TROJ_FAKEAV.FKQ
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to a website to send and receive information.
It displays fake alerts that warn users of infection. It also displays fake scanning results of the affected system. It then asks for users to purchase it once scanning is completed. If users decide to purchase the rogue product, users are directed to a certain website asking for sensitive information, such as credit card numbers. When users agree to buy the software, it connects to a certain URL.
TECHNICAL DETAILS
Varies
EXE
Yes
19 Jan 2012
Drops files, Terminates processes, Displays graphics/image, Connects to URLs/IPs
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following component file(s):
- %User Profile%\Application Data\Microsoft\Internet Explorer\Quick Launch\System Check.lnk
- %User Profile%\Desktop\System Check.lnk
- %User Profile%\Start Menu\Programs\System Check\System Check.lnk
- %User Profile%\Start Menu\Programs\System Check\Uninstall System Check.lnk
- %System Root%\Documents and Settings\All Users\Application Data\{random}
- %System Root%\Documents and Settings\All Users\Application Data\~{random}
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.. %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.)
It drops and executes the following files:
- %System Root%\Documents and Settings\All Users\Application Data\{random 1}.exe - also detected as TROJ_FAKEAV.FKQ
- %System Root%\Documents and Settings\All Users\Application Data\{random 2}.exe - also detected as TROJ_FAKEAV.FKQ
(Note: %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.)
It creates the following folders:
- %User Profile%\Start Menu\Programs\System Check
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.)
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
{random}.exe = "%System Root%\Documents and Settings\All Users\Application Data\{random}.exe"
Other System Modifications
This Trojan modifies the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Hidden = "0"
(Note: The default value data of the said registry entry is 1.)
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
ShowSuperHidden = "0"
(Note: The default value data of the said registry entry is 1.)
HKEY_CURRENT_USER\Software\Microsoft\
Internet Explorer\Download
CheckExeSignatures = "no"
(Note: The default value data of the said registry entry is yes.)
HKEY_USERS\S-1-5-21-117609710-764733703-839522115-500\Software\
Microsoft\Internet Explorer\Download
CheckExeSignatures = "no"
(Note: The default value data of the said registry entry is yes.)
It also creates the following registry entry(ies) as part of its installation routine:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
TaskbarGlomming = "2"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
TaskbarGlomming = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowUser = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowControlPanel = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowHelp = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowMyComputer = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowMyDocs = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowMyMusic = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowMyGames = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowMyPics = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowPrinters = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowRecentDocs = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowRun = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowSearch = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
ActiveDesktop
HidNoChangingWallPaperden = "1"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Associations
LowRiskFileTypess = ".zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;.scr;"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Attachments
SaveZoneInformation = "1"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = "1"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoDesktop = "1"
HKEY_CURRENT_USER\Control Panel
5761b2dc-ce77-4bfa-b965-6f33b1867cf2 =
HKEY_CURRENT_USER\Control Panel
7f6b3266-31c5-43a8-9547-e7911ad6fb33 =
HKEY_CURRENT_USER\Control Panel
nsreg = "4f18ff82"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer
EnableAutoTray = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowSetProgramAccessAndDefaults = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowNetConn = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Start_ShowNetPlaces = "0"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\policies\
system
DisableTaskMgr = "1"
Backdoor Routine
This Trojan connects to the following websites to send and receive information:
- {BLOCKED}ber.com
- {BLOCKED}dthihtu.com
- {BLOCKED}igol.com
- {BLOCKED}gytorrent.com
- {BLOCKED}s.com
- {BLOCKED}taltv.com
Process Termination
This Trojan terminates the following processes if found running in the affected system's memory:
- taskmgr.exe
- procexp.exe
- regedit.exe
- MSAScui.exe
Rogue Antivirus Routine
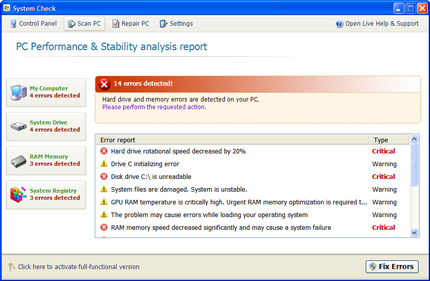
This Trojan displays fake alerts that warn users of infection. It also displays fake scanning results of the affected system. It then asks for users to purchase it once scanning is completed. If users decide to purchase the rogue product, users are directed to a certain website asking for sensitive information, such as credit card numbers.
When users agree to buy the software, it connects to the following URL to continue the purchase:
- http://{BLOCKED}ber.com/customers/buy.php
- http://{BLOCKED}dthihtu.com/customers/buy.php
- http://{BLOCKED}igol.com/customers/buy.php
- http://{BLOCKED}gytorrent.com/customers/buy.php
- http://{BLOCKED}s.com/customers/buy.php
- http://{BLOCKED}taltv.com/customers/buy.php
- http://{BLOCKED}s.com/customers/buy.php
NOTES:
It displays the following fake antivirus user interface:
It changes the attributes of the files in the system to Hidden. This routine tricks the user that the system has serious hardware problem.
