- Knowledge Base
- Amazon Web Services
- Amazon Redshift
- Redshift Cluster Encrypted
Ensure that your Amazon Redshift clusters are encrypted in order to meet security and compliance requirements. The Redshift clusters data encryption/decryption is handled transparently by AWS and does not require any additional action from you or your application.
This rule can help you with the following compliance standards:
- PCI
- HIPAA
- APRA
- MAS
- NIST4
For further details on compliance standards supported by Conformity, see here.
This rule can help you work with the AWS Well-Architected Framework.
This rule resolution is part of the Conformity Security & Compliance tool for AWS.
Cloud Conformity strongly recommends implementing encryption when dealing with Redshift clusters that contain sensitive data. Though encryption is an optional, immutable setting within AWS Redshift configuration, you should enable it in order to protect your data from unauthorized access and fulfill compliance requirements for data-at-rest encryption.
Audit
To determine your Amazon Redshift clusters encryption status, perform the following:
Using AWS Console
01 Login to the AWS Management Console.
02 Navigate to Redshift dashboard at https://console.aws.amazon.com/redshift/.
03 In the left navigation panel, under Redshift Dashboard, click Clusters.
04 Choose the Redshift cluster that you want to examine then click on its identifier (name) link:
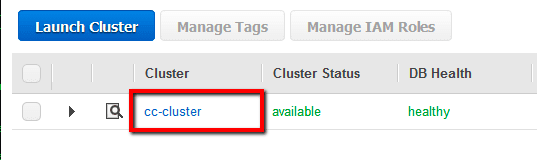
listed in the Cluster column.
05 On the selected cluster configuration page, in the Cluster Database Properties section, verify the Encrypted property status:
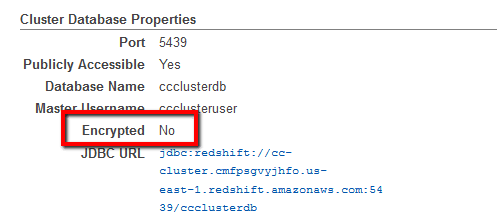
If the current status value is set to No, the selected Amazon Redshift cluster is not encrypted, therefore your Redshift data-at-rest is not protected in case of unauthorized access.
06 Repeat step no. 4 and 5 to verify the encryption status for other clusters provisioned in the current region.
07 Change the AWS region from the navigation bar and repeat the audit process for other regions.
Using AWS CLI
01 Run describe-clusters command (OSX/Linux/UNIX) using custom query filters to list the identifiers (names) of all Redshift clusters currently available in the selected region:
aws redshift describe-clusters --region us-east-1 --output table --query 'Clusters[*].ClusterIdentifier'
02 The command output should return a table with the requested cluster names:
---------------------- | DescribeClusters | +--------------------+ | cc-cluster | | bdu-cluster | | bde-cluster | +--------------------+
03 Run again describe-clusters command (OSX/Linux/UNIX) using the name of cluster that you want to examine as identifier and the necessary query filters to expose the encryption status for the selected AWS Redshift cluster:
aws redshift describe-clusters --region us-east-1 --cluster-identifier cc-cluster --query 'Clusters[*].Encrypted'
04 The command output should return the cluster encryption status (true for encrypted and false for unencrypted):
[
false
]
If the returned value is false, the selected Amazon Redshift cluster is not encrypted.
05 Repeat step no. 3 and 4 for each Redshift cluster available in the current region.
06 Change the AWS region by updating the --region command parameter value and repeat steps no. 1 - 5 to perform the audit process for other regions.
Remediation / Resolution
To encrypt an existing Redshift cluster you must unload the data from it to Amazon S3 then load this data in a new cluster with the chosen encryption setting, configuration settings that gives you have have the ability to choose the encryption key. There are two types of encryption keys - the default KMS key which is managed by AWS and the KMS Customer Managed Key (CMK) which is managed by the customer (you). The encryption key type used in this rule is default KMS (AWS-managed key). To set up the new Redshift cluster, enable encryption, and move your existing cluster data to it, perform the following:
Using AWS Console
01 Login to the AWS Management Console.
02 Navigate to Redshift dashboard at https://console.aws.amazon.com/redshift/.
03 In the left navigation panel, under Redshift Dashboard, click Clusters.
04 Click Launch Cluster button from the dashboard top menu to start the cluster setup process.
05 On the Cluster Details configuration page, enter a unique name for your new cluster in the Cluster Identifier field and fill out the rest of the fields available on this page with the information taken from your existing (unencrypted) cluster.
06 Click the Continue button to continue the setup process.
07 On the Node Configuration page, select the appropriate node type for the new cluster from the Node Type dropdown list and configure the number of nodes used to match the existing (unencrypted) cluster configuration.
08 Click Continue to carry on with the process.
09 On the Additional Configuration page, in the first configuration section, select KMS next to Encrypt Database. Choose (default) aws/redshift option from the Master Key dropdown list to encrypt the new cluster using the default master key provided and managed by AWS. The default master key is an AWS-managed key that is created automatically for Redshift clusters within your AWS account. Configure the rest of the options available on the page such as availability zone, VPC security group(s) and associated IAM role in order to reflect the unencrypted cluster configuration.
