RANSOM_GRYPHON.AUSG
Ransom.BTCware (NORTON); Ransom:Win32/Betisrypt!rfn (Microsoft); Gen:Variant.Ransom.BTCWare.34 (BITDEFENDER)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following mutexes to ensure that only one of its copies runs at any one time:
- NUCLEAR
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- .nuclear
- nuclear
It avoids encrypting files with the following strings in their file path:
- $recycle.bin
- msocache
- ProgramData
- programdata
- programdata\
- windows
- nvidia
- intel
- appdata
- inetpub
- temp
- program files
- programfiles (x86)
- HELP.hta
- BOOTMGR
It appends the following extension to the file name of the encrypted files:
- [qeteway@{BLOCKED}ta.com].nuclear
It drops the following file(s) as ransom note:
- %Application Data%\HELP.hta
(Note: %Application Data% is the Application Data folder, where it usually is C:\Documents and Settings\{user name}\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Roaming on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
NOTES:
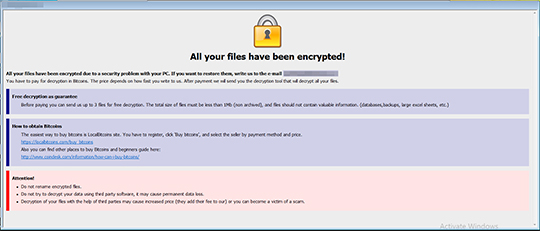
When %Application Data%\HELP.hta is opened, the following window will be shown:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Scan your computer with your Trend Micro product to delete files detected as RANSOM_GRYPHON.AUSG. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 4
Search and delete these files
- %Application Data%\HELP.hta
Step 5
Restore encrypted files from backup.
Did this description help? Tell us how we did.