SOLUTION
9.200
8.716.07
19 Jan 2012
8.717.00
19 Jan 2012
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product and note files detected as TROJ_FAKEAV.FKQ
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- {random}.exe = "%System Root%\Documents and Settings\All Users\Application Data\{random}.exe"
- {random}.exe = "%System Root%\Documents and Settings\All Users\Application Data\{random}.exe"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- TaskbarGlomming = "0"
- TaskbarGlomming = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- TaskbarGlomLevel = "2"
- TaskbarGlomLevel = "2"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowUser = "0"
- Start_ShowUser = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowControlPanel = "0"
- Start_ShowControlPanel = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowHelp = "0"
- Start_ShowHelp = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowMyComputer = "0"
- Start_ShowMyComputer = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowMyDocs = "0"
- Start_ShowMyDocs = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowMyMusic = "0"
- Start_ShowMyMusic = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowMyGames = "0"
- Start_ShowMyGames = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowMyPics = "0"
- Start_ShowMyPics = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowPrinters = "0"
- Start_ShowPrinters = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowRecentDocs = "0"
- Start_ShowRecentDocs = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowRun = "0"
- Start_ShowRun = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowSearch = "0"
- Start_ShowSearch = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop
- HidNoChangingWallPaperden = "1"
- HidNoChangingWallPaperden = "1"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations
- LowRiskFileTypess = ".zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;.scr;"
- LowRiskFileTypess = ".zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;.scr;"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments
- SaveZoneInformation = "1"
- SaveZoneInformation = "1"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System
- DisableTaskMgr = "1"
- DisableTaskMgr = "1"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
- NoDesktop = "1"
- NoDesktop = "1"
- In HKEY_CURRENT_USER\Control Panel
- 5761b2dc-ce77-4bfa-b965-6f33b1867cf2
- 5761b2dc-ce77-4bfa-b965-6f33b1867cf2
- In HKEY_CURRENT_USER\Control Panel
- 7f6b3266-31c5-43a8-9547-e7911ad6fb33
- 7f6b3266-31c5-43a8-9547-e7911ad6fb33
- In HKEY_CURRENT_USER\Control Panel
- nsreg = "4f18ff82"
- nsreg = "4f18ff82"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer
- EnableAutoTray = "0"
- EnableAutoTray = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowSetProgramAccessAndDefaults = "0"
- Start_ShowSetProgramAccessAndDefaults = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowNetConn = "0"
- Start_ShowNetConn = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Start_ShowNetPlaces = "0"
- Start_ShowNetPlaces = "0"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system
- DisableTaskMgr = "1"
- DisableTaskMgr = "1"
Step 5
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- From: Hidden = "0"
To: Hidden = "1"
- From: Hidden = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- From: ShowSuperHidden = "0"
To: ShowSuperHidden = "1"
- From: ShowSuperHidden = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download
- From: CheckExeSignatures = "no"
To: CheckExeSignatures = "yes"
- From: CheckExeSignatures = "no"
Step 6
Search and delete the file detected as TROJ_FAKEAV.FKQ
Step 7
Search and delete this folder
Step 8
Search and delete these files
%User Profile%\Desktop\System Check.lnk
%System Root%\Documents and Settings\All Users\Application Data\{random}
%System Root%\Documents and Settings\All Users\Application Data\~{random}
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_FAKEAV.FKQ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
- Open a command prompt.
- For Windows 2000, Windows XP, and Windows Server 2003 users, click Start>Run. In the Open input box, type CMD then press Enter.
- In the CMD console, type the following:
ATTRIB [+R | -R] [+A | -A ] [+S | -S] [+H | -H] [+I | -I] [drive:][path][file name] [/S [/D] [/L]]
Where:
+ Sets an attribute.
- Clears an attribute
R Read-only file attribute
A Archive file attribute
S System file attribute
H Hidden file attribute
I Not content indexed file attribute
[drive:][path][filename]
Specifies a file or files for attrib to process
/S Processes matching files in the current folder and all subfolders.
/D Processes folders
/L Work on the attributes of the Symbolic Link versus the target of the Symbolic Link
Example:
To unhide all files and folders (including subfolders) in drive D:
ATTRIB –H D:\* /S /D
- Repeat Step 2 for folders and files in other drives or directories.
NOTES:
GENERAL RECOMMENDATION
1. This malware is detected and removed by the latest Trend Micro anti-malware engine and pattern. Always keep pattern files and engines up-to-date. To know more about updating your Trend Micro product’s pattern, please refer to the following Trend Micro support page: http://esupport.trendmicro.com/9/How-do-I-manually-update-the-virus-pattern-of-my-Trend-Micro-Internet.aspx
Note: The steps apply for specific products indicated in the page.
2. To actively detect and protect your machine, enable real-time scanning of your Trend Micro anti-malware product. Refer to the following Trend Micro support page to know more about enabling real-time scanning in your Trend Micro product:
Home Users: http://esupport.trendmicro.com/solution/en-us/1054798.aspx
Business Users: http://esupport.trendmicro.com/Pages/How-do-I-enable-or-disable-the-Real-time-Protection-of-Trend-M-EN-1038331.aspx
3. Enable firewall to protect against threats. http://esupport.trendmicro.com/3/How-do-I-enable-or-disable-the-Personal-Firewall-of-Trend-Micr-EN-1038273.aspx
4. Block unused ports to disallow malware from using these ports to communicate and/or enforce commands.
5. Be aware of social engineering attacks.
6. Avoid accessing the listed malicious URLs to prevent possible re-infection.
7. Monitor network connections for any suspicious connection or connectivity.
8. Regularly update list of sites that are trusted.
Did this description help? Tell us how we did.