10 Click Continue to load the next page.
11 On the Review page, review the cluster properties, its database details, the security and encryption configuration, then click Launch Cluster to build the new (encrypted) AWS Redshift cluster.
12 On the confirmation page click Close to return to the Redshift dashboard. Once the Cluster Status value changes to available and the DB Health status changes to healthy, the new cluster can used to load the existing data.
13 Now unload your data from the unencrypted Redshift cluster and reload it into the newly created cluster using the Amazon Redshift Unload/Copy utility. With this utility tool you can unload (export) your data from the unencrypted cluster (source) to an AWS S3 bucket, encrypt it, then import the data into your new cluster (destination) and clean up the S3 bucket used. All the necessary instructions to install, configure and use the Amazon Redshift Unload/Copy tool can be found at this URL.
14 As soon as the migration process is completed and all the data is loaded into your new (encrypted) Redshift cluster, you can update your application configuration to refer to the new cluster endpoint:

15 Once the Redshift cluster endpoint is changed within your application configuration, you can remove the unencrypted cluster from your AWS account by performing the following actions:
- In the navigation panel, under Redshift Dashboard, click Clusters.
- Choose the Redshift cluster that you want to remove then click on its identifier link listed in the Cluster column.
- On the selected cluster Configuration tab, click the Cluster dropdown button from the dashboard main menu then select Delete from the dropdown list:
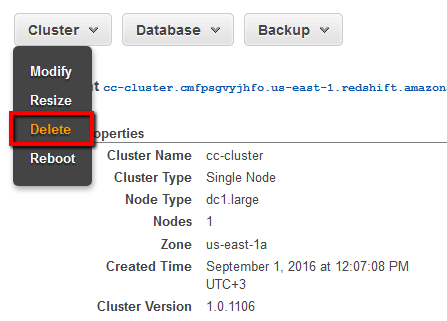 .
. - Inside the Delete Cluster dialog box, enter a unique name for the final snapshot in the Snapshot name box then click Delete to confirm the action. Once the snapshot is created the unencrypted cluster removal process begins.
16 Repeat steps no. 4 - 15 to enable data-at-rest encryption for other Redshift clusters launched in the current region.
17 Change the AWS region from the navigation bar and repeat the entire process for other regions.
Using AWS CLI
01 Run describe-clusters command (OSX/Linux/UNIX) to describe the configuration available for the selected unencrypted Redshift cluster:
aws redshift describe-clusters --region us-east-1 --cluster-identifier cc-cluster
02 The command output should return the requested configuration information which will be useful later when the new Redshift cluster will be created:
{
"Clusters": [
{
"PubliclyAccessible": true,
"MasterUsername": "ccclusteruser",
"VpcSecurityGroups": [
{
"Status": "active",
"VpcSecurityGroupId": "sg-58dc0a22"
}
],
"ClusterPublicKey": "ssh-rsa AAAAB3Nz46D5XtMr ... ",
"NumberOfNodes": 1,
"PendingModifiedValues": {},
"VpcId": "vpc-2fb56548",
"ClusterVersion": "1.0",
"Tags": [],
"AutomatedSnapshotRetentionPeriod": 1,
"ClusterParameterGroups": [
{
"ParameterGroupName": "default.redshift-1.0",
"ParameterApplyStatus": "in-sync"
}
],
"DBName": "ccclusterdb",
"PreferredMaintenanceWindow": "sun:06:00-sun:06:30",
"Endpoint": {
"Port": 5439,
"Address": "cc-cluster.cmfpsgvyjhfo.us-east-1 ... "
},
"IamRoles": [],
"AllowVersionUpgrade": true,
"ClusterCreateTime": "2016-09-01T12:24:54.550Z",
"ClusterSubnetGroupName": "default",
"ClusterSecurityGroups": [],
"ClusterIdentifier": "cc-cluster",
"ClusterNodes": [
{
"NodeRole": "SHARED",
"PrivateIPAddress": "172.31.9.165",
"PublicIPAddress": "54.55.80.231"
}
],
"AvailabilityZone": "us-east-1a",
"NodeType": "dc1.large",
"Encrypted": false,
"ClusterRevisionNumber": "1101",
"ClusterStatus": "available"
}
]
}
03 Run create-cluster command (OSX/Linux/UNIX) using the existing (unencrypted) cluster configuration details returned at the previous step to create a new Amazon Redshift cluster with the encryption feature enabled. The new cluster will be launched with the default master key used for data-at-rest encryption which is basically an AWS-managed key that is generated automatically for the Redshift service when you create your AWS account:
