This ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
It connects to certain websites to send and receive information.
Arrival Details
This ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Autostart Technique
This ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
DecryptFiles = C:\Users\{username}\AppData\Local\Temp\decrypt.exe
Dropping Routine
This ransomware drops the following files:
- C:\Users\{username}\AppData\Local\Temp\id.txt - 15 random characters
- C:\Users\{username}\AppData\Local\Temp\adr.txt - bitcoin address
- C:\Users\{username}\AppData\Local\Temp\lnk.txt - server
- C:\Users\{username}\AppData\Local\Temp\btc.txt - bitcoins to pay
- C:\Users\{username}\AppData\Local\Temp\del.bat - terminates and deletes decrypt.exe, and deletes the text files
Download Routine
This ransomware accesses the following websites to download files:
- http://{BLOCKED}.{BLOCKED}.123.78/decrypt.exe
It saves the files it downloads using the following names:
- C:\Users\{username}\AppData\Local\Temp\decrypt.exe - ransom note and decrypt program
It then executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
Other Details
This ransomware connects to the following website to send and receive information:
- http://{BLOCKED}.{BLOCKED}.123.78/
It encrypts files with the following extensions:
- .sql
- .csv
- .zip
- .mdbackup
- .syncdb
- .css
- .js
- .txt
- .pdf
- .doc
- .docx
- .exl
- .kdbx
- .kdb
It renames encrypted files using the following names:
- {original filename and extension}.grt
NOTES:
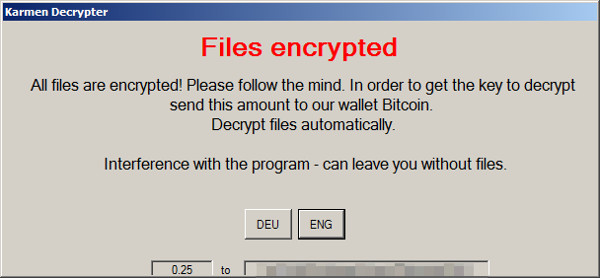
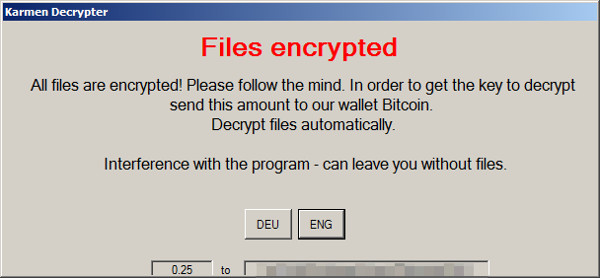
Decrypt.exe shows the following message:
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
[ Learn More ]
[ back ]
To restart in Safe Mode:
• For Windows 2000 users
- Restart your computer.
- Press F8 when you see the Starting Windows bar at the bottom of the screen.
- Choose the Safe Mode option from the Windows Advanced Options menu then press Enter.
• For Windows XP users
- Restart your computer.
- Press F8 after the Power-On Self Test (POST) routine is done. If the Windows Advanced Options menu does not appear, try restarting then pressing F8 several times when the POST screen appears.
- Choose the Safe Mode option from the Windows Advanced Options menu then press Enter.
• For Windows Server 2003 users
- Restart your computer.
- Press F8 after Windows starts up. If the Windows Advanced Options menu does not appear, try restarting again and pressing F8 several times afterward.
- On the Windows Advanced Option menu, use the arrow keys to select Safe Mode then press Enter.
• For Windows Vista, Windows 7, and Windows Server 2008 users
- Restart your computer.
- Press F8 after the Power-On Self Test (POST) routine is done. If the Advanced Boot Options menu does not appear, try restarting and then pressing F8 several times after the POST screen is displayed.
- On the Advanced Boot Options menu, use the arrow keys to select the Safe Mode option, and then press Enter.
