Ransom.MSIL.HARDBIT.THAODBC
UDS:Trojan.MSIL.DelShad.gen (KASPERSKY) ; Ransom:Win32/Hardbit!MTB (MICROSOFT)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %User Profile%\DOCUMENTS\hrdb.ico → icon used for all encrypted files
- %Desktop%\HARDBIT.jpg → image used as system wallpaper after encryption
- %User Temp%\lsm.exe → detected as TROJ_GEN.R002H09HJ23
- %User Temp%\is64.txt → identifies the OS architecture
- %User Temp%\is64.bat
- %User Temp%\is64.fil → contains the path to the 64-bit cmd.exe
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name} on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %Desktop% is the current user's desktop, which is usually C:\Documents and Settings\{User Name}\Desktop on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\Desktop on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- cmd.exe /C sc delete VSS
- cmd.exe /C wbadmin delete catalog -quiet
- cmd.exe /C vssadmin delete shadows /all /quiet & wmic shadowcopy deletee
- cmd.exe /C bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no
- "powershell" Get-MpPreference -verbose
- net.exe stop avpsus /y
- net.exe stop McAfeeDLPAgentService /y
- net.exe stop mfewc /y
- net.exe stop BMR Boot Service /y
- net.exe stop NetBackup BMR MTFTP Service /y
- net.exe stop DefWatch /y
- net.exe stop ccEvtMgr /y
- net.exe stop ccSetMgr /y
- net.exe stop SavRoam /y
- net.exe stop RTVscan /y
- net.exe stop QBFCService /y
- net.exe stop QBIDPService /y
- net.exe stop IntuitQuickBooksFCS /y
- net.exe stop QBCFMonitorService /y
- net.exe stop YooBackup /y
- net.exe stop YooIT /y
- net.exe stop zhudongfangyu /y
- net.exe stop stc_raw_agent /y
- net.exe stop VSNAPVSS /y
- net.exe stop VeeamTransportSvc /y
- net.exe stop VeeamDeploymentService /y
- net.exe stop VeeamNFSSvc /y
- net.exe stop veeam /y
- net.exe stop PDVFSService /y
- net.exe stop BackupExecVSSProvider /y
- net.exe stop BackupExecAgentAccelerator /y
- net.exe stop BackupExecAgentBrowser /y
- net.exe stop BackupExecDiveciMediaService /y
- net.exe stop BackupExecJobEngine /y
- net.exe stop BackupExecManagementService /y
- net.exe stop BackupExecRPCService /y
- net.exe stop AcrSch2Svc /y
- net.exe stop AcronisAgent /y
- net.exe stop CASAD2DWebSvc /y
- net.exe stop CAARCUpdateSvc /y
- net.exe stop sophos /y
- net.exe stop -n apache24
- net.exe stop mysql57
- net.exe wrapper
- net.exe DefWatch
- net.exe stop SavRoam /y
- net.exe stop Sqlservr /y
- net.exe stop sqlagent /y
- net.exe stop sqladhlp /y
- net.exe stop Culserver /y
- net.exe stop sqlbrowser /y
- net.exe stop QLADHLP /y
- net.exe stop Intuit /y
- net.exe stop QuickBooks /y
- net.exe stop FCS /y
- net.exe stop msmdsrv /y
- net.exe stop tomcat6 /y
- net.exe stop vmware /y
- net.exe stop vmware-converter /y
- net.exe stop dbsrv12 /y
- net.exe stop dbeng8 /y
- net.exe stop MSSQL$MICROSOFT /y
- net.exe stop ##WID /y
- net.exe stop MSSQL$VEEAMSQL2012 /y
- net.exe stop SQLAgent$VEEAMSQL2012 /y
- net.exe stop SQLBrowser /y
- net.exe stop SQLWriter /y
- net.exe stop FishbowlMySQL /y
- net.exe stop MySQL57 /y
- net.exe stop MSSQL$KAV_CS_ADMIN_KIT /y
- net.exe stop MSSQLServerADHelper100 /y!