aws redshift create-cluster --region us-east-1 --cluster-identifier cc-cluster-encrypted --cluster-type single-node --node-type dc1.large --db-name ccclusterdb --master-username ccclusteruser --master-user-password CCclusterpwd0 --vpc-security-group-ids sg-58dc0a22 --availability-zone us-east-1a --port 5439 --cluster-subnet-group-name default --cluster-parameter-group-name default.redshift-1.0 --automated-snapshot-retention-period 1 --publicly-accessible --allow-version-upgrade --encrypted
04 The command output should return the new cluster configuration metadata:
{
"Cluster": {
"PubliclyAccessible": true,
"MasterUsername": "ccclusteruser",
"VpcSecurityGroups": [
{
"Status": "active",
"VpcSecurityGroupId": "sg-58dc0a22"
}
],
"NumberOfNodes": 1,
"PendingModifiedValues": {
"MasterUserPassword": "****"
},
"VpcId": "vpc-2fb56548",
"ClusterVersion": "1.0",
"Tags": [],
"AutomatedSnapshotRetentionPeriod": 1,
"ClusterParameterGroups": [
{
"ParameterGroupName": "default.redshift-1.0",
"ParameterApplyStatus": "in-sync"
}
],
"DBName": "ccclusterdb",
"PreferredMaintenanceWindow": "fri:06:00-fri:06:30",
"IamRoles": [],
"AllowVersionUpgrade": true,
"ClusterSubnetGroupName": "default",
"ClusterSecurityGroups": [],
"ClusterIdentifier": "cc-cluster-encrypted",
"AvailabilityZone": "us-east-1a",
"NodeType": "dc1.large",
"Encrypted": true,
"KmsKeyId": "arn:aws:kms:us-east-1:123456789012:key/
4302e0f2-ec36-4f3c-806a-89f454193a47",
"ClusterStatus": "creating"
}
}
05 Run again describe-clusters command (OSX/Linux/UNIX) using the appropriate query filters to expose the new Redshift cluster endpoint:
aws redshift describe-clusters --region us-east-1 --cluster-identifier cc-cluster-encrypted --query 'Clusters[*].Endpoint.Address'
06 The command output should return the new cluster endpoint URL:
[
"cc-cluster-encrypted.cmfpsgvyjhfo.us-east-1.redshift.amazonaws.com"
]
07 Now unload your data from the unencrypted Redshift cluster and reload it in the one created at the previous step by using the Amazon Redshift Unload/Copy utility. With this utility tool you can export your data from the unencrypted cluster (source) to an AWS S3 bucket, encrypt it, then import the data into your new Redshift cluster (destination) and remove the S3 bucket used. The necessary instructions to install, configure and use the Amazon Redshift Unload/Copy tool can be found on this page.
08 As soon as the transfer is completed and all the data is loaded into your new (encrypted) cluster, you can update your application configuration to point to the new AWS Redshift cluster endpoint address returned at step no. 6.
09 Once the Redshift cluster endpoint is changed within your application configuration, run delete-cluster command (OSX/Linux/UNIX) to remove the unencrypted cluster from your AWS account:
aws redshift delete-cluster --region us-east-1 --cluster-identifier cc-cluster --final-cluster-snapshot-identifier cc-cluster-finalsnapshot
10 The command output should return the metadata of the cluster selected for deletion:
{
"Cluster": {
"PubliclyAccessible": true,
"MasterUsername": "ccclusteruser",
"VpcSecurityGroups": [
{
"Status": "active",
"VpcSecurityGroupId": "sg-58dc0a22"
}
],
"NumberOfNodes": 1,
"PendingModifiedValues": {},
"VpcId": "vpc-2fb56548",
"ClusterVersion": "1.0",
"Tags": [],
"AutomatedSnapshotRetentionPeriod": 1,
"ClusterParameterGroups": [
{
"ParameterGroupName": "default.redshift-1.0",
"ParameterApplyStatus": "in-sync"
}
],
"DBName": "ccclusterdb",
"PreferredMaintenanceWindow": "sun:06:00-sun:06:30",
"Endpoint": {
"Port": 5439,
"Address": "cc-cluster.cmfpsgvyjhfo.us-east-1 ... "
},
"IamRoles": [],
"AllowVersionUpgrade": true,
"ClusterCreateTime": "2016-09-01T12:24:54.550Z",
"ClusterSubnetGroupName": "default",
"ClusterSecurityGroups": [],
"ClusterIdentifier": "cc-cluster",
"AvailabilityZone": "us-east-1a",
"NodeType": "dc1.large",
"Encrypted": false,
"ClusterStatus": "final-snapshot"
}
}
11 Repeat steps no. 1 - 10 to enable encryption for other Amazon Redshift clusters provisioned in the current region.
12 Change the AWS region by updating the --region command parameter value and repeat steps no. 1 - 11 for other regions.
References
- AWS Documentation
- Amazon Redshift FAQs
- Amazon Redshift Clusters
- Managing Clusters Using the Console
- Manage Clusters Using the Amazon Redshift CLI and API
- Amazon Redshift Database Encryption
- AWS Command Line Interface (CLI) Documentation
- redshift
- describe-clusters
- create-cluster
- delete-cluster
