Proxyware.Win32.MaskVPN.C
Application.Deceptor.MaskVPN.A (BITDEFENDER)
Windows


Threat Type: Proxyware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Proxyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Proxyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Proxyware adds the following folders:
- %User Temp%\{Random Characters} → Deletes afterwards
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops the following files:
- %User Temp%\{Random Characters}\SET1E98.tmp → Deletes afterwards
- %User Temp%\{Random Characters}\SET22B.tmp → Deletes afterwards
- %User Temp%\{Random Characters}\SET2E9.tmp → Deletes afterwards
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- cmd /c ""{Malware Path}\driver\win732\uninstall.bat" "
- tapinstall.exe remove tap0901
- cmd /c ""{Malware Path}\driver\win732\install.bat" "
- tapinstall.exe install OemVista.inf tap0901
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- D041937956BB451DBAD9F6FC0226C1D4
Other System Modifications
This Proxyware deletes the following files:
- %User Temp%\{Random Characters}\oemvista.inf
- %User Temp%\{Random Characters}\tap0901.cat
- %User Temp%\{Random Characters}\tap0901.sys
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\Setup\
SetupapiLogStatus
setupapi.dev.log = 4096
Adware Routine
This Proxyware adds and runs the following services:
- tap0901 → (TAP-Windows Adapter V9)
Other Details
This Proxyware adds the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\tap0901
It does the following:
- It gathers the following system info as part of its initialization:
- OS Version
- Service Pack
- Suite
- ProductType
- Architecture
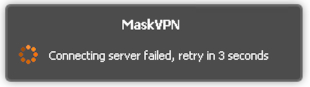
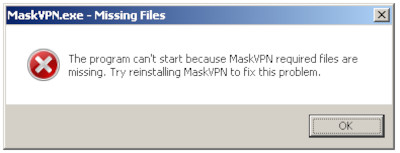
- It requires the existence of the following file in order to be executed:
- config.db Or else it displays the following error message:
- It displays the following upon execution:
- It detects possible old version of VPN driver installed on the system.

- It installs specific VPN driver included to its installer package.


- It checks for possible updates into a server.
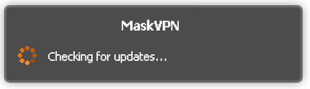
- However it encounters an error receiving update.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Identify and terminate files detected as Proxyware.Win32.MaskVPN.C
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 5
Disable this malware service
- tap0901
Step 6
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus
- setupapi.dev.log = 4096
- setupapi.dev.log = 4096
Step 7
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\tap0901
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Proxyware.Win32.MaskVPN.C. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