• For Windows 8, Windows 8.1, and Windows Server 2012 users
- Access the Charms bar by moving your mouse pointer to the upper right corner of the screen.
- Move your mouse pointer down and click Settings>Change your PC Settings.
- In the left panel, click General.
- In the right panel, scroll down to the bottom to find the Advanced startup section, then click the Restart now button and wait for the system to restart.
- In the Advanced Startup menu, click Troubleshoot>Advanced Options>Startup Settings>Restart and wait for the system to restart.
- In the Startup Settings menu, press 4 to enable safe mode.
Step 4
Delete this registry value
[ Learn More ]
[ back ]
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- DecryptFiles = C:\Users\{username}\AppData\Local\Temp\decrypt.exe
To delete the registry value this malware created:
- Open Registry Editor. To do this:
» For Windows 2000, Windows XP, and Windows Server 2003 users, click Start>Run, type regedit in the text box provided, and then press Enter.
» For Windows Vista, Windows 7, and Windows Server 2008 users, click the Start button, type regedit in the Search input field then press Enter.
» For Windows 8, Windows 8.1, and Windows Server 2012 users, right-click on the lower left corner of the screen, click Run, type regedit in the text box provided, and then press Enter. - In the left panel of the Registry Editor window, double-click the following:
HKEY_CURRENT_USER>Software>Microsoft>Windows>CurrentVersion>Run - In the right panel, locate and delete the entry:
DecryptFiles = C:\Users\{username}\AppData\Local\Temp\decrypt.exe - Close Registry Editor.
Step 5
Search and delete this file
[ Learn More ]
[ back ]
There may be some files that are hidden. Please make sure you check the
Search Hidden Files and Folders checkbox in the "More advanced options" option to include all hidden files and folders in the search result.
- C:\Users\{username}\AppData\Local\Temp\id.txt
- C:\Users\{username}\AppData\Local\Temp\adr.txt
- C:\Users\{username}\AppData\Local\Temp\lnk.txt
- C:\Users\{username}\AppData\Local\Temp\btc.txt
- C:\Users\{username}\AppData\Local\Temp\del.bat
- C:\Users\{username}\AppData\Local\Temp\decrypt.exe
To manually delete a malware/grayware file from an affected system:
• For Windows 2000, Windows XP, and Windows Server 2003:
- Right-click Start then click Search....
- In the File name* input box, type the following:
- C:\Users\{username}\AppData\Local\Temp\id.txt
- C:\Users\{username}\AppData\Local\Temp\adr.txt
- C:\Users\{username}\AppData\Local\Temp\lnk.txt
- C:\Users\{username}\AppData\Local\Temp\btc.txt
- C:\Users\{username}\AppData\Local\Temp\del.bat
- C:\Users\{username}\AppData\Local\Temp\decrypt.exe
- In the Look In drop-down list, select My Computer then press Enter.
- Once located, select the file then press SHIFT+DELETE to delete it.
*Note: The file name input box title varies depending on the Windows version (e.g. Search for files or folders named or All or part of the file name.).
• For Windows Vista, Windows 7, Windows Server 2008, Windows 8, Windows 8.1, and Windows Server 2012:
- Open a Windows Explorer window.
- For Windows Vista, 7, and Server 2008 users, click Start>Computer.
- For Windows 8, 8.1, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- C:\Users\{username}\AppData\Local\Temp\id.txt
- C:\Users\{username}\AppData\Local\Temp\adr.txt
- C:\Users\{username}\AppData\Local\Temp\lnk.txt
- C:\Users\{username}\AppData\Local\Temp\btc.txt
- C:\Users\{username}\AppData\Local\Temp\del.bat
- C:\Users\{username}\AppData\Local\Temp\decrypt.exe
- Once located, select the file then press SHIFT+DELETE to delete it.
*Note: Read the following Microsoft page if these steps do not work on Windows 7.
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as RANSOM_HIDDENTEARKARMEN.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 7
Restore encrypted files from backup.