LabHost takedown
On Thursday, April 18, 2024, the UK’s Metropolitan Police Service, along with fellow UK and international law enforcement, as well as several trusted private industry partners, conducted an operation that succeeded in taking down the Phishing-as-a-Service (PhaaS) provider LabHost. This move was also timed to coincide with a number of key arrests related to this operation. In this entry, we will briefly explain what LabHost was, how it affected its victims, and the impact of this law enforcement operation — including the assistance provided by Trend Micro.
What is LabHost?
In late 2021, LabHost (AKA LabRat) emerged as a new PhaaS platform, growing over time to eventually offer dozens of phishing pages targeting banks, high-profile organizations, and other service providers located around the world, but most notably in Canada, the US, and the UK. The popularity of the platform meant that at the time of the takedown, it boasted more than 2,000 criminal users, who had used it to deploy over 40,000 fraudulent sites leading to hundreds of thousands of victims worldwide.
The platform offered a number of key benefits to its criminal clientele, including:
- The ability to obtain two-factor authentication (2FA) codes by proxying the connection to the phished organization using Adversary-in-the-Middle (AitM) techniques. This is implemented in a tool called LabRat.
- Phishing pages for several key Canadian, US, and international banks
- Phishing pages for additional services such as Spotify, postal services such as DHL and An Post (the Irish post office), car toll services, insurance providers, and more.
- Highly customizable phishing templates that can request standard name and address information, email, dates of birth, standard security question answers, card numbers, passwords, and PINs.
- The ability to request the creation of bespoke phishing pages for target brands.
- Ease of management, since the platform takes care of most of the tedious tasks in developing and managing phishing page infrastructure; all the malicious actor needs is a virtual private server (VPS) to host the files and from which the platform can automatically deploy.
- Detailed campaign success statistics for criminal users.
- Management of any successfully stolen credentials.
- A popular SMS smishing component, LabSend, that supports customized SMS templates; this greatly eases the distribution of the phishing pages to target victims.
In essence, a PhaaS outsources the traditional task of having to develop and host phishing pages for a target organization, plus having to develop methods to extract stolen details, substantially dropping the barrier for entry to phishing
Note that LabHost was not the only such PhaaS provider — there were many others, such as Frappo and Greatness. Furthermore, there were several red-team tools developed for similar purposes, such as Evilgophish, EvilPhish, and EvilGinx2. However, LabHost was certainly one of the most popular and damaging in the market.
LabHost offered three membership tiers paid via bitcoin:
Standard (US$179 per month). This offered dozens of pages targeting Canadian institutions and hosted of a maximum of three active phishing pages at the same time.
Premium (US$249 per month). In addition to all the features of the Standard tier, Premium offered dozens of pages targeting US institutions and increased the size of its active phishing pages to 20.
World Membership (US$300 per month). The highest tier offered over 70 phishing pages targeting international organizations and added 10 hosted phishing pages (separate to Premium or Standard licenses). These include organizations in Andorra, Argentina, Australia, Austria, Bolivia, Brazil, Colombia, France, Germany, Guatemala, Hong Kong, Ireland, Italy, Netherlands, Luxembourg, Malaysia, Mexico, Netherlands, Poland, Portugal, Russia, Saudi Arabia, South Korea, Spain, Sweden, Turkey, UAE, and Venezuela.
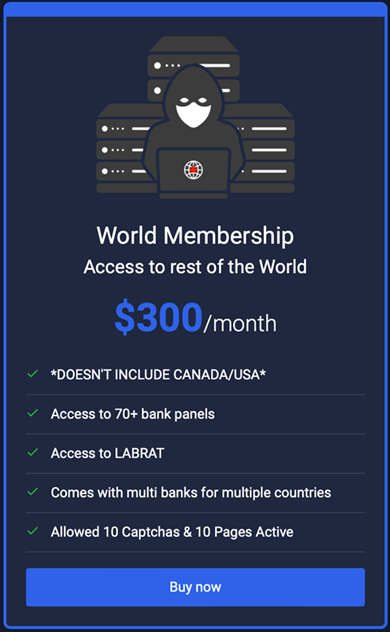
Quarterly and annual subscriptions were also available. In addition, the platform administrators offered technical support services via a dedicated Telegram channel for all service levels.
