TrojanSpy.Win32.CASBANEIRO.RG
Windows


Threat Type: Trojan Spy
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system. It connects to a website to send and receive information.
It logs a user's keystrokes to steal information.
TECHNICAL DETAILS
Arrival Details
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan Spy drops the following files:
- %Public%\Documents\HOME.tmp
(Note: %Public% is the folder that serves as a repository of files or folders common to all users, which is usually C:\Users\Public in Windows Vista, 7, and 8.)
It adds the following processes:
- https://{BLOCKED}licalcados.shop/modulo/ → if %Public%\Documents\HOME.tmp does not exist
Autostart Technique
This Trojan Spy adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Car{5 Random Characters} = {Loader File Path}\{Loader File Name}.exe
Backdoor Routine
This Trojan Spy executes the following commands from a remote malicious user:
- <|ALINHA_TELA|>
- <|BEST|>
- <|CARGASI|>
- <|FECHAR_RECORTE|>
- <|FECHASI_TELA|>
- <|KEYBOARD|>
- <|OK|> → Send an <|Info|> packet back to the C2 server
- <|PING|> → Heartbeat command that sends <|PONG|> packet back to the C2 server
- <|PRINCIPAL|>
- <|QUADRADO_FECHADO|>
- <|RECCCCCC|>
- <|RECORT2018|>
- <|RECORT2020|>
- <|RECVS|>
- <|REQUESTKEYBOARD|>
- <|TAMANHO|>
- Execute Arbitrary Commands
It connects to the following websites to send and receive information:
- http://{BLOCKED}e.com.br/AEIOU/index.php?#HGUYG6758765vUHVUYIV
- http://{BLOCKED}stalar.me/brstorm/getdata.php
- http://{BLOCKED}stalar.me/messages.zip
- http://{BLOCKED}ydesk.online/xxx.txt
- https://{BLOCKED}ogle.com/document/u/0/export?format=txt&id={BLOCKED}9jQYFPhwJfSSR6g67XDroAJeyuofLD4KiDsB_M
- https://{BLOCKED}ogle.com/document/u/0/export?format=txt&id={BLOCKED}rXM-ISJrLq3fiFgDag9KUdUnZb3QIo6VJYBWno
- https://{BLOCKED}ogle.com/document/u/0/export?format=txt&id={BLOCKED}TMf-t6z0AVQuZIagntGVtfEX4FiFFGkHp99NTYk
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}Mfx_Ed_XRm0veUu8cvKDt3pgsBii3nzbNO1V-o
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}nOq3uCrnken6nxpsV7doKZddt1Pe6ENIWTreW0
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}n3o4Ncjt2A7l0QYyO-WHmfXGzAVP5-EqiqoOUo
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}qJD792RDtAgMYd3xt0yiOHprfQKynu1yIK6P0Q
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}wbY_5WouaywEKCaSclTZHznClfuO9FTigbqKQ
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}7oXDFhR9OjcydAWd7HtUAPz4bbBdoTI0xu3gU
- https://{BLOCKED}ogle.com/document/u/4/export?format=txt&id={BLOCKED}nPbKNR35VUkgnzk06sqNgXLuY_3RuRfxTVc8aw
- https://{BLOCKED}ogle.com/file/d/{BLOCKED}Y494DvAuW1XNV6ANNdhUgeycVjq3H/view
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}iHcpW41LVyRB0sefNrst7hKAzl0&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}yR6VHERIPpdO6MrV3fh7qadvqI-&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}d5jnMcF1PJ_jZqfPiI4ZjuwMatn&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}bNcPqKKMjTUmaNU7NmiFwhF3jfJ&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}W-fUhIu121-dffSkd2zJonTmC0&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}p3XGdauZjlbTD8HUAUEWt79oxno&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}wA8bBF8r0RLQPQtNp4