TROJ_POSHCODER.A
Trojan-Ransom.Win32.Crypren.pug (Kaspersky)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This ransomware uses Windows PowerShell to encrypt files.
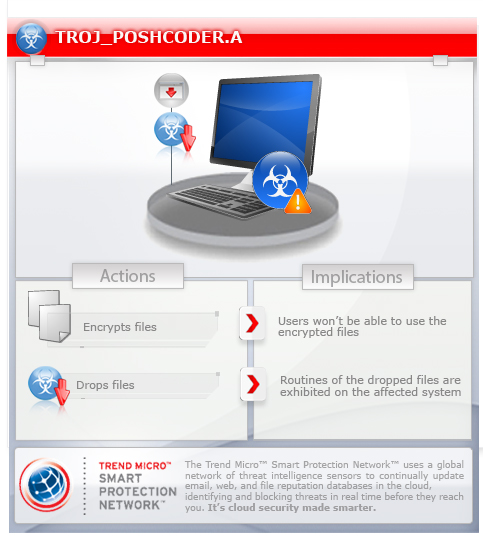
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Varies
EXE, DLL, Script
Yes
20 May 2014
Encrypts files, Displays images, Drops files
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan creates the following folders:
- %User Temp%\Quest Software\PowerGUI\{GUID}
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
Other System Modifications
This Trojan adds the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{GUID} = ""
HKEY_CURRENT_USER\Software\Microsoft
{GUID}0 = ""
HKEY_CURRENT_USER\Software\Microsoft
{GUID}1 = ""
Dropping Routine
This Trojan drops the following files:
- %User Temp%\Quest Software\PowerGUI\{GUID}\crypter.ps1 - the PowerShell encryptor script component also detected as TROJ_POSHCODER.A
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
Other Details
This Trojan encrypts files with the following extensions:
- .1cd
- .3d
- .3d4
- .3df8
- .3g2
- .3gp
- .3gp2
- .3mm
- .7z
- .8ba
- .8bc
- .8be
- .8bf
- .8bi8
- .8bl
- .8bs
- .8bx
- .8by
- .8li
- .aac
- .abk
- .abw
- .ac3
- .accdb
- .ace
- .act
- .ade
- .adi
- .adpb
- .adr
- .adt
- .aim
- .aip
- .ais
- .amf
- .amr
- .amu
- .amx
- .amxx
- .ans
- .ap
- .ape
- .api
- .arc
- .ari
- .arj
- .aro
- .arr
- .asa
- .asc
- .ascx
- .ase
- .ashx
- .asmx
- .asp
- .asr
- .avi
- .avs
- .bdp
- .bdr
- .bi8
- .bib
- .bic
- .big
- .bik
- .bkf
- .blp
- .bmc
- .bmf
- .bml
- .bmp
- .boc
- .bp2
- .bp3
- .bpl
- .bsp
- .cag
- .cam
- .cap
- .car
- .cbr
- .cbz
- .cc
- .ccd
- .cch
- .cd
- .cdr
- .cer
- .cfg
- .cgf
- .chk
- .clr
- .cms
- .cod
- .col
- .cp
- .cpp
- .crd
- .crt
- .cs
- .csi
- .cso
- .css
- .ctt
- .cty
- .cwf
- .dal
- .dap
- .dbb
- .dbx
- .dcp
- .dcu
- .ddc
- .ddcx
- .dem
- .dev
- .dex
- .dic
- .dif
- .dii
- .dir
- .disk
- .divx
- .diz
- .djvu
- .dmg
- .dng
- .dob
- .doc
- .docm
- .docx
- .dot
- .dotm
- .dotx
- .dox
- .dpk
- .dpl
- .dpr
- .dsk
- .dsp
- .dvd
- .dvi
- .dvx
- .dwg
- .dxe
- .dxf
- .elf
- .eps
- .eql
- .err
- .euc
- .evo
- .ex
- .f90
- .faq
- .fcd
- .fdr
- .fds
- .ff
- .fla
- .flp
- .flv
- .for
- .fpp
- .gthr
- .gz
- .java
- .jc
- .jgz
- .jif
- .man
- .map
- .max
- .mbox
- .mbx
- .mcd
- .md0
- .md1
- .md2
- .md3
- .mdf
- .mdl
- .mdn
- .mds
- .mic
- .mip
- .mlx
- .mm6
- .mm7
- .mm8
- .mod
- .moz
- .mp1
- .mp3
- .mp4
- .mpa
- .msg
- .msp
- .mxp
- .nav
- .ncd
- .nds
- .nfo
- .now
- .nrg
- .nri
- .odc
- .odf
- .odi
- .odm
- .odp
- .ods
- .oft
- .oga
- .ogg
- .opf
- .owl
- .oxt
- .pab
- .pak
- .pbf
- .pbp
- .pbs
- .pcv
- .pdd
- .php
