Backdoor.ASP.WEBSHELL.KEPL
Windows, Linux, MacOS


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be hosted on a website and run when a user accesses the said website.
It executes commands from a remote malicious user, effectively compromising the affected system.
TECHNICAL DETAILS
Arrival Details
This Backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be hosted on a website and run when a user accesses the said website.
Backdoor Routine
This Backdoor executes the following commands from a remote malicious user:
- Lists directories and files (includes file information)
- Adds and removes mapped drives
- Creates files and folders
- Renames files and folders
- Copies, moves, and deletes files
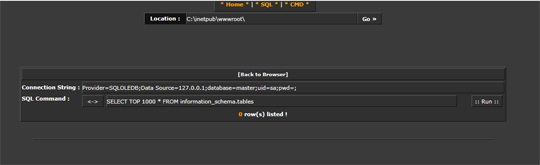
- Runs SQL command
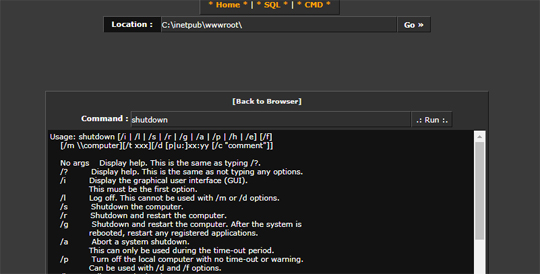
- Executes arbitrary commands via CMD
- Uploads and downloads files
- Remotely views image files (JPEG, GIF, BMP, PNG)
Other Details
This Backdoor does the following:
- When hosted on a web server, it is able to display the following windows, where the attacker can perform the backdoor activity:
- Directory Explorer
- SQL Window
- CMD Window

It does not exploit any vulnerability.
It requires being hosted on a web server in order to proceed with its intended routine.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as Backdoor.ASP.WEBSHELL.KEPL. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.