F4OTDCiJG&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}ZQ9H1cF0A6axJnF08XRLKtWqnVk&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}Q0qWN70oY6QIbVXJK7u40A2Re4R&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}WPCgS7PcQhKZieAdXWgD3iyeTFQ&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}4B5r3Eulp7Z_dJu9ZayAh46P5iH&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}fDHEbJlkieTSi9f8iYmHsAY1lk&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}ycVl8nvqo6XO-ClJ4OMnOnDWxSq&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}Btodcroz8-LPk8MSEvvu9VU888e&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}X6NpOM7NLUEHSQmnBkRmtr9o6tz&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}wqX3rF3QEQXNjH_jcZqPLiWy2uz&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}kltSIkaHP-_1XHDQqW44pndIpNG&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}JOXSBQvqqpuc9-PO9KlJ5Byji52&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}UCl3TRBX_QqpZ21GjAofB88RPvn&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}T3mTWGhlnUnGFAH7MerS6jXMXM9&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}vuVEeT7HqFOp28jzTfamTx3CBh4&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}iBsbzOgPi4nL2WoGcJq5yIL8&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}Z-Swx9HkizMi8VG3lf8nKNxhJtj&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}F2rWfDJdZcWUjOE2kiVI-bCFyHP&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}ZJJmomAT9Wiqfz6YHSrdw-9pCQa&export=download
- https://{BLOCKED}oogle.com/uc?authuser=0&id={BLOCKED}vVBYyB-qfHa-hc9nPdlWq9JsId&export=download
Information Theft
This Trojan Spy gathers the following data:
- From the infected machine:
- OS version
- OS architecture (32-bit or 64-bit)
- Computer Name
- User Name
- IP and Geolocation of the Infected machine
- Screenshot of the Affected System
- From the user:
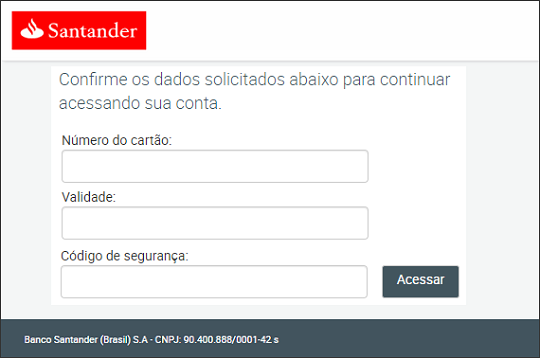
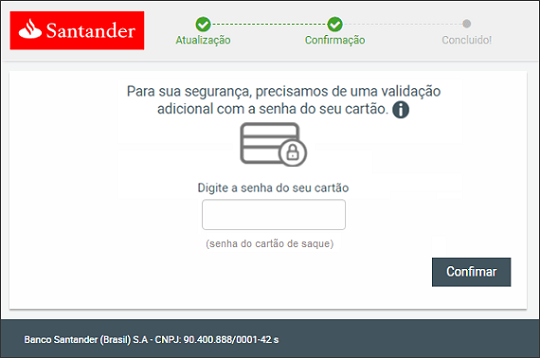
- Banking credentials (i.e. username, password, security code, etc.)
It logs a user's keystrokes to steal information.
Other Details
This Trojan Spy does the following:
- It requires to be decrypted by its loader in order to run successfully.
- It connects to the following URL to identify the affected machine's geolocation:
- http://{BLOCKED}i.com/json/
- It can start or stop the Desktop Window Manager using the following commands:
- cmd.exe /C net start uxsms
- cmd.exe /C net stop uxsms
- It can hide and unhide the Windows task bar.
- It can control and simulate mouse clicks and movements.
- It can restart the affected system.
- It can delete the following folders:
- %ProgramData\nameAPP
- %ProgramData\nameCAIXA
- %ProgramData\regita
- %ProgramData\reg8
- %ProgramData\namePC
- %ProgramData\txtA
- %ProgramData\txtC
- It can terminate the following processes:
- c6bank.exe
- iexplore.exe
- firefox.exe
- chrome.exe
- opera.exe
- office.exe
- AplicativoBradesco.exe
- itauaplicativo.exe
- MicrosoftEde.exe
- MicrosoftEdgeCP.exe
- NavegadorExclusivoBradesco.exe
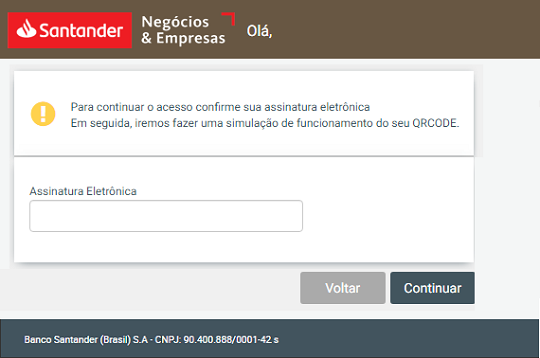
- It monitors if the victim will access specific banking websites and create an overlay window over the legitimate web browser window and connect them to the C&C server.
