Another Cybersecurity Awareness Month is here. According to the National Cybersecurity Alliance (NCA) this is the twentieth year we’ve marked the event. 20 years ago, we saw the launch of Facebook, Gmail, MySpace, Roblox, Google’s IPO, and the MyDoom virus. Fast forward to 2023, with attacks and vulnerabilities now on the front pages daily, cybersecurity is more critical and difficult than ever.
What is Cybersecurity Awareness Month?
Launched in 2004 under leadership from the U.S. Department of Homeland Security and the NCA, Cybersecurity Awareness Month aims to help Americans stay safe and secure online. Since then, the movement has grown exponentially—raising awareness amongst consumers, small and medium sized businesses (SMB), enterprises, and educational institutions.
Making Cybersecurity Awareness Month Meaningful
This year, NIST lists the focus is on four key behaviors throughout the month:
- Enabling multi-factor authentication
- Using strong passwords and a password manager
- Updating software
- Recognizing and reporting phishing
This is certainly a great place to start, but businesses of all sizes should look to go above and beyond in a strategic sense to improve their cybersecurity posture. Here are my four additional actions that any organization can take to show high-impact improvement:
Visibility, Visibility, Visibility
There’s a military expression that “Amateurs talk tactics, and veterans talk logistics”: veteran cybersecurity staff today are talking about visibility. With more complexity in our environments, attackers like the complexity when it means neglected and less protected resources they can use to hop-scotching laterally to gain privilege and avoid detection.
Relying on your IT system management databases isn’t accurate enough today: the scope and speed of change means that ITSM databases are perpetually out of date and lean on security to help them find new or hidden assets.
Know your network’s stuff: whether legitimate, shadow IT, or connected through VPNs, get a more accurate inventory of your attack surface. Attackers know that devices not managed and/or patched are the very best lateral paths.
Visibility doesn’t mean just knowing the attack surface alone. External attack surface management (EASM) and internal Cyber Asset Attack Surface Management (CAASM) are both needed to get a large part of the asset picture.
But visibility goes beyond the existence or patch state of an asset. It means knowing what communication has happened with those assets – merely knowing an asset is vulnerable is less meaningful than also knowing what other identities and assets it communicates with as this reflects on the posture of those other elements.
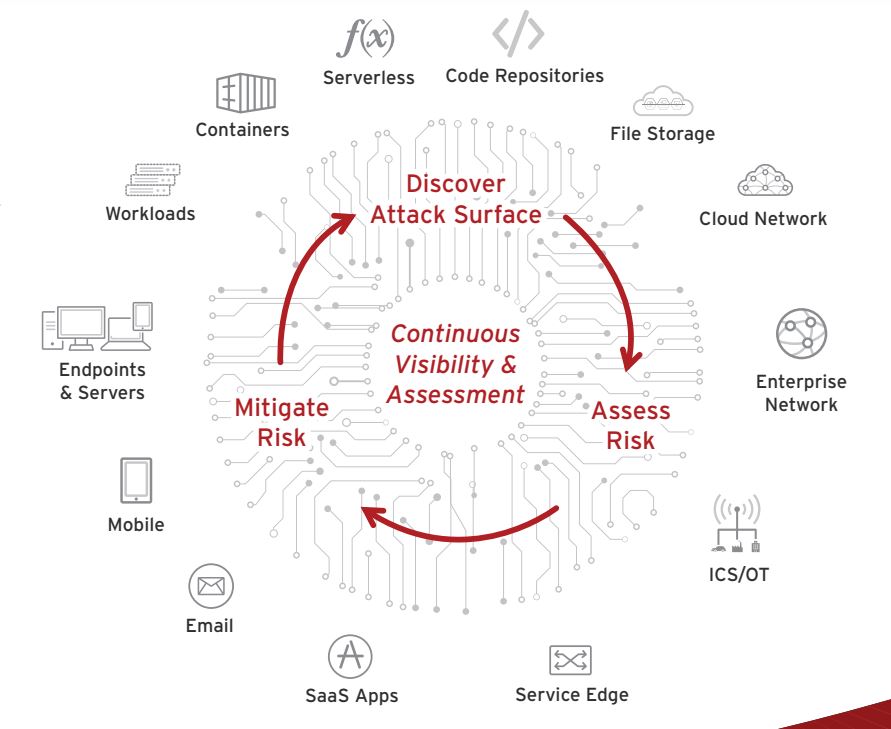
Decrease the Risk Assessment Time Gap Towards Continuous Assessment
Semi-annual penetration tests get a box checked and keep you out of compliance jail, but cybersecurity has moved to near-real time and so too must your assessment. Continuous monitoring has been an important goal, but we need to advance it to making continuous decisions based on that continuous monitoring.
