Ransom.Win32.MCRYPT.THABAOAH
Trojan-Ransom.MSIL.Agent.abl(Kaspersky); Trojan:Win32/Occamy.C(Microsoft); Ransom.Wannacry(Symantec)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
685,056 bytes
EXE
Yes
17 Jun 2019
Drops files,
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following processes:
- "cmd.exe" /C ping 127.0.0.1 -n 5& Del → executes this command if "%System%\drivers\dcrypt.sys" is not found in the system
- "%Public%\dcinst.exe" -install → will not execute properly since it is not a parameter by nature of the file
- "%Public%\dcinst.exe" -setup → installs "dcrypt.sys" as a service into the system
- "%Public%\dccon.exe" -install → will not execute properly since it is not a parameter by nature of the file
- "shutdown.exe" /r /f /t 03 → shuts down the system after attempting to install the driver, dcrypt.sys into the system
- "%Public%\dccon.exe" -enum → enumerates the following information from the system.
- Drive Letter
- Drive Name
- Size
- Bootable (Y/N)
- Bootloader
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %Public% is the folder that serves as a repository of files or folders common to all users, which is usually C:\Users\Public in Windows Vista, 7, and 8.)
Autostart Technique
This Ransomware registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\dcrypt\Instances\
dcrypt
Altitude = 87150
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\dcrypt\Instances\
dcrypt
Flags = 0
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\dcrypt\Instances
DefaultInstance = "dcrypt"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\dcrypt\config
Flags = "1408"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\dcrypt\config
Hotkeys = "\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\dcrypt\config
sysBuild = "846"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\myCryptoraphyService
DisplayName = "myCryptoraphyService"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\myCryptoraphyService
ImagePath = "{malware path and file name}.exe"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\myCryptoraphyService
Start = "SERVICE_AUTO_START"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\dcrypt
DisplayName = "DiskCryptor driver"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\dcrypt
ImagePath = "%System%\drivers\dcrypt.sys"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\dcrypt
Start = "SERVICE_BOOT_START"
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\dcrypt\Instances\
dcrypt
Altitude = "87150"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\dcrypt\Instances\
dcrypt
Flags = "0"
Dropping Routine
This Ransomware drops the following files:
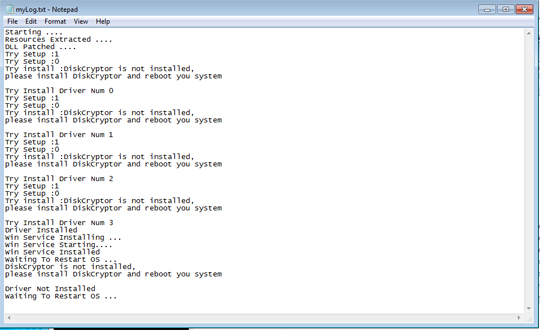
- %Public%\myLog.txt → contains the log of the malware process upon execution. A sample log is seen from the image:
- %Public%\dccon.exe → used to check information and perform other functions in a system's volume information
- %Public%\dcinst.exe → Contains the configuration and setup of the malware
- %Public%\dcrypt.sys
- %Public%\myConf.txt → contains the input argument/parameter that was set by the victim
- %System%\drivers\dcrypt.sys
- %Public%\dcapi.dll → contains all the calling functions that dcinst.exe and dccon.exe uses
Other Details
This Ransomware does the following:
- Dropped files accepts the following argument to perform different operations:
- dcinst.exe
- -setup → Drops and installs "dcrypt.sys" as a service into the infected system
- -unins → Checks and removes the installed "dcrypt.exe" service and driver into the infected system
- -unldr → restores the MBR to its default configuration
- -isboot → checks the MBR configuration
- -isenc → Checks the system if its encrypted
- Accepts the following parameters:
- test → stores "okay" into a standard output then terminates the process
- {Random string} → this malware needs an argument to perform its routine that will be stored into the dropped file "myConf.txt"
- After booting up your system, it will show the following ransom note:
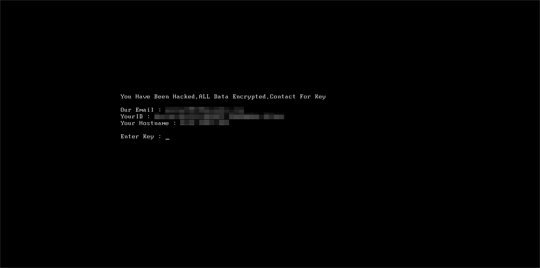
- This ransomware encrypts the whole disk of the victim that disables the infected system to boot up normally.
SOLUTION
9.850
14.680.04
10 Dec 2018
14.681.00
11 Dec 2018
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Restart in Safe Mode
Step 3
Identify and terminate files detected as Ransom.Win32.MCRYPT.THABAOAH
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Search and delete these files
- %Public%\myLog.txt
- %Public%\dccon.exe
- %Public%\dcinst.exe
- %Public%\dcrypt.sys
- %Public%\myConf.txt
- %System%\drivers\dcrypt.sys
- %Public%\dcapi.dll
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\dcryptStep 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.MCRYPT.THABAOAH. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 7
Restore encrypted files from backup.
Did this description help? Tell us how we did.