- It identifies specific bank/banking-related websites by looking for the following strings:
- © Santander
- © Banco do Brasil
- santander
- banco do brasil
- bancobrasil.com.br
- bb clt
- auto atendimento banco do brasil
- bb pj
- netbankingcai
- internet banking
- ofertas para empresas
- sicoob es
- - sicoob -
- sicoobnet
- sistema de cooperativas de crédito
- banco do nordeste
- mercado bitcoin
- banco mufg brasil
- abc brasil
- unicred
- cresol
- banco paulista
- credisis
- pagueveloz
- banese
- banco original
- banco digital
- superdigital
- banco sofisa direto
- safrapay
- pine online
- Banco Sofisa
- credit suisse
- tribanco online
- banco da amazônia
- advanced - painel de clientes
- banco alfa
- contasuper
- conta super empresas
- desbank
- banco sofisa direto
- btg pactual
- bem vindo ao seu bmg
- login | ativa investimentos
- ibi on-line
- acesso restrito - banco cedula
- banco cetelem
- fair corretor
- banco fibra
- banco industrial do brasil
- bem-vindo ao seu banco
- keb hana
- banco luso
- bancornx
- modal banking
- banking
- bancogenial
- banco genial
- banco paulista
- banco pine
- banco brp
- bancosemear
- e-moneyger
- banco topazio
- tribanco
- banco tricury
- cecoop
- ccb brasil
- cm capital
- login corporate
- credisan
- extrato associados
- credsol
- home - frete corretora
- getmoney
- guide|login
- nova futura
- nbc bank
- omni - area do cliente
- cadastro|parmetal
- banco|senff
- servicoop
- travelex bank
- uniprime central nacional
- banco fidis
- psa banco
- banco randon
- finamax
- santinvest - home
- fitbank
- hiperbanco
- conta digital
- bandeprev
- bocom bbm
- banda da amazônia
- banco fibra
- banco industrial
- netbaking
- banco master
- banco mufg
- banco rendimento
- grafeno
- binance
- novadax
- bitcoin
- criptomoedas
- bitypreco
- cripto
- btg empresas
- banco safra
- efi - login
- mercado pago
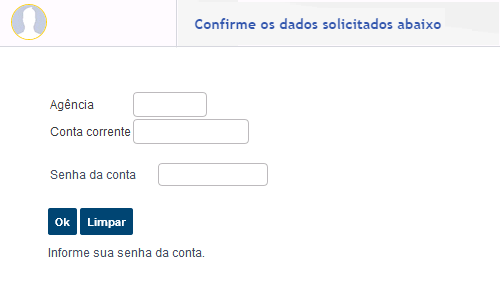
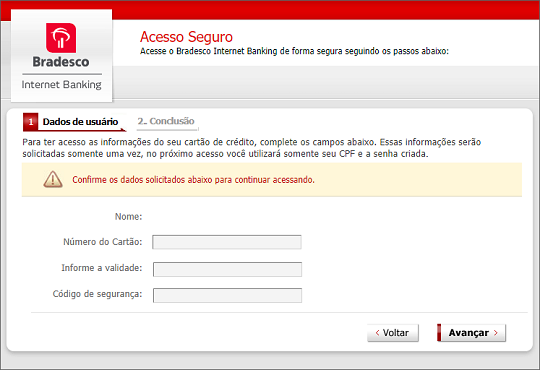
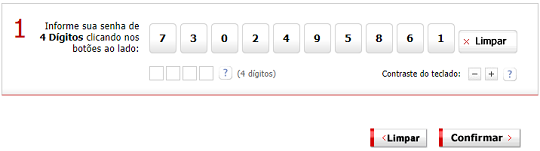
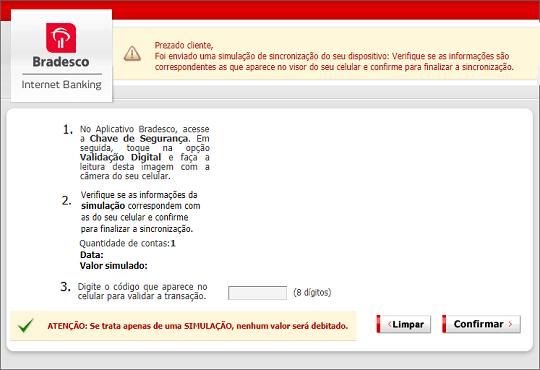
- The following are samples of the overlay that the malware will create:
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Car{5 Random Characters} = {Loader File Path}\{Loader File Name}.exe
- Car{5 Random Characters} = {Loader File Path}\{Loader File Name}.exe
Step 5
Search and delete this file
- %Public%\Documents\HOME.tmp
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TrojanSpy.Win32.CASBANEIRO.RG. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



