HTML_PHISH.AUSEHC
HTML/Phishing.PayPal.CS (ESET-NOD32); PWS:HTML/Phish (Microsoft)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
NOTES:
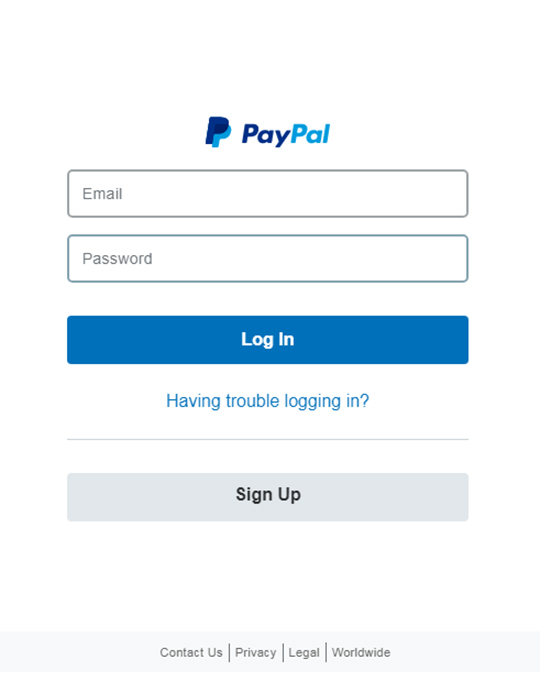
Upon execution of the file, it displays the following fake PayPal Login page.
After entering login credentials, the user will be presented with the following fake "Update Forms" requiring personal and credit card information.
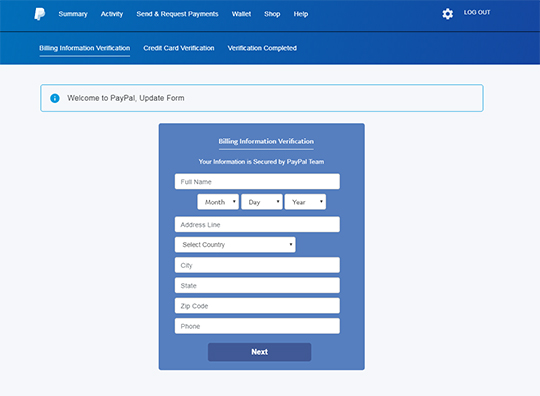
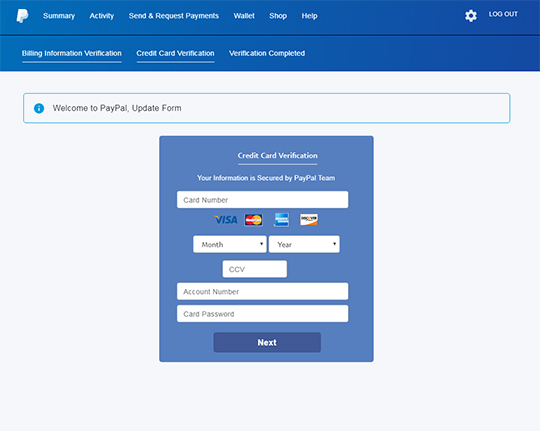
After providing the requested information and clicking Next, it will post the gathered information to the following URL: http://www.{BLOCKED}t.com.au/private/rez1.php
The user will then be redirected to the real PayPal homepage.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as HTML_PHISH.AUSEHC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