Example attack flow
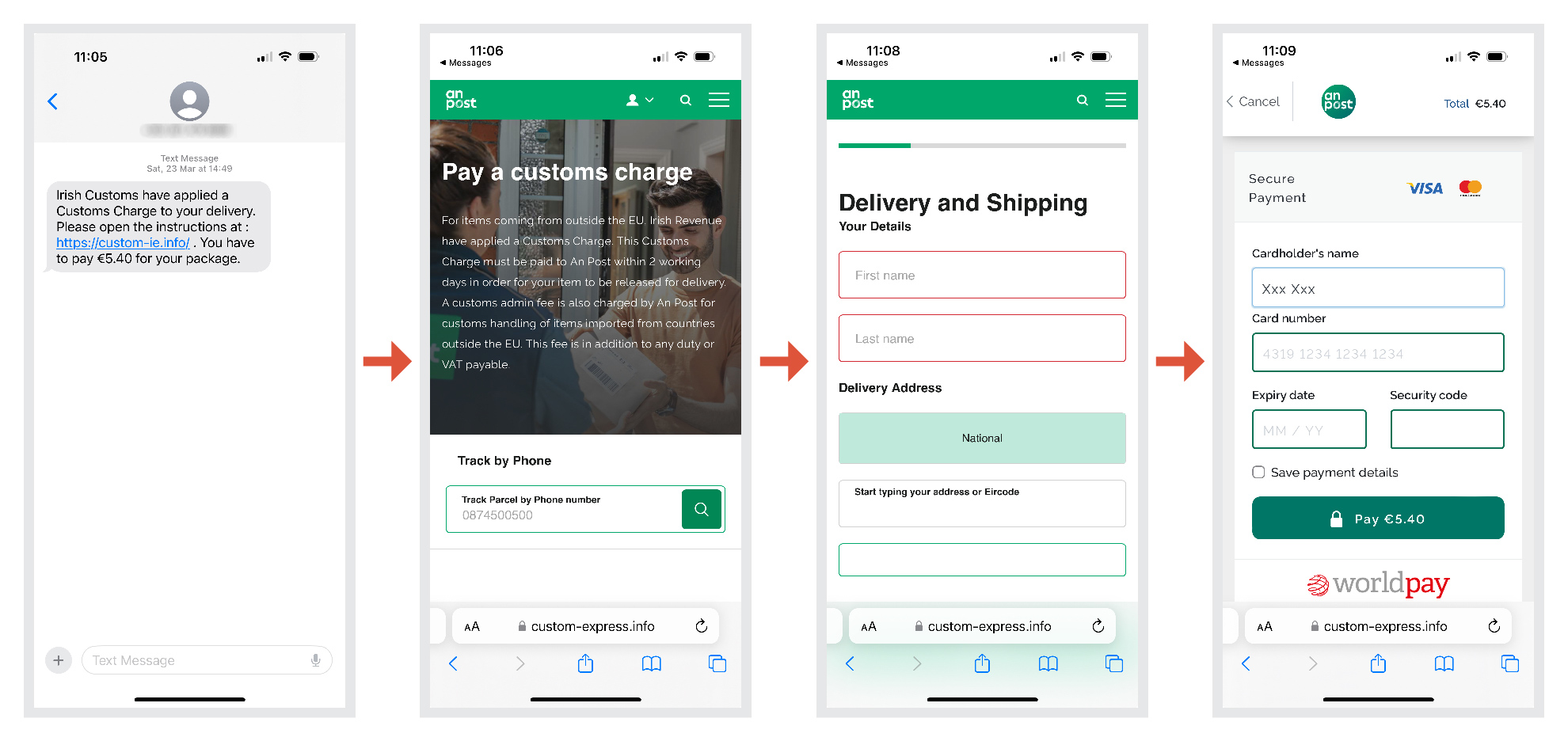
Figure 3 shows an example of a fairly typical attack flow for an SMS-based phishing attack from LabHost, based on the target’s perspective.
The user’s target phone receives an SMS related to a service offered in their country — in this case, it mimicked a customs charge on a posted item to Ireland. Since Ireland is an island nation, it’s not unusual for Irish people who are expecting a parcel from outside of the EU (such as the UK or the US) to receive these kinds of legitimate requests. Other common targeting techniques used against Irish users include local bank or local road toll services, or their equivalents from other countries.
