Ransom.Linux.BRAINCIPHER.THHOIBD
Ransom:Linux/Babuk.B!MTB (MICROSOFT)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It encrypts files with specific file extensions. It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- If parameter -onvm {ID1, ID2, ID3, ...} is used:
- /tmp/running_vms.txt → contains active VM IDs retrieved from the system.
It adds the following processes:
- If parameter -onvm {ID1, ID2, ID3, ...} is used:
- vim-cmd vmsvc/getallvms | grep '^[0-9]' | awk '{print $1}' > /tmp/running_vms.txt → retrieves information about all VMs on an ESXi host and stores the IDs in a text file.
- vim-cmd vmsvc/power.getstate {VM ID} | grep 'Powered on' → checks the power state of VMs on an ESXi host based on the VM IDs specified in the parameter.
- vim-cmd vmsvc/power.off {VM ID} → powers off VMs on an ESXi host if found running.
- rm /tmp/running_vms.txt → permanently deletes the text file.
Other Details
This Ransomware does the following:
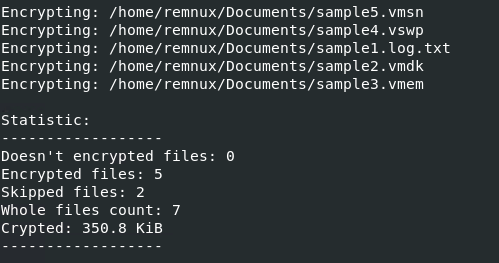
- It displays the following output in the terminal:
It accepts the following parameters:
- -onvm {ID1, ID2, ID3, ...} → used to power off ESXi VMs based on IDs
- -time {seconds} → delay in seconds before doing encryption
- {Path to Encrypt} → directory to encrypt including subdirectories
Ransomware Routine
This Ransomware encrypts files with the following extensions:
- .log
- .vmdk
- .vmem
- .vswp
- .vmsn
- Any files with the above strings found in their filename except with the blacklisted extensions.
It appends the following extension to the file name of the encrypted files:
- .encrptd
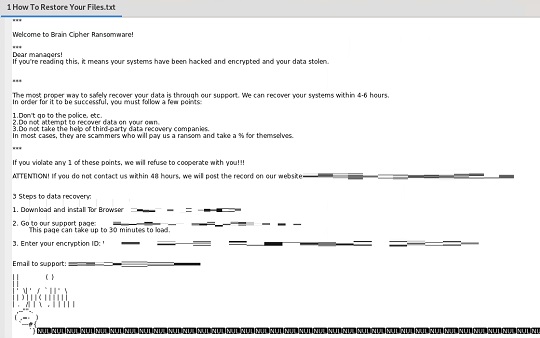
It drops the following file(s) as ransom note:
- {Encrypted Path}/How To Restore Your Files.txt
It avoids encrypting files with the following file extensions:
- .encrptd
- .encrptd{Any String}
SOLUTION
Step 1
Scan your computer with your Trend Micro product to delete files detected as Ransom.Linux.BRAINCIPHER.THHOIBD. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 2
Restore encrypted files from backup.
Did this description help? Tell us how we did.


