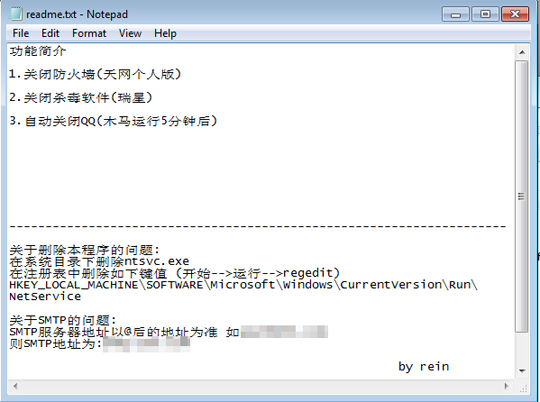
- Displays a text file that contains the features and how to remove the generated file TSPY_KEYLOG.NTS when the third button is clicked:
- readme.txt - deleted after opening with notepad.exe
NOTES:
This hacking tool uses Simplified Chinese language.
It tries to locate and load the following as libraries:
- {hacking tool path and name}.EN
- {hacking tool path and name}.ENU
It requires the correct user name and password for the reporting routine. It has links to the website www.hackbase.com.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as HKTL_REINLOG.GB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



