HTML_FAKEPAY.III
Mal/Phish-A (Sophos)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Spyware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This spyware executes when a user accesses certain websites where it is hosted.
TECHNICAL DETAILS
Arrival Details
This spyware executes when a user accesses certain websites where it is hosted.
Stolen Information
This spyware sends the gathered information via HTTP POST to the following URL:
- http://{BLOCKED}o70.com/form.php
- http://{BLOCKED}rp.com/x/userrpd.php
- http://{BLOCKED}ardo.cl/w.php
NOTES:
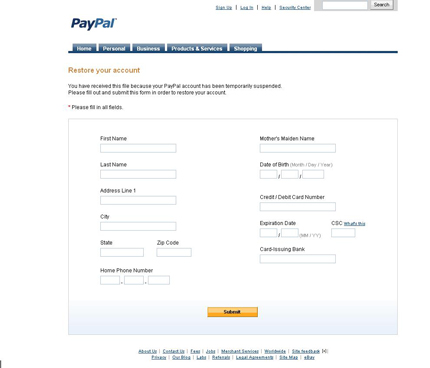
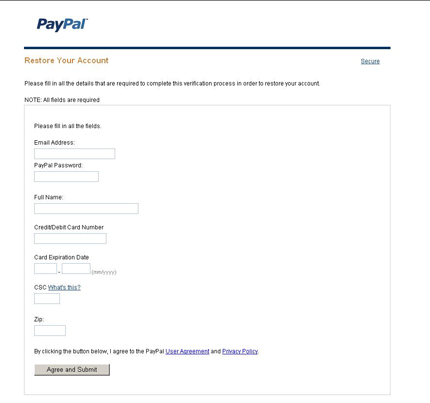
This is Trend Micro's detection for malicious phishing pages targeting Paypal users. It disguises itself as various PayPal user account forms such as account restoration form, account reactivation form, and personal profile form, thus, stealing all the information a user inputs, including credit card information. Below are sample screenshots:
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as HTML_FAKEPAY.III. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.