Even events such as authenticating to use a VPN are too infrequent to make actionable judgements: in between those authentications there can be many indicators of compromise (IOC) that give a high enough assurance that you or your account/device/asset/data has moved from acceptable to unacceptable risk.
Continuous assessment means always looking for vulnerable or compromised elements and taking action. If my device is vulnerable, or my email account is spewing malware or the signs of having been phished there should be an immediate risk-based decision taken. Time is the friend of the attacker. Let’s be less friendly with them.
Increase Collection of Non-Standard Security Telemetry
This action is closely tied to the first recommendation about visibility. The standard events we examine in security have not only gotten a bit stale, but the attackers know them well enough to avoid being caught up in them. That’s the whole basis for attacks to move laterally and through unconventional paths such as IoT and things likely not known to be part of your attack surface when they are. And like “birds of a feather”, the more of an outlier the telemetry comes from, the more likely it is to lead you to other assets, data, connections, and identities that your organization may not have known about.
Attackers know where the “motion alarms” are for standard security alerts and telemetry and avoid those. Common incident forensics clearly show that evading detection especially for known security safeguards is an increasingly common attacker tactic. A key part of visibility means going and gathering more new kinds of security-relevant telemetry.
A common mistake today is collecting more telemetry but accessing it less often. “Well, if we double the telemetry, we’ll just consult it half as often” doesn’t have to be the trade-off. Smart use of telemetry is utilized by modern platforms rather than clumsy bulk-searching through data, and more telemetry should mean less load on SOC staff, not more.
Extended detection and response (XDR) and continuous assessment gets smarter, faster, and more accurate when there is more data to assess beyond your parents’ firewall alerts. Telemetry regarding connections, rates of missed authentications, changes in application activity, DNS usage, system tools running in new places, never seen before pairings of privileges and the granting admin, unusual backups… there’s a data lake to fill with these. The more telemetry you have, means you can combine them into more meaningful indicators that are less likely to be a false positive or false negative.
Get Your Platform Strategy Underway, and Get Rid of Shelfware
Underscoring all of this is the fact you need the right security tools in place. While you may opt to diversify your security stack, don’t fall into the trap of deploying point products that don’t play nicely together. As I said, visibility is the foundation of all other defense – using siloed solutions will only give you bits and pieces of the entire picture.
A platform strategy is a strategy, not an overnight procurement exercise: you don’t need to rip and replace your entire stack immediately. Take a planned approach (but don’t delay the inevitable). However, you can leverage a cybersecurity platform that brings together the telemetry from different security solutions into a single pane of glass. Beware, some vendors may try to sell you a suite of siloed solutions as a platform. A true platform is composed of integrated vendor solutions and allows broad third-party integrations.
As a bonus, look for a platform that’s backed by the capabilities I mentioned earlier like XDR, virtual patching, automation, continuous monitoring and risk assessments, and more to provide security across the attack surface – from users, to endpoints, to email, to clouds, to networks, etc.
A key part of your platform strategy should be looking for security shelfware. As part of unifying the telemetry and response capabilities of your security tools, look for tools and products that aren’t necessary any longer.
It can be awkward to end-of-life a security tool that was viewed as critically useful a few years back and oh yes you made an eloquent pitch for the budget for it, but security moves quickly. You can integrate it into your platform, but instead if it really has been superseded or no longer relevant removing shelfware has only benefits.
Saving money, removing it from the need to integrate it into your platform, speedier analysis by removing duplicative telemetry, and the training and updating efforts are only part of the list of benefits of a leaner/cleaned-up security stack.
Next Steps
So, let’s make Cybersecurity Awareness Month actionable and meaningful. And in the spirit of visibility and continuous assessment don’t wait until next year’s Cybersecurity Awareness Month to check and refine your progress