- net.exe stop SQLAgent$KAV_CS_ADMIN_KIT /y
- net.exe stop msftesql /y
- net.exe stop Exchange /y
- net.exe stop MSSQL$MICROSOFT##SSEE /y
- net.exe stop MSSQL$SBSMONITORING /y
- net.exe stop MSSQL$SHAREPOINT /y
- net.exe stop MSSQLFDLauncher$SBSMONITORING /y
- net.exe stop SQLAgent$SBSMONITORING /y
- net.exe stop SQLAgent$SHAREPOINT /y
- net.exe stop QBVSS /y
- net.exe stop vss /y
- net.exe stop sql /y
- net.exe stop svc$ /y
- net.exe stop MSSQL /y
- net.exe stop MSSQL$ /y
- net.exe stop memtas /y
- net.exe stop mepocs /y
- net.exe stop backup /y
- net.exe stop bedbg /y
- net.exe stop MVArmor /y
- net.exe stop MVarmor64 /y
- net.exe stop ARSM /y
- net.exe stop WSBExchange /y
- net.exe stop MSExchange /y
- net.exe stop MSExchange$ /y
- %User Temp%\lsm.exe
- %User Temp%\is64.bat
- "%System%\mshta.exe" "%User Temp%\readme-warning.hta"
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
It creates the following folders:
- %User Temp%\myfiles
- %User Temp%\wxy
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_USERS\{SID}_CLASSES\.hardbit2\
DefaultIcon
(Default) = %User Profile%\Documents\hrdb.ico
It adds the following registry keys as part of its installation routine:
HKEY_USERS\{SID}_CLASSES\.hardbit2
HKEY_USERS\{SID}_CLASSES\.hardbit2\
DefaultIcon
It modifies the following registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender
DisableAntiSpyware = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableBehaviorMonitoring = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableOnAccessProtection = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableScanOnRealtimeEnable = 1
(Note: The default value data of the said registry entry is 0.)
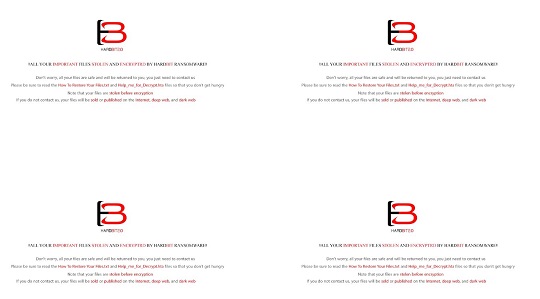
It changes the desktop wallpaper by modifying the following registry entries:
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %Desktop%\HARDBIT.jpg
It sets the system's desktop wallpaper to the following image:
- %Desktop%\HARDBIT.jpg
Process Termination
This Ransomware terminates the following services if found on the affected system:
- avpsus
- McAfeeDLPAgentService
- mfewc
- BMR Boot Service
- NetBackup BMR MTFTP Service
- DefWatch
- ccEvtMgr
- ccSetMgr
- SavRoam
- RTVscan
- QBFCService
- QBIDPService
- IntuitQuickBooksFCS
- QBCFMonitorService
- YooBackup
- YooIT
- zhudongfangyu
- stc_raw_agent
- VSNAPVSS
- VeeamTransportSvc
- VeeamDeploymentService
- VeeamNFSSvc
- veeam
- PDVFSService
- BackupExecVSSProvider
- BackupExecAgentAccelerator
- BackupExecAgentBrowser
- BackupExecDiveciMediaService
- BackupExecJobEngine
- BackupExecManagementService
- BackupExecRPCService
- AcrSch2Svc
- AcronisAgent
- CASAD2DWebSvc
- CAARCUpdateSvc
- sophos
- apache24
- mysql57
- SavRoam
- Sqlservr
- sqlagent
- sqladhlp
- Culserver
- sqlbrowser
- QLADHLP
- Intuit
- QuickBooks
- FCS
- msmdsrv
- tomcat6
- vmware
- vmware-converter
- dbsrv12
- dbeng8
- MSSQL$MICROSOFT
- ##WID
- MSSQL$VEEAMSQL2012
- SQLAgent$VEEAMSQL2012
- SQLBrowser
- SQLWriter
- FishbowlMySQL
- MySQL57
- MSSQL$KAV_CS_ADMIN_KIT
- MSSQLServerADHelper100!