- In this case, the smish would have been sent via the LabSend module of the LabHost platform, likely leveraging a farm of dedicated mobile devices created for this purpose. Note that the fee is set to a small amount to avoid raising suspicion.
- Once the target selects this link, they are directed to a highly convincing page that copies the look and feel of An Post, the Irish postal service and the legitimate entity that normally processes these kinds of customs payments. The user is then prompted to input their phone number; however, in testing, this does not need to match the targeted phone, so it does not function as a safety check.
- Rather than present the user with all the details the attackers wants to gather on one screen (which might trigger suspicion) the attackers break these details up over several screens.
- The fake page initially asks for the user’s name and address (Eircode is a postcode system used in Ireland), then requests classic credit card details, including the security code. Once completed, all these details will be sent via the phishing page (hosted on a user of LabHost’s infrastructure) to the main LabHost panel, with an alert being sent to the cybercriminal user. The user can then simply log in to LabHost and retrieve these details, or export all of the gathered credentials for a given time period.
While this is an example of an attack against an Irish target, a similar attack flow exists using different brands for other regions on both mobile and desktop devices. Mobile devices have an advantage for attackers since they frequently lack installed security software, making users more susceptible to carrying out small transactions on them without practicing due diligence. Such attacks not only negatively affect the target victim but also indirectly affect the impersonated brands themselves, potentially undermining trust and leading them to receive support calls for which they can do little to assist the victim.
What action did law enforcement take?
On Thursday, April 18, 2024, LabHost and all linked fraudulent sites were disrupted by the Metropolitan Police Service and replaced with messages announcing their seizure. This operation was carried out in partnership with the UK’s National Crime Agency, the City of London Police, Europol, Regional Organised Crime Units (ROCUs) across the UK, and other international police forces in close collaboration with trusted private industry organizations.
In addition, from April 14 to April 17, international law enforcement made several arrests related to criminal users of this service. International law enforcement also contacted hundreds more, mentioning that it knew the details of their activities and leaving a warning that they remain under active investigation.
The press release articulates the scale of the service, including the large amount of money earned from it for an approximate period of two and a half years, the number of fraudulent domains created, and the volume of stolen credentials. The removal of this service and several of its key users will yield a significant impact on these types of phishing fraud attacks as a result.
Trend has been assisting in the investigation of LabHost along with the UK’s Metropolitan Police Service since June 2023. During that time we have helped in the following:
- Investigating the infrastructure hosting the criminal service
- Investigating phishing pages associated with users of the service
- Assisting with the triage and clustering of LabHost users
- Launching individual investigations on several key users
This is in keeping with Trend’s guiding mission to make the world safe for the exchange of digital information, for both our customers and non-customers alike. We have been collaborating with law enforcement globally for decades and have formal partnerships with UK law enforcement going back almost 10 years, with several successful operations and arrests. Such partnerships help us not only to proactively protect our customer base with highly timely threat intelligence but also expand that impact to the wider internet userbase.
In taking this action, the Metropolitan Police Service and its partners have helped remove a major player in the phishing ecosystem, weakening the toolkits of malicious actors while also spreading uncertainty among their userbase. This will have an immediate effect on the targets of phishing attacks carried out using the platform, thereby helping to safeguard victims (who would unfortunately receive messages that impersonate legitimate brands) and the affected brands themselves.
We would like to take this opportunity to congratulate the Metropolitan Police Service on its lead role in this operation, its international and local law enforcement partners, and our fellow trusted private industry colleagues on all the hard work that went into this case. We look forward to many continued successful endeavors in the future.
Key indicators
The following are the main landing pages for the now disabled service. Each of these e is proactively blocked by Trend so that our customers are aware if anyone on their network is visiting these sites.
- labhost[.]cc (historical)
- labhost[.]co (historical)
- labhost[.]xyz (historical)
- labhost[.]ru (historical)
- lab-host[.]ru
In addition, the platform was used to generate over 40,000 fraudulent sites with many new phishing URLs added daily for its customer base. Trend protects customers from these URLs using a combination of sourcing and behavioral detection methods, primarily tagging them with the category “PHISHKIT” in our logs.
As mentioned previously, other PhaaS-type services still exist, and we continue to actively monitor and provide protection for ongoing campaigns. For advice on protecting yourself from phishing attacks, please visit our phishing definition page.