TSPY_FAKEPUT.A
Trojan:Win32/Modputty.A (Microsoft); Hacktool (Symantec)
Windows


Threat Type: Spyware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This spyware may be unknowingly downloaded by a user while visiting malicious websites.
TECHNICAL DETAILS
Arrival Details
This spyware may be unknowingly downloaded by a user while visiting malicious websites.
NOTES:
It retrieves the following information of the machine/server intended to access using Putty:
- IP Address/Domain
- Username
- Password
- Port
It uses the string format ssh://{username}:{password}@{IP address/domain}:{port}.
The malware is encoded to Base64 for encryption then concatenated to URL and finally sent to the following URL:
- http://{BLOCKED}-uro.ru/get/index.php?record={encoded base64 stolen information}
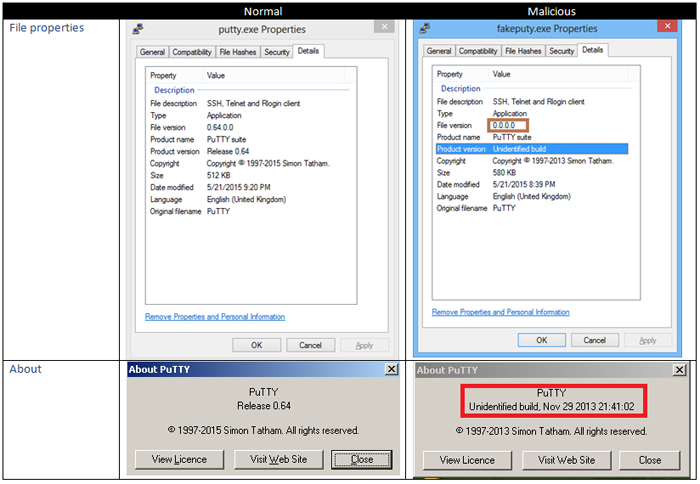
In comparison, the GUI and File icon of the normal Putty and malicious Putty may be similar.
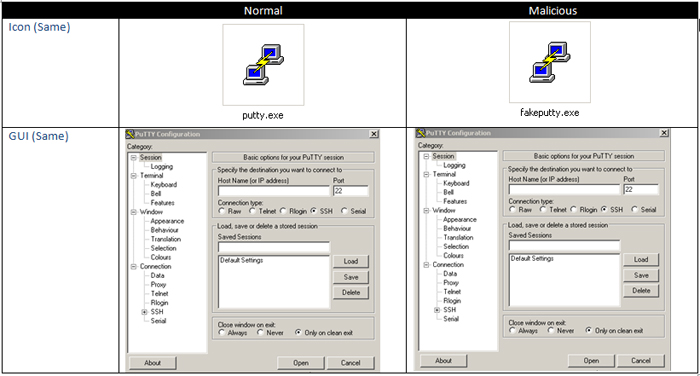 We can determine their differences by checking file properties and clicking the about button in the GUI.
We can determine their differences by checking file properties and clicking the about button in the GUI.
SOLUTION
Scan your computer with your Trend Micro product to delete files detected as TSPY_FAKEPUT.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