- SQLAgent$KAV_CS_ADMIN_KIT
- msftesql
- Exchange
- MSSQL$MICROSOFT##SSEE
- MSSQL$SBSMONITORING
- MSSQL$SHAREPOINT
- MSSQLFDLauncher$SBSMONITORING
- SQLAgent$SBSMONITORING
- SQLAgent$SHAREPOINT
- QBVSS
- vss
- sql
- svc$
- MSSQL
- MSSQL$
- memtas
- mepocs
- backup
- bedbg
- MVArmor
- MVarmor64
- ARSM
- WSBExchange
- MSExchange
- MSExchange$
It terminates the following processes if found running in the affected system's memory:
- 360Doctor
- 360Se
- acwebbrowser
- ADExplorer
- ADExplorer64
- ADExplorer64a
- Adobe
- AdobeCollabSync
- AdobeIPCBroker
- agntsvc
- AutodeskDesktopApp
- Autoruns
- Autoruns64
- Autoruns64a
- Autorunsc
- Autorunsc64
- Autorunsc64a
- avz
- axlbridge
- bedbh
- benetns
- bengien
- beserver
- BrCcUxSys
- BrCtrlCntr
- CagService
- calc
- CEF
- Cloud
- CoreSync
- Creative
- Culture
- dbeng50
- dbsnmp
- Defwatch
- DellSystemDetect
- dumpcap
- encsvc
- EnterpriseClient
- excel
- fbguard
- fbserver
- fdhost
- fdlauncher
- firefox
- GDscan
- GlassWire
- GWCtlSrv
- Helper
- httpd
- infopath
- InputPersonalization
- isqlplussvc
- j0gnjko1
- java
- koaly-exp-engine-service
- msaccess
- mspub
- mydesktopqos
- mydesktopservice
- mysqld
- node
- notepad
- notepad++
- ocautoupds
- ocomm
- ocssd
- onedrive
- onenote
- ONENOTEM
- oracle
- outlook
- powerpnt
- ProcessHacker
- Procexp
- Procexp64
- procexp64a
- procmon
- procmon64
- procmon64a
- pvlsvr
- QBDBMgr
- QBDBMgrN
- QBIDPService
- qbupdate
- QBW32
- Raccine
- Raccine_x86
- RaccineElevatedCfg
- RaccineSettings
- RAgui
- raw_agent_svc
- RdrCEF
- RTVscan
- sam
- Service
- SimplyConnectionManager
- SimplySystemTrayIcon
- sqbcoreservice
- sqlbrowser
- sqlmangr
- Sqlservr
- Ssms
- steam
- supervise
- sync
- synctime
- Sysmon
- Sysmon64
- SystemExplorer
- SystemExplorerService
- SystemExplorerService64
- taskbar
- tbirdconfig
- tcpview
- tcpview64
- tcpview64a
- tdsskiller
- TeamViewer
- TeamViewer_Service
- thebat
- thunderbird
- TitanV
- tomcat6
- Totalcmd
- Totalcmd64
- tv_w32
- tv_x64
- VeeamDeploymentSvc
- visio
- vsnapvss
- vss
- vxmon
- wdswfsafe
- winword
- WireShark
- wordpad
- worker
- wsa_service
- wuauclt
- wxServer
- wxServerView
- xfssvccon
- ZhuDongFangYu
Information Theft
This Ransomware gathers the following data:
- Hardware information (CPU, Disk Drives, Graphics Card, Manufacturer, BIOS)
- Network adapter settings (IP configuration, MAC address)
- Username
- Computer Name
- Timezone Information
Other Details
This Ransomware does the following:
- It changes the encrypted file icon to the following image:

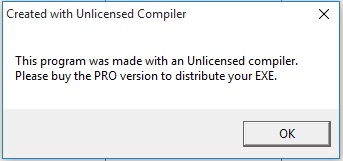
- %User Temp%\lsm.exe shows the following message box:
