TROJ_QADARS.BZ
Win32/Qadars.AX (ESET-NOD32); Trojan:Win32/Sopinar.F!bit (Microsoft)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be manually installed by a user.
It does not have any propagation routine.
It does not have any backdoor routine.
It connects to certain websites to send and receive information.
TECHNICAL DETAILS
322,560 bytes
EXE
Yes
24 Feb 2017
Connects to URLs/IPs
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be manually installed by a user.
Installation
This Trojan adds the following mutexes to ensure that only one of its copies runs at any one time:
- {Generated Hash of the file}
It injects codes into the following process(es):
- svchost.exe
Propagation
This Trojan does not have any propagation routine.
Backdoor Routine
This Trojan does not have any backdoor routine.
Other Details
This Trojan connects to the following website to send and receive information:
- hxxp://{Random Domain}.{com|net|org}/report.php
It uses domain generation algorithm (DGA) for its C&C servers.
It does the following:
- It checks the following registry and terminates itself if found:
- HKEY_LOCAL_MACHINE\Software\KasperskyLab
- HKEY_LOCAL_MACHINE\Software\AVG
- Sends the following information to its CnC:
- Bot ID
- OS Version
- Bot Version
- It gathers installed applications by enumerating DisplayName entries in the following registry entry:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall
- It may download additional modules from its server. However as of this writing, there was no successful connection to the server.
- It executes the following commands:
%System%\netsh.exe advfirewall firewall add rule name="svchost.exe" dir=in action=allow program="%System%\svchost.exe" enable=yes
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
NOTES:
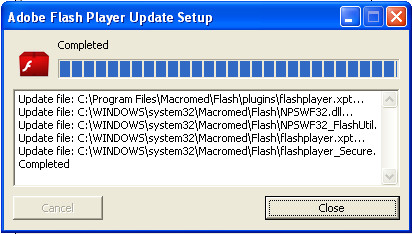
Upon execution it displays the following user interface to trick the user that it is a legitimate application.
It does not have rootkit capabilities.
It does not exploit any vulnerability.
SOLUTION
9.850
13.256.04
04 Mar 2017
13.257.00
05 Mar 2017
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Restart in Safe Mode
Step 3
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_QADARS.BZ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