- .pkb
- .pkh
- .pl
- .plc
- .pli
- .pm
- .png
- .pot
- .potm
- .potx
- .ppd
- .ppf
- .pps
- .ppsm
- .ppsx
- .ppt
- .pptm
- .pptx
- .prc
- .prt
- .psa
- .psd
- .puz
- .pwf
- .pwi
- .pxp
- .qbb
- .qdf
- .qel
- .qif
- .qpx
- .qtiq
- .qtq
- .qtr
- .r00
- .r01
- .r02
- .r03
- .ra
- .rar
- .raw
- .res
- .rev
- .rgn
- .rnc
- .rng
- .rrt
- .rsrc
- .rsw
- .rte
- .rtf
- .rts
- .rtx
- .rum
- .run
- .rv
- .sad
- .saf
- .sav
- .scm
- .scn
- .scx
- .sdb
- .sdc
- .sdn
- .sds
- .sdt
- .sen
- .sfs
- .sfx
- .sh
- .shar
- .shr
- .shw
- .slt
- .snp
- .so
- .spr
- .sql
- .sqx
- .srf
- .srt
- .ssa
- .std
- .stt
- .stx
- .sud
- .svi
- .svr
- .swd
- .swf
- .t01
- .t03
- .t05
- .tar
- .tax2012
- .tax2013
- .tax2014
- .tbz2
- .tch
- .tcx
- .text
- .tg
- .thmx
- .tif
- .tiff
- .tlz
- .tpu
- .tpx
- .trp
- .tu
- .tur
- .txd
- .txf
- .txt
- .uax
- .udf
- .umx
- .unr
- .unx
- .uop
- .upoi
- .url
- .usa
- .usx
- .ut2
- .ut3
- .utc
- .utx
- .uvx
- .uxx
- .val
- .vc
- .vcd
- .vdo
- .ver
- .vhd
- .vmf
- .vmt
- .vsi
- .vtf
- .w3g
- .w3x
- .wad
- .war
- .wav
- .wave
- .waw
- .wbk
- .wdgt
- .wks
- .wm
- .wma
- .wmd
- .wmdb
- .wmmp
- .wmv
- .wmx
- .wow
- .wpk
- .wpl
- .wsh
- .wtd
- .wtf
- .wvx
- .xl
- .xla
- .xlam
- .xlc
- .xll
- .xlm
- .xlr
- .xls
- .xlsb
- .xlsm
- .xlsx
- .xltx
- .xlv
- .xlwx
- .xpi
- .xpt
- .xvid
- .xwd
- .yab
- .yps
- .z02
- .z04
- .zap
- .zip
- .zipx
- .zoo
- .gam
- .gif
- .grf
- .gzig
- .h3m
- .h4r
- .htm
- .idx
- .img
- .indd
- .ink
- .ipa
- .iso
- .isu
- .isz
- .itdb
- .itl
- .iwd
- .jar
- .jav
- .jiff
- .jpc
- .jpeg
- .jpf
- .jpg
- .jpw
- .js
- .kmz
- .kwd
- .lbi
- .lcd
- .lcf
- .ldb
- .lgp
- .lp2
- .ltm
- .ltr
- .lvl
- .mag
It renames encrypted files using the following names:
- {file name}.POSHCODER
NOTES:
It encrypts the first 81,920 bytes of the file if the file size of the file to be encrypted is greater than 81,920 bytes. If the file size is less, it encrypts the whole file.
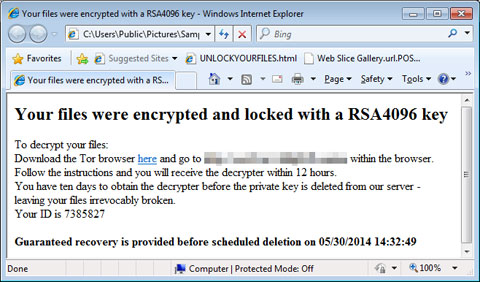
It drops a file named UNLOCKYOURFILES.html in all folders where there are encrypted files. When opened using a browser, it contains the following:
It displays the following message box:
SOLUTION
9.700
10.804.07
20 May 2014
10.805.00
20 May 2014
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft
- {GUID}0 = ""
- {GUID}0 = ""
- In HKEY_CURRENT_USER\Software\Microsoft
- {GUID}1 = ""
- {GUID}1 = ""
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {GUID} = ""
- {GUID} = ""
Step 3
Search and delete this folder
- %User Temp%\Quest Software\PowerGUI\{GUID}
Step 4
Scan your computer with your Trend Micro product to delete files detected as TROJ_POSHCODER.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