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file path:
- autorun.inf
- boot.ini
- bootfont.bin
- bootsect.bak
- d3d9caps.dat
- desktop.ini
- GDIPFONTCACHEV1.DAT
- HARDBIT.jpg
- iconcache.db
- log
- ntldr
- ntuser.dat
- ntuser.ini
- thumbs.db
It renames encrypted files using the following names:
- {10 Random Characters}.[id-{Generated ID}].[godgood55@tutanota.com].hardbit2
It drops the following file(s) as ransom note:
- {Encrypted Directory}\How To Restore Your Files.txt
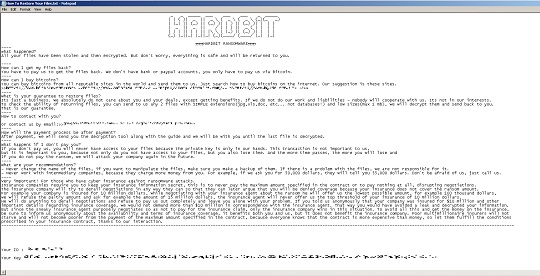
- {Encrypted Directory}\Help_me_for_Decrypt.hta
%User Temp%\readme-warning.hta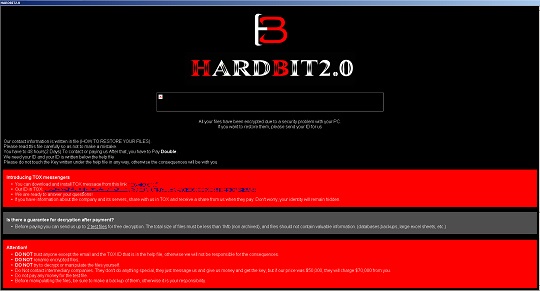
It avoids encrypting files with the following file extensions:
- .dll
- .exe
- .EXE
- .lnk
- .DLL
- .msi
- .386
- .adv
- .ani
- .bin
- .cab
- .cmd
- .com
- .cpl
- .cur
- .deskthemepack
- .diagcab
- .diagcfg
- .diagpkg
- .drv
- .hlp
- .hta
- .icl
- .icns
- .ico
- .ics
- .idx
- .key
- .lock
- .mod
- .mpa
- .msc
- .msp
- .msstyles
- .msu
- .nls
- .nomedia
- .ocx
- .pdb
- .prf
- .ps1
- .rom
- .rtp
- .scr
- .search-ms
- .shs
- .spl
- .sys
- .theme
- .themepack
- .wpx
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
-
TROJ.Win32.TRX.XXPE50FFF065
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender
- DisableAntiSpyware=1
- DisableAntiSpyware=0
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection
- DisableBehaviorMonitoring=1
- DisableBehaviorMonitoring= 0
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection
- DisableOnAccessProtection=1
- DisableOnAccessProtection= 0
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection
- DisableScanOnRealtimeEnable=1
- DisableScanOnRealtimeEnable= 0
Step 5
Delete this registry key
=Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this only if you know how to or you can seek your system administrator’s help. You may also check out this Microsoft article first before modifying your computer's registry.
- In HKEY_USERS\{SID}_CLASSES\.hardbit2
Step 6
Search and delete this file
- {Encrypted Directory}\How To Restore Your Files.txt
- {Encrypted Directory}\Help_me_for_Decrypt.hta
- %User Temp%\readme-warning.hta
- %User Profile%\DOCUMENTS\hrdb.ico
- %User Temp%\lsm.exe
- %User Temp%\is64.txt
- %User Temp%\is64.bat
- %User Temp%\is64.fil
- %Desktop%\HARDBIT.jpg
Step 7
Search and delete these folders
- %User Temp%\myfiles
- %User Temp%\wxy
Step 8
Scan your computer with your Trend Micro product to delete files detected as Ransom.MSIL.HARDBIT.THAODBC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 9
Reset your Desktop properties
Step 10
Restore encrypted files from backup.
Did this description help? Tell us how we did.


